Compliance Monitoring is the ongoing process of verifying that an organization's systems, processes, and people continuously adhere to regulatory requirements, internal policies, and industry standards — not just at audit time, but every day. For cloud-native and regulated businesses in 2026, it is the difference between a clean audit and a costly breach.
What is Compliance Monitoring?
Compliance monitoring is the systematic, continuous practice of evaluating whether an organization's operations, systems, and people conform to the laws, regulations, and internal standards that govern them. Unlike a one-time audit, compliance monitoring runs as an always-on feedback loop — collecting evidence, flagging exceptions, and enabling rapid remediation before regulators ever knock on the door.
The practice is critical across heavily regulated industries:
Healthcare — HIPAA, HITECH, 21 CFR Part 11
Finance & Banking — PCI DSS, SOX, Basel III, MiFID II
Cloud & SaaS — SOC 2, ISO 27001, CSA CCM
EU-regulated entities — GDPR, NIS2, DORA
Energy & Utilities — NERC CIP, ISO 50001
Pharmaceuticals — GxP, FDA 21 CFR
💡 In short: Compliance monitoring is your organization's immune system. Audits are the annual check-up. Monitoring is what keeps you healthy between check-ups.
Why Compliance Monitoring Matters in 2026
Regulatory landscapes have never moved faster. GDPR fines reached record highs in 2024–2025, NIS2 entered enforcement mode across the EU, and DORA (Digital Operational Resilience Act) took effect for financial entities. Meanwhile, cloud adoption has created entirely new attack surfaces that traditional point-in-time audits simply cannot cover.
Risk Without MonitoringTypical Business ImpactProbability (unmonitored)Undetected misconfigured S3 bucket / cloud storageData breach, regulatory fine, brand damageHighStale privileged access not reviewedInsider threat, audit failure, SOX violationVery HighMissing audit log retentionInability to prove compliance, automatic audit failureHighBackup not testedUnrecoverable data loss, SLA breach, recovery failureMediumUnpatched critical CVE beyond SLAExploitable vulnerability, CVSS breach, PCI non-complianceHighWhy Compliance Monitoring Matters in 2026
Strong compliance monitoring builds trust with enterprise clients and partners, significantly reduces audit preparation time, and enables a proactive risk posture instead of a reactive, fire-fighting one.
Compliance Monitoring vs Compliance Audit vs Compliance Management
These three terms are often used interchangeably but they describe distinct activities that work together. Understanding the difference helps organizations allocate resources correctly.
DimensionCompliance MonitoringCompliance AuditCompliance ManagementFrequencyContinuous / near-real-timePeriodic (annual, quarterly)Ongoing governancePurposeDetect & alert on deviationsFormal independent assessmentPolicies, training, cultureOutputAlerts, dashboards, exception logsAudit report, findings, attestationPolicies, procedures, risk registerWho leadsEngineering / Security / DevOpsInternal audit / Third-party auditorCompliance Officer / GRC teamAnalogyBlood pressure cuff worn dailyAnnual physical with doctorHealthy lifestyle programCompliance Monitoring vs Compliance Audit vs Compliance Management
✅ Monitoring answers
Is MFA enforced right now?
Are all logs being retained?
Did anything change in IAM this week?
Are backups completing successfully?
Is encryption enabled on all storage?
📋 Auditing answers
Were controls effective over the period?
Did evidence satisfy the framework?
What is the organization's control maturity?
What formal findings require remediation?
Is the organization SOC 2 / ISO 27001 ready?
Explore our Compliance Audit services
The 7-Step Compliance Monitoring Process
Effective compliance monitoring is not a single tool or dashboard — it's a disciplined cycle. Here is the process Gart uses when setting up or maturing a client's compliance monitoring program:
1. Define Scope & Applicable Frameworks
Identify which regulations, standards, and internal policies apply. Map your systems, data flows, and third-party integrations to determine the monitoring perimeter. Ambiguous scope is the most common reason monitoring programs fail.
2. Inventory Systems & Controls
Catalogue all assets (cloud, on-prem, SaaS, CI/CD pipelines) and map each one to a control objective. Assign control owners. Without ownership, no one acts when an exception fires.
3. Define Evidence Collection Rules
For each control, specify what constitutes "evidence of compliance" — a log entry, a configuration state, a test result, a screenshot, or a signed document. Define collection frequency (real-time, daily, monthly) and acceptable format for auditors.
4. Instrument & Automate Collection
Deploy monitoring agents, SIEM rules, cloud policy engines (AWS Config, Azure Policy, GCP Security Command Center), and IaC scanning tools. Automate evidence collection wherever possible — manual evidence gathering at audit time is a costly, error-prone anti-pattern.
5. Monitor Exceptions & Triage Alerts
Create alert thresholds for control deviations. Not every alert is a breach — build a triage process that separates noise from genuine risk. Route high-priority exceptions to security/engineering immediately; lower-priority items to a weekly review queue.
6. Prioritize Risks & Remediate
Score exceptions by likelihood and impact. Maintain a risk register that tracks open findings, owners, and target remediation dates. Escalate unresolved critical findings to leadership with a clear business-impact framing.
7. Re-test, Report & Continuously Improve
After remediation, re-test the control to confirm it is effective. Produce compliance health reports for leadership and auditors. Run a quarterly retrospective to tune alert thresholds and update monitoring scope as regulations and infrastructure evolve.
Key Controls & Evidence to Monitor
Across hundreds of compliance engagements, the controls below consistently appear on auditor checklists. These are the areas where automated compliance monitoring delivers the highest return:
Control AreaWhat to MonitorEvidence Auditors WantRelevant FrameworksIdentity & Access (IAM)Privileged role assignments, inactive accounts, MFA status, service account permissionsAccess review logs, MFA adoption rate, least-privilege config exportsSOC 2, ISO 27001, HIPAAAudit LoggingLog completeness, retention period, tamper-evidence, SIEM ingestion healthLog retention policy, SIEM dashboard, CloudTrail / Audit Log exportsPCI DSS, SOX, NIS2, GDPREncryptionData-at-rest encryption on storage, TLS version on endpoints, key rotation schedulesEncryption config exports, key management audit logs, TLS scan reportsPCI DSS, HIPAA, GDPR, ISO 27001Patch ManagementCVE scan results, SLA adherence per severity, open critical/high vulnerabilitiesScan reports, patch cadence logs, SLA compliance metricsSOC 2, PCI DSS, ISO 27001Backup & RecoveryBackup job success rate, RPO/RTO test results, offsite replication statusBackup logs, recovery test records, DR test reportsSOC 2, ISO 22301, DORA, NIS2Vendor / Third-Party AccessActive vendor sessions, access scope, contract/NDA currency, SOC 2 report datesVendor access logs, contract register, third-party risk assessmentsISO 27001, SOC 2, GDPR, NIS2Network & PerimeterFirewall rule changes, open ports, egress filtering, WAF alert volumesFirewall config snapshots, IDS/IPS logs, pen test reportsPCI DSS, SOC 2, NIS2Incident ResponseMean time to detect (MTTD), mean time to respond (MTTR), breach notification timelinesIncident logs, CSIRT reports, post-mortemsGDPR (72h), NIS2, HIPAA, DORAKey Controls & Evidence to Monitor
Continuous Compliance Monitoring for Cloud Environments
Cloud infrastructure changes constantly — teams spin up resources, update IAM policies, and deploy code multiple times per day. This makes continuous compliance monitoring not a nice-to-have but a fundamental requirement. Manual checks against cloud state are obsolete before the ink dries.
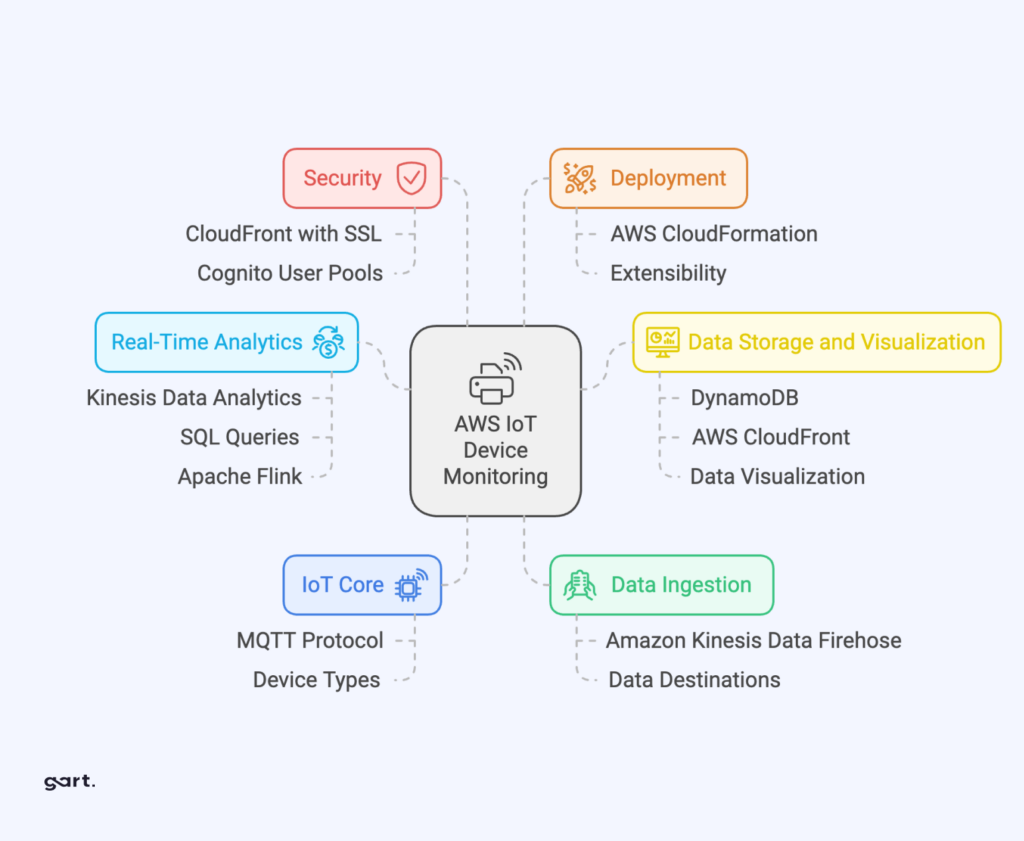
AWS Compliance Monitoring — Key Automated Checks
AWS Config Rules — detect non-compliant resources in real time (e.g., unencrypted EBS volumes, public S3 buckets, missing CloudTrail)
AWS Security Hub — aggregates findings from GuardDuty, Inspector, Macie into a single compliance posture score
CloudTrail + Athena — query audit logs for unauthorized IAM changes, API calls outside approved regions
IAM Access Analyzer — surfaces external access to resources and unused roles/permissions
Azure Compliance Monitoring — Key Automated Checks
Azure Policy & Defender for Cloud — enforce and score compliance against CIS, NIST SP 800-53, ISO 27001 benchmarks
Microsoft Purview — data classification, governance, and audit trail across Azure and M365
Azure Monitor + Sentinel — SIEM-class alerting on suspicious activity with compliance-relevant playbooks
Privileged Identity Management (PIM) — just-in-time access with mandatory justification and approval workflows
GCP Compliance Monitoring — Key Automated Checks
Security Command Center — organization-wide misconfiguration detection and compliance benchmarking
VPC Service Controls — perimeter security policies that prevent data exfiltration
Cloud Audit Logs — immutable, per-service activity and data access logs
Policy Intelligence — recommends IAM role right-sizing based on actual usage data
🔗
For authoritative cloud security benchmarks, the CIS Benchmarks provide configuration baselines for AWS, Azure, GCP, Kubernetes, and 100+ other platforms — an industry-standard starting point for any cloud compliance monitoring program.
See Gart's Cloud Computing & Security services
Industry-Specific Compliance Monitoring Frameworks
Compliance monitoring requirements differ significantly by industry and geography. Below are the frameworks Gart's clients most commonly monitor against, along with the controls that require continuous (not just periodic) monitoring.
FrameworkIndustry / RegionKey Continuous Monitoring RequirementsResourcesISO 27001Global / All industriesAccess control review, log management, vulnerability scanning, supplier reviewISO.orgSOC 2 Type IISaaS / TechnologyContinuous availability, logical access, change management, incident responseAICPAHIPAAHealthcare (US)ePHI access logs, encryption at rest/transit, workforce activity auditsHHS.govPCI DSS v4.0Payment / E-commerceReal-time network monitoring, file integrity monitoring, quarterly vulnerability scansPCI SSCNIS2EU / Critical sectorsIncident detection within 24h, risk assessments, supply chain security checksENISAGDPREU / Global processing EU dataData subject request tracking, breach detection (<72h notification), processor auditsGDPR.euIndustry-Specific Compliance Monitoring Frameworks
How to prepare for a HIPAA Audit - Gart's PCI DSS Audit guide
First-Hand Experience
What We Usually Find During Compliance Monitoring Reviews
After reviewing postures across dozens of regulated environments, these are the patterns we encounter repeatedly — regardless of organization size.
👥
Incomplete or stale access reviews
Former employees and service accounts with active permissions weeks after departure. IAM hygiene is rarely automated, and reviews are often rubber-stamped.
📋
Missing backup test evidence
Backups appear healthy, but nobody has tested a restore in 6–18 months. Auditors want dated restore test logs with RPO/RTO outcomes, not just success metrics.
📊
Fragmented or incomplete audit logs
Gaps in the log chain (like disabled S3 data-event logging) make it impossible to reconstruct an incident or prove that one didn't happen.
🔔
Alert fatigue masking real issues
Thousands of low-fidelity alerts lead teams to mute notifications or build exceptions, inadvertently disabling detection for real threats.
📄
Policy-to-implementation gaps
Written policies say "encryption required," but reality reveals unencrypted legacy buckets. Continuous monitoring is the only way to detect this drift.
🔧
Automation is first patched, last monitored
CI/CD pipelines move faster than human reviewers. IaC repositories often lack policy-as-code scanning, leaving non-compliant resources active for months.
Featured Success Story
Case study: ISO 27001 compliance for Spiral Technology
→
Compliance Monitoring Tools & Automation
The right tooling depends on your stack, frameworks, and team maturity. Most organizations use a layered approach rather than a single platform:
CategoryRepresentative ToolsBest ForCloud Security Posture Management (CSPM)AWS Security Hub, Wiz, Prisma Cloud, Orca Security, Defender for CloudCloud misconfiguration detection, continuous benchmarkingSIEM / Log ManagementSplunk, Elastic SIEM, Microsoft Sentinel, Datadog SecurityLog correlation, anomaly detection, audit evidenceGRC PlatformsVanta, Drata, Secureframe, ServiceNow GRC, OneTrustEvidence collection automation, audit-ready reportingPolicy-as-Code / IaC ScanningOpen Policy Agent (OPA), Checkov, Terrascan, tfsec, ConftestPrevent non-compliant infrastructure from being deployedVulnerability ManagementTenable Nessus, Qualys, AWS Inspector, Trivy (containers)CVE detection, patch SLA monitoring, container scanningIdentity GovernanceSailPoint, CyberArk, Azure PIM, AWS IAM Access AnalyzerAccess reviews, least-privilege enforcement, PAM
⚠️ Tool sprawl is a compliance risk: More tools mean more integrations to maintain, more alert queues to manage, and more places where evidence can fall through the cracks. Start with native cloud tools and expand deliberately. The Linux Foundation and CNCF maintain open-source compliance tooling for cloud-native environments worth evaluating before adding commercial licenses.
Compliance Monitoring Best Practices
1. Shift compliance left into the development pipeline
The cheapest time to catch a compliance violation is before the resource is deployed. Integrate policy-as-code scanning (OPA, Checkov) into your CI/CD pipeline so that non-compliant Terraform or Helm charts never reach production. Treat compliance failures as build-breaking errors, not post-deploy recommendations.
2. Automate evidence collection — not just detection
Detection without evidence collection is useless at audit time. Configure your monitoring tools to export and archive compliance evidence (configuration snapshots, access review logs, scan reports) automatically to an immutable store. Auditors need evidence from a defined period — not a screenshot taken the morning of the audit.
3. Assign control owners, not just tool owners
Every control needs a named human owner who is accountable for exceptions. When an alert fires that MFA is disabled on a privileged account, "the security team" is not a sufficient owner — a specific person must be on call to investigate and remediate within the SLA.
4. Tune alerts ruthlessly to eliminate fatigue
Compliance monitoring programs that generate thousands of daily alerts quickly become ignored. Start with a small set of high-fidelity, high-impact alerts. Expand incrementally after each is tuned to near-zero false positive rates. A team that responds to 20 real alerts per day is more secure than one drowning in 2,000 noisy ones.
5. Monitor your monitoring
Monitoring pipelines break silently. Log shippers stop, API rate limits are hit, SIEM ingestion queues fill up. Build meta-monitoring to detect when evidence collection or alerting pipelines have gaps — and treat those gaps as compliance findings in their own right.
6. Conduct a quarterly compliance posture review
Beyond continuous automated monitoring, schedule a quarterly human review of the compliance posture. Review open exceptions, re-assess risk scores, retire obsolete controls, and update monitoring scope to cover new systems and regulatory changes.
Compliance Monitoring Checklist for Cloud Teams
A starting point for cloud-first compliance. Each item requires a named owner, a monitoring cadence, and a defined evidence artifact.
✓
MFA enforced on all privileged and administrative accounts
✓
Access reviews completed for all privileged roles (minimum quarterly)
✓
Service accounts audited for least-privilege and no unused permissions
✓
Audit logging enabled and retained (90 days min; 1 year for PCI/HIPAA)
✓
SIEM ingestion health monitored — no silent log gaps
✓
Data-at-rest encryption confirmed on all storage (S3, RDS, EBS, blobs)
✓
TLS 1.2+ enforced; TLS 1.0/1.1 disabled on all endpoints
✓
Encryption key rotation scheduled and verified
✓
Vulnerability scans run weekly; critical/high CVEs remediated within SLA
✓
Patch management SLA compliance tracked and reported
✓
Backups verified complete daily; restore tests documented quarterly
✓
DR test completed at least annually; RPO/RTO outcomes logged
✓
No public cloud storage buckets without explicit business justification
✓
Firewall change log reviewed; unauthorized rule changes alerting
✓
Vendor/third-party access scoped, time-limited, and reviewed quarterly
✓
Incident response plan tested; MTTD and MTTR tracked
✓
Policy-as-code scans integrated into CI/CD pipelines
✓
Compliance evidence archived in immutable storage for audit period
✓
Monitoring pipeline health checked — no silent collection failures
✓
Quarterly posture review conducted with named control owners
Gart Solutions · Compliance Monitoring Services
How Gart Helps You Build a Continuous Compliance Monitoring Program
We work with CTOs, CISOs, and engineering leaders to design, implement, and run compliance monitoring programs that hold up under real auditor scrutiny — not just on paper.
🗺️
Scope & Framework Mapping
We identify applicable frameworks (ISO 27001, SOC 2, HIPAA, PCI DSS, NIS2, GDPR) and map your cloud infrastructure to each control objective.
🔧
Monitoring Setup & Automation
We deploy CSPM tools, SIEM rules, and policy-as-code pipelines — so evidence is collected automatically, not manually on audit day.
📊
Gap Analysis & Risk Register
We deliver a clear view of your current compliance posture, prioritized by risk, with a remediation roadmap and accountable owners.
🔄
Ongoing Reviews & Readiness
Monthly exception reviews and pre-audit evidence packages — so you're never scrambling the week before an official audit.
☁️
Cloud-Native Expertise
AWS, Azure, GCP, Kubernetes, and CI/CD. We speak infrastructure as code and translate compliance into DevOps workflows.
📋
Audit-Ready Deliverables
Exception logs, risk matrices, and control evidence archives. Everything formatted for the specific framework you're being audited against.
Get a Compliance Audit
Talk to an Expert
Fedir Kompaniiets
Co-founder & CEO, Gart Solutions · Cloud Architect & DevOps Consultant
Fedir is a technology enthusiast with over a decade of diverse industry experience. He co-founded Gart Solutions to address complex tech challenges related to Digital Transformation, helping businesses focus on what matters most — scaling. Fedir is committed to driving sustainable IT transformation, helping SMBs innovate, plan future growth, and navigate the "tech madness" through expert DevOps and Cloud managed services. Connect on LinkedIn.

Cybersecurity monitoring — threat detection and response framework
Cybersecurity monitoring is the continuous process of collecting, correlating, and acting on security signals across your entire technology environment. For CTOs and engineering leaders, it is no longer optional: the IBM Cost of a Data Breach 2024 report shows that organisations without mature monitoring take an average of 194 days to identify a breach and a further 64 days to contain it — at an average cost of $4.88 million per incident.
This guide covers everything you need to build or improve a cybersecurity monitoring programme: the foundational concepts, every tool type, a metrics benchmark table, a 30/60/90-day implementation plan, and honest advice from Gart's delivery teams on where organisations most commonly fail.
Executive Summary — 6 key takeaways
01
Cybersecurity monitoring = continuous collection + correlation + analysis of security telemetry, 24/7.
02
The average breach goes undetected for 194 days (IBM 2024). Every day of dwell time adds to remediation cost.
03
Core tooling stack: SIEM + EDR/XDR + IDS/IPS + CSPM + identity monitoring. No single tool covers everything.
04
In our projects, the biggest issue is rarely tool choice — it is signal quality: mapping events to assets and owners.
05
In-house SOC and managed MDR each suit different levels. A hybrid model often delivers the best cost-to-coverage ratio.
06
Organisations with mature monitoring save an average of $1.76 million per breach compared to those without (IBM 2024).
What is Cybersecurity Monitoring?
Cybersecurity monitoring is the continuous collection, correlation, and analysis of security telemetry across endpoints, identities, cloud workloads, networks, and applications to detect threats early and trigger a structured, timely response.
Unlike a one-time security audit, cybersecurity monitoring is an always-on operational capability. It transforms raw data — logs, network flows, authentication events, cloud configuration states — into actionable intelligence that security teams can act on before damage spreads.
NIST defines Information Security Continuous Monitoring (ISCM) as "maintaining ongoing awareness of information security, vulnerabilities, and threats to support organisational risk management decisions." The practical meaning: monitoring is not a product you buy — it is a programme you build and continuously improve.
Three things make cybersecurity monitoring distinct from general IT monitoring:
Security intent: it focuses on adversarial behaviour, not just performance or availability.
Cross-domain correlation: it connects signals from endpoints, identity, network, and cloud — because modern attacks traverse all of them.
Response integration: detection without a structured response workflow creates noise, not security.
Why Cybersecurity Monitoring Matters for Modern Businesses
194
Average days to identify a breach
IBM Cost of a Data Breach, 2024
64
Additional days to contain it
IBM, 2024
$4.88M
Average total breach cost
IBM, 2024
Modern infrastructure is not a perimeter — it is a patchwork of cloud services, SaaS applications, remote endpoints, third-party APIs, and CI/CD pipelines. Attackers exploit this complexity: they move laterally over weeks, escalate privileges quietly, and exfiltrate data long before triggering any obvious alarm.
Organisations that discover incidents through customer complaints, ransomware notes, or regulatory notifications have already lost the containment window. Cybersecurity monitoring shifts the model from reactive discovery to proactive detection.
Three business realities make it non-negotiable in 2026:
Regulatory mandates: GDPR, HIPAA, PCI-DSS, NIS2, SOC 2 Type II, and ISO 27001 all require demonstrable evidence of continuous security oversight. Monitoring provides the audit trail.
Attack surface growth: Every new SaaS integration, cloud account, and remote worker adds potential entry points that a periodic scan cannot keep pace with.
Cyber-insurance requirements: Insurers increasingly require proof of active monitoring capabilities as a condition of coverage or favourable premiums.
The "Boom" Event & Proactive Threat Hunting
In security operations, the "boom" is the moment a breach executes — ransomware activates, data exfiltrates, or systems are compromised. This framing divides the security timeline into two distinct operational phases:
← Left of Boom
The attacker's preparation phase. Your detection window.
Phishing & credential harvesting
Initial access via unpatched CVEs
Lateral movement across the network
Privilege escalation attempts
Persistence mechanisms installed
Right of Boom →
Breach has happened. Goal: detect, contain, recover.
Active data exfiltration underway
Ransomware encryption begins
Command-and-control comms established
Evidence destruction attempts
Regulatory notification windows open
The goal of cybersecurity monitoring is to compress the window between an attacker's first action and your detection — ideally catching the breach left of boom, before the destructive payload executes.
Threat Hunting: Proactively Identifying Risks
Threat hunting is the proactive, human-led search for adversarial activity that automated tools have not yet flagged. Hunters use two primary signal types:
Indicators of Compromise (IOCs): Forensic artefacts left by attackers — unusual login times, unauthorised file access, known malicious IP addresses.
Indicators of Attack (IOAs): Behavioural signals that an attack is in progress — unusual data transfers, lateral movement between hosts, memory injection patterns.
Core tooling for threat hunting includes XDR (cross-domain telemetry correlation), SIEM (event aggregation and rule-based alerting), and UBA (User Behaviour Analytics, which surfaces compromised accounts and malicious insiders based on behavioural baselines).
Core Components of a Cybersecurity Monitoring Programme
No single tool provides complete coverage. A mature programme integrates several complementary layers that together form a full detection-to-response pipeline:
📥
Log Collection
🔗
SIEM Correlation
🚨
Alert Triage
🔍
Investigation
🛡️
Containment
✅
Recovery
Log Collection & Aggregation
Security telemetry must be collected from every relevant source: servers, endpoints, firewalls, cloud services, identity providers, applications, and network devices. Without broad log coverage, downstream correlation is guesswork. Key standards: NIST 800-92 and CISA log-management guidance.
SIEM (Security Information and Event Management)
The correlation engine. SIEM normalises events from all sources and applies detection rules, behavioural analytics, and correlation logic to surface potential incidents. Modern SIEMs (Splunk, Microsoft Sentinel, IBM QRadar, Elastic) include ML-driven anomaly detection. The failure mode: poorly tuned SIEMs generate thousands of low-quality alerts per day, causing alert fatigue that leads analysts to miss real threats.
EDR / XDR
EDR agents on endpoints collect granular telemetry about process activity, file changes, network connections, and registry modifications. XDR extends this across cloud workloads, email, identity, and network sources — providing correlated, cross-domain visibility that SIEM alone cannot replicate.
Network Monitoring (IDS/IPS, NDR)
Network-based detection identifies threats that bypass endpoint controls: lateral movement, command-and-control traffic, DNS tunnelling, and protocol abuse. NDR tools use ML baselines to flag anomalous traffic patterns in encrypted and east-west traffic.
Identity & Access Monitoring
The majority of breaches involve compromised credentials (Verizon DBIR 2024). Monitoring identity events — failed logins, impossible-travel alerts, privilege escalation, MFA bypass attempts, and service-account anomalies — is a primary detection surface, not an optional add-on.
Cloud Security Posture Management (CSPM)
CSPM tools continuously assess cloud environments for misconfigurations, compliance violations, and risky resource exposures. In multi-cloud environments, manual configuration review cannot keep pace with infrastructure change velocity — CSPM is a requirement, not a luxury.
Incident Response Workflow
Detection without response is noise. A defined workflow — runbooks, escalation paths, ownership assignments, and communication templates — ensures that when an alert fires, the right people take the right actions within the required timeframe. Every alert category needs a written playbook before you need it at 3 a.m.
Types of Cybersecurity Monitoring
TypeWhat It CoversKey ToolsPriority LevelSIEMCross-source log correlation, anomaly detection, compliance reportingSplunk, Microsoft Sentinel, IBM QRadar, Elastic SIEMFoundational — Day 1EDR / XDREndpoint behaviour, process activity, cross-domain detectionCrowdStrike Falcon, SentinelOne, Microsoft Defender XDRFoundational — Day 1IDS / IPSSignature-based network intrusion detection/preventionSnort, Suricata, Palo Alto NGFWHigh — perimeter and east-westNDRNetwork behavioural analytics, encrypted traffic, lateral movementDarktrace, ExtraHop, Vectra AIHigh — when lateral movement is a key riskCSPMCloud misconfigurations, IAM policy risks, compliance postureWiz, Prisma Cloud, AWS Security HubMandatory for any cloud workloadIdentity MonitoringIAM events, PAM activity, MFA anomalies, credential abuseMicrosoft Entra ID Protection, Okta ThreatInsight, BeyondTrustCritical — most breaches use stolen credentialsEmail Security MonitoringPhishing, BEC, malicious attachments, domain spoofingProofpoint, Mimecast, Microsoft Defender for Office 365Day 1 — email is the primary initial-access vectorDLP MonitoringSensitive data movement, exfiltration attempts, policy violationsForcepoint, Microsoft Purview, NightfallRequired for regulated data environmentsTypes of Cybersecurity Monitoring
Cybersecurity Monitoring Best Practices
1. Build Coverage First, Then Tune for Quality
The most common deployment mistake: organisations spin up a SIEM with five log sources and immediately start writing detection rules. Without broad coverage, blind spots are guaranteed. Before tuning, ensure every endpoint, cloud account, identity system, and network chokepoint is feeding telemetry into your monitoring stack.
2. Establish Baselines Before Writing Rules
Effective alerting requires knowing what normal looks like. Baseline login times, network traffic volumes, API call rates, and process execution patterns before deploying behavioural detection rules. Rules without baselines produce overwhelming false-positive rates that erode analyst trust in the system.
3. Map Every Alert to an Asset and an Owner
In Gart's delivery experience, teams consistently tell us the same story: "We generate thousands of alerts, but we can't tell which system they came from or who is responsible for it." Without an asset inventory that maps to alert sources, MTTD is artificially inflated not by detection failure but by coordination failure.
4. Write Runbooks Before You Need Them
A runbook is a step-by-step response procedure for a specific alert type. When an alert fires at 2 a.m., the analyst must be executing a defined playbook, not deciding what to do. For each high-priority alert category, define: who is notified, what immediate containment steps are taken, what evidence is preserved, and what escalation thresholds apply.
5. Tune Ruthlessly to Eliminate Alert Fatigue
Alert fatigue — analysts ignoring alerts because volume overwhelms judgment — is one of the leading causes of missed incidents. Commit to a weekly tuning cycle: review false-positive rates, suppress known-good patterns, and retire rules with no confirmed detections in the past 90 days. Fewer, higher-fidelity alerts are always better than more low-quality ones.
6. Validate Detection Coverage Through Testing
Never assume your monitoring detects what it claims to detect. Purple-team exercises, tabletop simulations, and adversary emulation (using MITRE ATT&CK as a framework) validate actual coverage. Teams that never test their detection capability routinely discover gaps during real incidents — exactly the wrong time to learn.
Gart Perspective
"In our projects, the biggest issue is rarely tool choice. It is signal quality: teams collect thousands of events but cannot map them to assets, owners, or response playbooks. The most effective monitoring programmes we have built are distinguished by their operational discipline, not their technology spend." — Fedir Kompaniiets, Co-founder, Gart Solutions
7. Integrate Threat Intelligence Feeds
Threat intelligence provides up-to-date information on known-malicious IPs, domains, file hashes, and emerging TTPs (tactics, techniques, and procedures). Integrating commercial or open-source intel feeds into your SIEM and EDR ensures that known-bad indicators trigger alerts even before anomalous behaviour appears.
Need help building 24/7 cybersecurity monitoring?
Gart designs and implements monitoring programmes for cloud-native and regulated environments — from architecture to runbooks to alert tuning.
Book a Monitoring Assessment
Key Cybersecurity Monitoring KPIs & Metrics
Tracking the right metrics transforms cybersecurity monitoring from a cost centre into a measurable security programme. The table below includes benchmarks based on industry data and Gart delivery experience — treat them as directional targets, not universal standards.
MetricWhat it measuresWhy it mattersTarget benchmarkHow to improveMTTD — Mean Time to DetectTime from initial breach to detectionEach additional day of dwell time increases breach cost< 24 h for high-severity eventsBroader log coverage, behavioural baselines, threat intel integrationMTTR — Mean Time to RespondTime from detection to active response actionSlow response allows attacker to expand access and exfiltrate data< 1 h for critical alertsAutomated playbooks, defined on-call rotations, pre-written runbooksMTTC — Mean Time to ContainTime to fully isolate the affected environmentContainment limits blast radius and regulatory notification timelines< 4 h for critical incidentsPre-approved isolation procedures, network segmentation, SOAR automationFalse Positive Rate% of alerts that are not genuine threatsHigh rates cause alert fatigue, leading analysts to miss real incidents< 10% for high-fidelity rulesRegular rule tuning, ML-assisted triage, suppression of known-good patternsAlert-to-Incident RatioTotal alerts generated per confirmed incidentHigh ratio = noise drowning real signals< 100:1 for mature programmesCorrelation rules, consolidation of related alerts, SIEM tuningPatching Compliance Rate% of critical CVEs patched within SLA windowUnpatched vulnerabilities are the most commonly exploited entry points> 95% within defined SLAAutomated patch management, CVE prioritisation by exposure and exploit availabilityLog-Source Coverage% of known assets actively feeding telemetryUnmonitored assets are guaranteed blind spots> 98% of known asset inventoryAsset inventory automation, agent deployment tooling, CSPM integrationDLP Incident CountVolume of sensitive-data policy violations per periodEarly indicator of insider threat or compromised account activityTrending down quarter-over-quarterData classification, DLP policy refinement, UBA for anomalous data accessKey Cybersecurity Monitoring KPIs & Metrics
How to Implement Cybersecurity Monitoring: A 30/60/90-Day Plan
Most implementations fail because they try to do everything simultaneously. A phased approach builds foundational capability first, then layers sophistication on proven ground.
Days 1–30: Foundation
Asset inventory: Document every endpoint, server, cloud account, SaaS application, and network device in scope. You cannot protect — or correlate events from — assets you do not know exist.
Log source prioritisation: Identify your 10–15 highest-value sources: Active Directory / Entra ID, firewalls, DNS, VPN, cloud IAM logs, and critical server OS logs. Get these feeding into SIEM first.
Deploy EDR on all managed endpoints with high-confidence detection enabled and exclusion lists documented.
Define alert severity levels (P1–P4 or Critical/High/Medium/Low) and assign explicit on-call ownership for each level.
Establish baseline metrics: Record current MTTD and MTTR (even if poor) so you have a starting point to improve from.
Days 31–60: Coverage & Tuning
Expand log collection to all remaining sources: cloud workloads, SaaS applications, network devices, email security gateway.
Establish behavioural baselines for users, hosts, and services using 2–3 weeks of clean telemetry.
Write initial runbooks for the top 10 alert types by volume.
Begin weekly alert quality reviews: track and suppress the top 5 false-positive rule sources each week.
Integrate identity monitoring: connect IAM / PAM logs, enable impossible-travel and anomalous-login alerting.
Conduct first tabletop exercise to validate detection and response procedures against a realistic scenario.
Days 61–90: Optimisation & Validation
Integrate threat intelligence feeds into SIEM and EDR.
Deploy CSPM across all cloud environments and address critical posture findings.
Complete runbooks for all Tier 1 and Tier 2 alert categories.
Re-measure MTTD, MTTR, and false-positive rate to quantify improvement.
Conduct purple-team or adversary-emulation exercise mapped to MITRE ATT&CK TTPs relevant to your industry.
Establish a quarterly review cadence: coverage audit, detection-rule review, KPI reporting to leadership.
Cybersecurity Monitoring Readiness Checklist — for CISOs & CTOs
Complete, up-to-date asset inventory with data owners assigned
EDR deployed on ≥ 98% of managed endpoints
SIEM receiving normalised logs from all priority sources
Identity monitoring active (IAM, PAM, MFA events)
Cloud security posture monitoring (CSPM) enabled across all cloud accounts
Network monitoring covering east-west (lateral) traffic, not only perimeter
Alert severity levels and on-call escalation paths documented
Runbooks written and tested for top 10 alert categories
False-positive rate below 10% for high-fidelity detection rules
MTTD and MTTR baselines established and reported monthly
Detection coverage validated via exercise in the past 6 months
Quarterly monitoring review process in place with leadership reporting
In-House SOC vs. Managed Detection & Response (MDR): Which Model Fits Your Business?
FactorIn-House SOCManaged MDRHybrid ModelTime to 24/7 coverage12–18 months (hiring + tooling)4–8 weeksMDR covers gaps while SOC maturesUpfront costHigh — headcount, tools, trainingLow-medium — subscription-basedMediumEnvironment contextHigh — team knows your systemsLower initially, improves over 6–12 monthsHigh — internal team retains contextAnalyst expertise depthDepends on hiring successAccess to deep specialist talent poolSpecialist MDR for complex threats + internal for day-to-dayScalabilitySlow — constrained by hiring timelinesFast — elastic coverageFastBest fitsLarge enterprise, regulated industries, classified data environmentsMid-market, rapid-growth companies, lean security teamsEnterprise augmenting internal SOC with external threat huntingIn-House SOC vs. Managed Detection & Response (MDR)
Decision Guidance
If you have fewer than 3 dedicated security analysts today, a fully in-house 24/7 SOC is not achievable in the near term. An MDR or co-managed model delivers immediate coverage while you build internal capability. The key question to ask an MDR provider: "What does your escalation process look like at 3 a.m. on a Sunday?" — the specificity of their answer tells you whether they truly operate 24/7.
Industry-Specific Cybersecurity Monitoring Requirements
Healthcare (HIPAA)
Healthcare organisations face a dual mandate: protect patient data under HIPAA and maintain clinical system availability. Key monitoring requirements include audit logs for all access to ePHI (electronic protected health information), detection of unauthorised export or modification of patient records, and dedicated monitoring of medical-device networks — a rapidly expanding attack surface. HIPAA breach-notification requirements demand evidence of precisely what data was accessed and when, which only comprehensive monitoring can provide. See Gart's work in healthcare IT consulting.
Financial Services (PCI-DSS, GDPR, SOX)
Financial organisations must monitor cardholder data environments under PCI-DSS, maintain detailed privileged-access logs for SOX compliance, and implement data-subject access controls under GDPR. Specific requirements include anomalous-transaction pattern detection, monitoring of all privileged access to financial systems, and demonstrable data-retention and erasure controls. Gart's PCI-DSS audit service establishes the compliance baseline that a monitoring programme then maintains continuously.
SaaS & Cloud-Native Companies
For SaaS businesses, monitoring priorities shift to cloud infrastructure: API security monitoring, cloud IAM anomaly detection, multi-tenant data isolation verification, and software supply-chain security. Cloud misconfiguration remains the leading cause of SaaS data breaches — CSPM is the minimum viable control, not a nice-to-have. The CNCF publishes guidance on cloud-native security monitoring practices relevant to this segment.
Government & Defence
Government entities operate under frameworks such as CMMC, FedRAMP, and FISMA that mandate continuous monitoring, defined log-retention periods, and specific incident-reporting timelines. Insider-threat monitoring — tracking privileged user activity, data access patterns, and behavioural deviations — receives particular regulatory emphasis in this sector.
Common Cybersecurity Monitoring Mistakes
Critical Insight
Most common mistake
Compliance logging ≠ active monitoring. Storing logs to satisfy an auditor and actively analysing logs in near-real-time to detect threats are fundamentally different activities. Many organisations do the former and believe they are doing the latter. A log that is stored but never analysed provides zero detection value.
Other failure patterns Gart sees repeatedly across engagements:
Too many tools, no ownership. Buying six security platforms without clear owners and a unified workflow creates gaps and confusion. Assign explicit ownership for every tool and integrate them into a single response workflow.
No baselines, no useful alerts. Deploying detection rules before establishing behavioural baselines guarantees high false-positive rates. Baseline first, rule second.
Missing cloud and SaaS coverage. Traditional monitoring programmes were designed for on-premises environments. Cloud workloads, SaaS applications, and identity providers are now primary attack surfaces — but many programmes still lack visibility there.
Identity monitoring treated as optional. The majority of modern attacks involve compromised credentials or privilege abuse. A monitoring programme without IAM event analysis and behavioural analytics for identity has a critical blind spot.
No runbooks → MTTR measured in days, not hours. Programmes with documented, tested runbooks consistently show 2–5× faster MTTR than those without them.
Detection coverage never validated. Assuming your tools detect what they claim to detect, without any testing, is overconfidence that attackers actively exploit.
How Gart Approaches Cybersecurity Monitoring in Practice
Gart's cybersecurity monitoring engagements follow a structured delivery framework developed through implementations across healthcare, fintech, SaaS, and enterprise environments:
Discovery and asset mapping: We start by building a complete picture of what exists — every endpoint, cloud account, SaaS tool, and identity system — and what is currently being monitored. Coverage gaps are the first deliverable.
Log-source prioritisation: Not all logs are equal. We identify the 15–20 sources that cover the highest-risk attack paths in your environment and ensure those are feeding into SIEM with proper normalisation before expanding coverage further.
Alert tuning and noise reduction: We treat false-positive rate as a primary quality metric. A SIEM generating 10,000 alerts per day with 2% true-positive rate is worse than one generating 200 alerts with 40% true-positive rate. We optimise toward the latter.
Incident workflow design: Every alert category receives a written runbook that defines: detection criteria, immediate triage steps, escalation path, evidence-preservation requirements, and resolution criteria.
Ongoing optimisation: Monitoring is not a project — it is a programme. We establish a quarterly review process that measures KPI trends, identifies new coverage gaps from infrastructure changes, and updates detection logic for emerging threat patterns.
Why Trust Gart on This Topic
Gart has designed and implemented monitoring programmes for international SaaS platforms, healthcare systems, regulated financial environments, and cloud-native enterprises across Europe and North America. Our team brings direct hands-on experience with SIEM deployment, EDR/XDR integration, CSPM implementation, and compliance-aligned logging — not only theoretical knowledge.
Gart Solutions · Cybersecurity Monitoring Services
Build 24/7 Cybersecurity Monitoring Without a Full SOC Team
Gart designs and implements production-ready monitoring programmes for cloud-native companies and regulated enterprises — from architecture through continuous detection.
🗺️
Discovery & Asset Mapping
Full inventory of assets, log sources, and coverage gaps — so you know exactly what you are monitoring and what you are missing.
🔧
SIEM / XDR Architecture
Tool selection, integration design, and log-source normalisation built for your specific environment, not a generic template.
📉
Alert Tuning & Noise Reduction
We reduce false-positive rates to under 10% through behavioural baselining, rule optimisation, and continuous tuning cycles.
📋
Runbooks & Escalation Paths
Documented, tested incident-response playbooks for every alert category — so your team acts immediately, not improvises.
☁️
Cloud Security & CSPM
Continuous cloud posture monitoring, IAM anomaly detection, and multi-cloud visibility across AWS, Azure, and GCP.
✅
Compliance Readiness
Monitoring programmes designed around HIPAA, PCI-DSS, GDPR, SOC 2, and ISO 27001 requirements — audit-ready from day one.
Real-World Impact
Centralized Monitoring for a B2C SaaS Music Platform
Implemented real-time security and infrastructure monitoring using AWS CloudWatch and Grafana, delivering scalable cross-region visibility and reduced incident detection time.
Read the case study →
Monitoring Solutions for Scaling a Digital Landfill Platform
Designed a cloud-neutral monitoring solution spanning Iceland, France, Sweden, and Turkey — including compliance logging and full observability without vendor lock-in.
Read the case study →
Book a Monitoring Assessment
View Monitoring Services
Fedir Kompaniiets
Co-founder & CEO, Gart Solutions · Cloud Architect & DevOps Consultant
Fedir is a technology enthusiast with over a decade of diverse industry experience. He co-founded Gart Solutions to address complex tech challenges related to Digital Transformation, helping businesses focus on what matters most — scaling. Fedir is committed to driving sustainable IT transformation, helping SMBs innovate, plan future growth, and navigate the "tech madness" through expert DevOps and Cloud managed services. Connect on LinkedIn.
Don’t wait for a breach — contact Gart today and fortify your cybersecurity defenses!

What is application monitoring and why is it critical?
Application monitoring is the continuous practice of tracking your software's performance, availability, and error rates in real time. In 2026, with the average cost of a production outage exceeding $5,600 per minute (Gartner), teams that monitor proactively resolve incidents up to 60% faster than those relying on reactive alerts. This guide covers key metrics, tools like Datadog and Prometheus, step-by-step implementation, and insider practices to avoid alert fatigue.
What Is Application Monitoring?
Application monitoring is the process of continuously observing, tracking, and analyzing the performance, availability, and overall health of software applications running in production. It gives engineering teams real-time and historical visibility into how an application behaves under load, where errors originate, and how user experience is affected by infrastructure changes.
The discipline spans from low-level infrastructure metrics (CPU, memory) to high-level business signals (conversion rates, revenue per transaction). Application monitoring is today a foundational pillar of both DevOps practices and Site Reliability Engineering (SRE).
The key objectives of application monitoring are:
Ensure optimal application performance and response times
Maintain high availability, reliability, and uptime SLAs
Detect and resolve incidents before they impact end users
Provide data for capacity planning and architecture decisions
Support compliance and security audit requirements
Why Application Monitoring Matters in 2026
Modern applications are no longer monolithic. They are distributed ecosystems of microservices, serverless functions, third-party APIs, and multi-cloud infrastructure. A single degraded dependency can cascade into a full-blown outage within seconds — yet be invisible without proper monitoring in place.
$5,600
Average cost per minute of downtime
Gartner, 2024
60%
Faster MTTR with proactive monitoring
Gart Solutions client data
81%
Of outages are detected by end users first
Google SRE Book
Without application monitoring, engineering teams are essentially flying blind. They discover problems from customer complaints, social media escalations, or late-night PagerDuty calls — after significant business damage has already occurred. With the right monitoring stack, teams shift from reactive firefighting to proactive reliability engineering.
"Monitoring isn't just an operational concern — it's a business continuity strategy. Every minute of undetected degradation erodes user trust in ways that take months to rebuild." — Fedir Kompaniiets, Co-founder, Gart Solutions
Key Challenges in Application Monitoring
One of the major challenges in modern application monitoring is managing the complexity that comes with microservices. Applications today are built using a multitude of microservices that interact with one another, often spanning across different cloud environments. Finding and monitoring all these services can be a daunting task.
A useful analogy can be drawn from early aviation. Pilots in the past had to rely on their intuition and limited manual tools to interpret multiple signals coming from various instruments simultaneously, making it difficult to ensure safe operations. Similarly, application operators are often flooded with a vast amount of performance signals and data, which can be overwhelming to process. This data overload is compounded by the fact that microservices are highly distributed and can have many dependencies that require monitoring.
Without the right tools, managing all this information can be a bottleneck, just like early pilots struggled with too many signals.
SRE (Site Reliability Engineering) principles streamline the monitoring of complex systems by focusing on the most critical aspects of application performance. Rather than tracking every possible metric, SRE emphasizes the Golden Signals (latency, errors, traffic, and saturation). This approach reduces the complexity of analyzing multiple services, allowing engineers to identify root causes faster, even in microservice topologies where each service could be based on different technologies. The key advantage is faster detection and resolution of issues, minimizing downtime and enhancing the user experience.
Types of Application Monitoring
Application monitoring encompasses a range of techniques and tools to provide comprehensive visibility into the performance, availability, and overall health of software systems. Some of the key types of application monitoring include:
Infrastructure Monitoring
This involves monitoring the underlying hardware, virtual machines, and cloud resources that support the application, such as CPU, memory, storage, and network utilization. Infrastructure monitoring helps ensure the reliable operation of the application's foundation.
Application Performance Monitoring (APM)
APM focuses on tracking the performance and behavior of the application itself, including response times, error rates, transaction tracing, and resource consumption. This allows teams to identify performance bottlenecks and optimize the application's codebase.
User Experience Monitoring
This approach tracks how end-users interact with the application, measuring metrics like page load times, user clicks, and session duration. User experience monitoring helps ensure the application meets or exceeds customer expectations.
Log and Event Monitoring
Monitoring the application's logs and event data can provide valuable insights into system behavior, errors, and security incidents. This information can be used to troubleshoot problems and ensure regulatory compliance.
Synthetic Monitoring
Synthetic monitoring uses automated scripts to simulate user interactions and measure the application's responsiveness, availability, and functionality from various geographic locations. This proactive approach helps detect issues before they impact real users.
Real-User Monitoring (RUM)
RUM tracks the actual experience of end-users by collecting performance data directly from the user's browser or mobile device. This provides a more accurate representation of the user experience compared to synthetic monitoring.
Application Monitoring vs. Observability: What's the Difference?
These terms are often used interchangeably, but they describe different philosophies. Understanding the distinction is critical for building a mature monitoring program.
Traditional
Application Monitoring
Focus: Tracks predefined metrics and thresholds
Goal: Answers: "Is the system healthy?"
Nature: Reactive — triggers alerts when known conditions occur
Use Case: Best for known failure modes (e.g. CPU > 90%)
Tools: Nagios, Zabbix, CloudWatch
VS
Advanced
Observability
Focus: Enables ad-hoc exploration of system behavior
Goal: Answers: "Why is the system behaving this way?"
Nature: Proactive — surfaces "unknown unknowns"
Use Case: Complex failure modes (e.g. distributed tracing)
Tools: OpenTelemetry, Honeycomb, Datadog APM
The practical takeaway: Monitoring tells you that something is wrong. Observability helps you understand why. In 2026, mature engineering teams need both — starting with solid application monitoring and layering in full observability as complexity grows.
Key Metrics for Application Monitoring
Not all metrics are created equal. Tracking hundreds of signals creates noise without improving reliability. The most effective teams focus on a structured hierarchy of metrics — from foundational signals up to business impact.
Tier 1: The Four Golden Signals (SRE Standard)
Defined by Google's SRE team, these four metrics form the minimum viable monitoring baseline for any production service:
SignalDefinitionHealthy Threshold (typical)Alert ConditionLatencyTime to process a request (P50/P95/P99)P95 < 300msP95 > 500ms for 5 minError Rate% of requests resulting in 5xx errors< 0.1%> 1% over 5 minTrafficRequests per second (RPS/QPS)Baseline ± 30%Drop > 50% or spike > 3x baselineSaturationResource utilization (CPU, memory, queue depth)< 70%> 85% sustained > 10 minThe Four Golden Signals (SRE Standard)
Tier 2: Application Performance Metrics (APM KPIs)
MetricWhy It MattersToolingApdex ScoreSingle satisfaction score for response timeNew Relic, DatadogTransaction TracesEnd-to-end request path through servicesJaeger, Datadog APM, ZipkinDB Query LatencySlow queries cascade to API slowdownspgBadger, Datadog, New RelicGarbage CollectionGC pauses cause latency spikes in JVM/Go appsPrometheus, AppDynamicsThread Pool UtilizationThread exhaustion causes request queuingJMX, Datadog, New RelicApplication Performance Metrics (APM KPIs)
Tier 3: Business & User Experience Metrics
These bridge the gap between technical performance and business outcomes — critical for communicating the value of reliability work to stakeholders:
MetricBusiness ConnectionPage Load Time (Core Web Vitals)1s delay → 7% drop in conversions (Google data)Checkout Funnel Completion RateDirect revenue signal for e-commerceAPI Response Time by Customer TierSLA compliance for enterprise contractsSession Abandonment RateCorrelated with performance degradationsReal User Monitoring (RUM) DataActual user experience vs synthetic baselinesBusiness & User Experience Metrics
Types of Application Monitoring
A comprehensive application monitoring strategy spans multiple layers of the tech stack. Each type serves a distinct purpose and requires different tooling:
1. Infrastructure Monitoring
Tracks the underlying hardware, VMs, and cloud resources — CPU utilization, memory, disk I/O, and network throughput. This is the foundation. Without infrastructure health, application-level metrics are meaningless. Tools: Prometheus Node Exporter, AWS CloudWatch, Nagios.
2. Application Performance Monitoring (APM)
The core layer — tracks response times, error rates, transaction traces, and code-level bottlenecks. APM agents instrument your application and surface the exact line of code causing a slowdown. Tools: Datadog APM, New Relic, AppDynamics, Dynatrace.
3. Synthetic Monitoring
Automated scripts simulate user journeys from multiple geographic locations, proactively testing availability and response times before real users are affected. Critical for SLA verification and pre-release checks. Tools: Datadog Synthetics, New Relic Synthetics, Pingdom.
4. Real User Monitoring (RUM)
Captures actual performance data from real browsers and mobile devices. Unlike synthetic monitoring, RUM shows how geography, device type, and network conditions affect your actual users. Tools: Datadog RUM, New Relic Browser, Elastic RUM.
5. Log & Event Monitoring
Aggregates, indexes, and searches application logs for errors, security incidents, and behavioral anomalies. Structured logging dramatically improves searchability and alerting accuracy. Tools: ELK Stack, Splunk, Grafana Loki, Datadog Logs.
6. Distributed Tracing
In microservices architectures, a single user request may touch dozens of services. Distributed tracing follows the entire request path, making it possible to pinpoint exactly where latency or errors are introduced. Tools: Jaeger, Zipkin, OpenTelemetry, AWS X-Ray.
TypeBest ForWhen to PrioritizeInfrastructure MonitoringHardware/cloud healthFrom day oneAPMApp performance & errorsFrom day oneSynthetic MonitoringProactive availabilityBefore launchReal User MonitoringActual user experiencePost-launch scaleLog MonitoringRoot cause investigationFrom day oneDistributed TracingMicroservices debuggingWhen adopting microservices
Top Application Monitoring Tools (Compared)
Choosing the right tooling depends on your team size, budget, infrastructure complexity, and in-house expertise. Here is an honest comparison of the most widely adopted platforms:
Full-Stack APM · Commercial
Datadog
The gold standard for cloud-native observability. Exceptional out-of-the-box integrations (800+), AI-powered anomaly detection, and a unified platform for metrics, logs, and traces.
Best for: Mid-size to enterprise teams wanting a "single pane of glass."
APM · Commercial
New Relic
Usage-based pricing makes it accessible for startups. Strong distributed tracing, excellent browser/mobile monitoring, and a genuinely useful free tier.
Best for: Developer-led teams wanting fast time-to-value.
Metrics · Open Source
Prometheus
The de facto standard for Kubernetes metrics collection. Powerful PromQL language and a massive ecosystem. Requires investment but offers total control.
Best for: Cloud-native teams prioritizing zero licensing costs.
Visualization · Open Source
Grafana
The most flexible dashboard platform available. Connects to Prometheus, Loki, Tempo, CloudWatch, and Datadog. Used by teams at every scale.
Best for: Teams needing highly customizable visual observability.
AI-Powered APM · Commercial
Dynatrace
Sets itself apart with automatic dependency mapping and Davis AI for root cause analysis. Minimizes configuration overhead significantly.
Best for: Large enterprises with complex legacy architectures.
Logs · Commercial/OSS
ELK Stack
Elasticsearch, Logstash, and Kibana — the standard for log management. Highly scalable and flexible, but requires operational overhead to manage.
Best for: Deep log analysis and large-scale data indexing.
ToolBest ForPricing ModelOpen Source?DatadogFull-stack, enterprisePer host/GB ingestedNoNew RelicAPM, developer-led teamsPer user + data ingestNoPrometheusKubernetes, metricsFree, self-hostedYes (CNCF)GrafanaVisualization, dashboardsFree / Grafana CloudYesDynatraceEnterprise, AI-drivenPer DEM unitNoELK StackLog managementFree / Elastic CloudYesAppDynamicsEnterprise APMPer CPU coreNoTop Application Monitoring Tools (Compared)
The Monitoring Maturity Model
Not all organizations need to — or should try to — build the most sophisticated monitoring stack on day one. This original framework from Gart Solutions' SRE practice maps your current state and provides a clear progression path:
1
Level 1
Reactive
Users report incidents
No monitoring tooling in place. The team discovers outages through customer complaints or social media. MTTD measured in hours or days.
2
Level 2
Basic Alerts
Infrastructure health checks & uptime
Server uptime checks, basic CPU/memory alerts, and simple HTTP pings. Issues are detected faster, but root cause analysis is still manual.
3
Level 3
APM in Place
Application performance monitoring deployed
APM agents instrument services, error rates and latency are tracked. Dashboards exist, but alert thresholds are manually configured.
MTTD < 15 min
4
Level 4
Observability
Metrics, logs, and traces unified
The three pillars are correlated in a single platform. SLIs and SLOs are defined, error budgets tracked. Runbooks linked to alerts.
MTTD < 5 min
5
Level 5
Predictive
AI/ML-driven proactive operations
Anomaly detection and automated remediation (circuit breakers) prevent incidents. Business and reliability metrics are fully integrated.
True Proactive Ops
Where are you today?
Most organizations we audit at Gart Solutions are between Level 2 and Level 3.
The jump from Level 3 to Level 4 — correlating metrics, logs, and traces — delivers the largest ROI in reduced MTTR and faster deployment confidence.
How to Implement Application Monitoring: Step-by-Step
A monitoring rollout that tries to instrument everything at once typically fails. This step-by-step approach from our SRE practice gets you to production-grade monitoring in 4–6 weeks without overwhelming your team:
Define your monitoring goals and SLOsBefore choosing any tools, define what "healthy" means for your application. Set Service Level Objectives (SLOs): e.g., "99.9% of requests complete in under 300ms." These will drive every alert threshold you configure.
Instrument your application (APM agent or OpenTelemetry)Install an APM agent (Datadog, New Relic) or instrument with OpenTelemetry SDK for vendor-neutral telemetry. Start with your most critical service or user-facing API. This takes 1–2 hours and immediately surfaces error rates and latency percentiles.
Deploy infrastructure monitoringUse Prometheus Node Exporter (Linux) or the cloud provider's native monitoring (CloudWatch, Azure Monitor) to collect host-level metrics. Configure a Grafana dashboard with the Four Golden Signals for each service.
Set up centralized log aggregationShip all application and infrastructure logs to a central store (ELK, Grafana Loki, Datadog Logs). Enforce structured JSON logging across services. Set up log-based alerts for critical error patterns and security events.
Configure alerts — start with just Resist the temptation to alert on everything. Start with five actionable, SLO-derived alerts: high error rate, high P95 latency, service down, disk full warning, and memory saturation. Each alert should have a runbook link. See the Alert Fatigue section below.
Integrate monitoring into your CI/CD pipelineAdd automated performance gates to your deployment pipeline. Configure rollback triggers if error rate exceeds baseline within 5 minutes of a deployment. Use synthetic tests to verify critical user journeys post-deploy.
Conduct weekly monitoring reviewsHold a 30-minute weekly review of alert noise, missed incidents, and dashboard usage. Prune alerts that fired but required no action (noise). Add alerts for any incident that wasn't caught by existing monitoring.
Alert Fatigue: The Silent Killer of Monitoring Programs
Alert fatigue is one of the most underappreciated risks in application monitoring. When too many alerts fire — especially for non-actionable conditions — on-call engineers begin ignoring them. The result is worse incident detection than having no alerting at all.
⚠️
Attention Required
The Alert Fatigue Trap
In a production incident post-mortem we conducted with a fintech client, their on-call team had received 1,400 alert notifications in a single week — of which fewer than 80 required any action. When the real outage hit, it was buried in noise. MTTR was 4 hours longer than it should have been.
How to Fight Alert Fatigue
The key principle: every alert must be actionable. If an alert fires and the on-call engineer has no action to take, the alert should not exist.
Anti-PatternSolutionAlerting on symptoms of symptomsAlert on user-facing Golden Signals onlyStatic thresholds on dynamic metricsUse anomaly detection / % change alertsAlerts without runbooksEvery alert must link to a documented responsePaging for non-urgent issuesRoute warnings to Slack, only page for criticalNo alert review cadenceWeekly 30-min alert hygiene reviewSame alert for dev and prodSeparate alert policies per environment
🔧
Gart SRE Insight
The "Would You Wake Up At 3AM?" Test
Before adding any alert to your on-call rotation, ask: "If this fires at 3am, would I be grateful for the wake-up call, or annoyed?" If the honest answer is "annoyed" — it belongs in a dashboard or Slack notification, not a PagerDuty page. This single test eliminates roughly 40% of alert noise in most environments we audit.
Production Monitoring Checklist
Use this checklist before declaring any service production-ready. It reflects the minimum viable monitoring baseline that our SRE team at Gart Solutions requires for all client deployments:
Infrastructure & Platform
CPU, memory, disk, and network metrics collected for all hosts/pods
Kubernetes cluster health monitored (node conditions, pod restarts, PVC usage)
Cloud provider resource quotas and limits tracked
Database connection pool utilization and slow query logs enabled
SSL/TLS certificate expiry monitoring configured (alert at 30 days)
Application Performance
APM agent deployed and reporting latency percentiles (P50, P95, P99)
Error rate tracking enabled with 5xx/4xx split
Distributed tracing configured for all service-to-service calls
External API dependency latency and error rates monitored
Background job / queue depth and processing latency tracked
Alerting & Response
All production alerts have linked runbooks
On-call rotation configured with escalation policies
Alert severity tiers defined (Critical → page, Warning → Slack)
Deployment-correlated alerting enabled (suppress noise during deploys)
SLO dashboards visible to both engineering and leadership
Synthetic & User Experience
Synthetic checks running against critical user journeys every 1 min
Real User Monitoring (RUM) capturing Core Web Vitals
Geographic availability monitoring from 3+ regions
Best Practices in Application Monitoring
Effective application monitoring requires a strategic approach and the adoption of best practices. Some key recommendations include:
Set SLO-Driven Alert Thresholds, Not Arbitrary Ones
Configure every alert threshold to correspond directly to an SLO violation — not a technical gut-feel. An alert that fires at "CPU > 80%" is meaningless without knowing whether that CPU level actually causes user impact.
Leverage AI/ML for Anomaly Detection
Modern platforms like Datadog and Dynatrace offer ML-based anomaly detection that adapts to your application's normal behavior patterns — including daily and weekly seasonality. This dramatically reduces false positives compared to static thresholds.
Monitor Across All Environments, Not Just Production
Extend monitoring to staging and even integration environments with proportionally relaxed thresholds. Catching a performance regression in staging before it reaches production is always cheaper than a production incident.
Instrument the Deployment Event
Always annotate your monitoring dashboards with deployment markers. The most common question during an incident is "was this caused by a recent deployment?" — having deployment events on your metrics timeline answers that question instantly.
Build Dashboards for the Right Audience
Create distinct dashboard views for different stakeholders: an SRE/on-call view (real-time alerts, error rates, latency breakdowns), an engineering view (per-service deep dives), and an executive view (SLO compliance, availability percentages, business impact metrics).
Test Your Monitoring — Before You Need It
Run regular "chaos" exercises where you intentionally trigger failure conditions (traffic spikes, kill a service, exhaust disk space) to verify that your alerts fire as expected and runbooks are accurate. Finding a broken alert during a drill is far better than during a real outage.
Optimize Your Application Performance with Expert Monitoring
Is your application running at its best? At Gart Solutions, we specialize in setting up robust monitoring systems tailored to your needs. Whether you’re looking to enhance performance, minimize downtime, or gain deeper insights into your application’s health, our team can help you configure and implement comprehensive monitoring solutions.
Gart Solutions Case Studies
Theory is useful. Real outcomes are better. Here are two recent engagements from Gart Solutions' monitoring practice:
Case Study 1 · B2C SaaS
Centralized Monitoring for a Global Music Platform
Challenge
A music platform serving millions of concurrent users globally had zero visibility into regional performance. Incidents were discovered by users, not engineers. Infrastructure was split across multiple AWS regions with no unified observability.
Solution
Gart deployed a centralized monitoring architecture using AWS CloudWatch, Datadog APM, and Grafana dashboards providing regional health views. Custom SLO dashboards were created for engineering leadership.
Read the full case study →
60%
Reduction in MTTR
4→