Infrastructure scalability is no longer a luxury — it's the architectural foundation that separates businesses that survive growth from those that collapse under it. This guide covers everything from fundamental scaling concepts to modern auto-scaling patterns, hybrid strategies, and real-world decision frameworks used by engineering teams at scale.
What Is Infrastructure Scalability?
Infrastructure scalability is the capacity of an IT system to handle increasing workloads by adding resources — without requiring a fundamental redesign. A scalable infrastructure maintains performance, reliability, and cost-efficiency as demand grows, whether that growth is gradual or sudden.
Scalability is often confused with related concepts. Understanding the distinctions matters for architectural decision-making:
ConceptDefinitionKey DifferenceScalabilityAbility to handle growing workload by adding resourcesManual or planned expansionElasticityAutomatic, real-time scaling up and down based on demandDynamic, reactive to load changesAvailabilitySystem uptime and accessibility under normal and abnormal conditionsReliability focus, not capacityPerformanceSpeed and efficiency of a specific workload at a given momentMeasured now, not under future loadResilienceAbility to recover from failures quicklyPost-failure recovery, not capacity growthWhat Is Infrastructure Scalability?
Usually, scaling does not involve rewriting the code, but either adding servers or increasing the resources of the existing one. According to this type, vertical and horizontal scaling are distinguished.
💡 Key InsightEven a company that isn't growing still faces increasing infrastructure demands over time. Data accumulates, systems become more complex, and technical debt compounds — making infrastructure scalability planning essential regardless of business growth trajectory.
20×
Hardware cost reduction possible with horizontal scaling vs. single high-end server
99.99%
Uptime achievable with distributed horizontal architecture and proper fault tolerance
40–65%
Typical infrastructure cost reduction from auto-scaling and rightsizing
Vertical Scaling (Scale Up): Deep Dive
Vertical scaling — also called scaling up — means increasing the capacity of a single existing server: adding more CPU cores, RAM, faster storage, or a more powerful GPU. The machine becomes more powerful, but it remains one machine.
Architecture Patterns
Vertical Scaling (Scale Up)
Before
🖥️
Standard Server
4 vCPU / 16 GB
UPGRADE
After
🚀
High-End Server
32 vCPU / 256 GB
Result: Same machine, significantly more resources. No distribution complexity, but a hard ceiling exists.
Advantages of Vertical Scaling
No code changes required. Applications don't need to be redesigned for distributed execution. The upgrade is transparent at the software level.
Operational simplicity. A single server environment is easier to manage, monitor, and debug than a distributed cluster of nodes.
Lower latency for tightly coupled workloads. Intra-process communication on one machine is dramatically faster than inter-node network calls.
Familiar tooling. Teams experienced in single-server environments can scale up without new infrastructure tooling or orchestration skills.
Immediate performance gain. Adding RAM or CPU cores takes effect upon restart — no migration, reconfiguration, or code deployment required.
Limitations of Vertical Scaling
Hard ceiling on capacity. Every server has a physical maximum. Eventually there is no larger instance to upgrade to, forcing a disruptive migration.
Single point of failure. If the server goes down, the entire application goes with it. No horizontal redundancy means downtime equals total outage.
Expensive at high tiers. The highest-spec servers command enormous price premiums. The cost-per-unit-of-compute rises sharply as you move up the hardware tier.
Downtime during upgrades. Physical or hypervisor-level resource additions often require a maintenance window, even if brief.
⚠️ Common MistakeMany teams choose vertical scaling as the default response to performance problems because it feels simpler. But repeatedly scaling up without addressing architectural inefficiencies leads to escalating costs and increasing migration risk as hardware tiers are exhausted.
When Vertical Scaling Is the Right Choice
Vertical scaling delivers the most value in specific scenarios. It is not inherently inferior to horizontal scaling — for the right workload, it is precisely correct:
Scale Up
Monolithic Legacy Applications
Applications with deep internal state dependencies or a tightly coupled codebase that cannot be easily distributed across nodes.
Scale Up
High-Frequency Trading Platforms
Latency-sensitive systems where microseconds matter and inter-node network latency would violate SLAs. A single powerful machine is optimal.
Scale Up
In-Memory Databases
Redis, Memcached, or in-memory OLAP databases benefit enormously from large RAM configurations. Adding RAM scales capacity linearly and immediately.
Scale Up
Predictable, Bounded Workloads
Applications with stable, predictable load that will not exceed known limits within the infrastructure lifecycle. Simpler and cheaper than distributed overhead.
Horizontal Scaling (Scale Out): Deep Dive
Horizontal scaling — also called scaling out — means adding more servers (nodes) to distribute the workload. Instead of one increasingly powerful machine, you have many smaller, cooperating machines with load distributed across them.
Scalability Patterns
Horizontal Scaling (Scale Out)
Traffic Manager
⚖️
Load Balancer
🖥️
Node 1
4 vCPU / 16 GB
🖥️
Node 2
4 vCPU / 16 GB
🖥️
Node 3
4 vCPU / 16 GB
➕
Node N
On Demand
Result: Traffic is distributed. Any node can fail without total outage. Add more nodes as demand grows — theoretically without limit.
Advantages of Horizontal Scaling
Theoretically unlimited capacity. Add nodes indefinitely as demand grows. No hard ceiling on the total capacity of the cluster.
Fault tolerance & high availability. If one node fails, the load redistributes to remaining nodes. No single point of failure exists by design.
Cost-efficient commodity hardware. Many mid-tier servers cost a fraction of an equivalent high-spec single server, often reducing hardware costs by up to 20×.
Zero-downtime scaling. Add or remove nodes while the application continues serving traffic. No maintenance windows required for capacity changes.
Geographic distribution. Nodes can be placed in multiple regions, reducing latency for global users and satisfying data residency requirements.
Enables auto-scaling. Horizontal architectures are the foundation for dynamic, demand-driven auto-scaling in cloud environments.
Challenges of Horizontal Scaling
Application must support distribution. Stateful applications storing data on individual nodes require significant rearchitecting before they can scale horizontally.
Increased operational complexity. Managing clusters, load balancers, service discovery, inter-node communication, and distributed tracing requires dedicated tooling and expertise.
Data consistency challenges. Maintaining consistency across distributed nodes requires careful design — particularly for databases and shared state.
Network overhead. Inter-node calls add latency compared to in-process function calls. This is acceptable for most workloads but problematic for ultra-low-latency requirements.
When Horizontal Scaling Is the Right Choice
Scale Out
SaaS Applications with Variable Load
Web apps and APIs experiencing unpredictable or seasonal demand spikes. Auto-scaling adds nodes during peaks and removes them during troughs.
Scale Out
Microservices Architectures
Each service can be scaled independently based on its own demand profile — eliminating the waste of scaling the entire application for bottlenecks in one component.
Scale Out
Big Data Processing Pipelines
Distributed computing frameworks like Apache Spark or Hadoop are purpose-built for horizontal scaling, splitting large jobs across many worker nodes in parallel.
Scale Out
Content Delivery Networks
CDNs distribute content to edge servers globally. Adding nodes in new regions reduces latency for regional users and increases total throughput capacity.
Head-to-Head Comparison: Horizontal vs. Vertical Scaling
DimensionVertical Scaling (Scale Up)Horizontal Scaling (Scale Out)How it worksIncrease resources on existing serverAdd more servers to the poolCapacity ceilingHard ceiling (max hardware spec)Theoretically unlimitedFault toleranceLow — single point of failureHigh — redundant nodesDowntime riskPossible during upgradesMinimal — nodes added liveImplementation complexityLow — no code changes neededHigh — requires distributed architectureCost at scaleExpensive at high tiersCost-efficient with commodity hardwareAuto-scaling supportLimitedNative in cloud environmentsBest forMonolithic apps, low-latency, legacy systemsDistributed apps, microservices, variable loadData consistencySimple — single data storeComplex — requires distributed consistency patternsGeographic distributionNot possible by designNative support for multi-regionHorizontal vs. Vertical Scaling
Auto-Scaling: The Evolution of Infrastructure Scalability
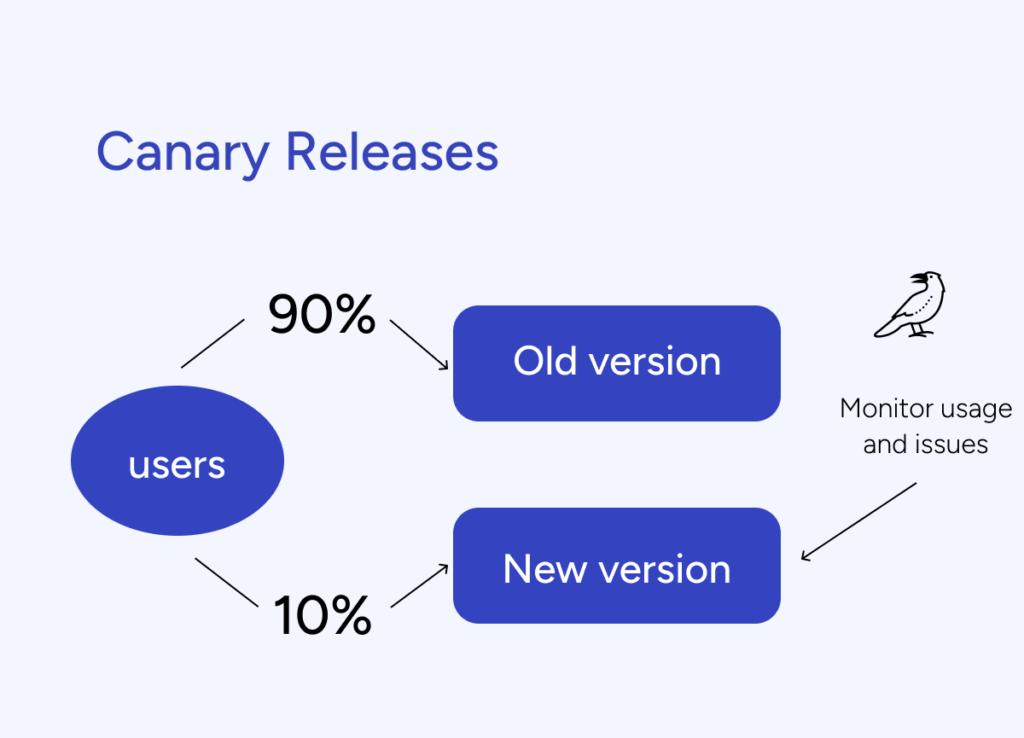
Manual scaling — whether vertical or horizontal — requires human decisions and action. Auto-scaling removes the human from the loop, automatically adjusting infrastructure capacity based on real-time demand signals. It is the operationalization of horizontal scalability in cloud environments.
Modern infrastructure scalability strategies are built around three auto-scaling approaches:
1. Reactive Auto-Scaling
The most common form. The system monitors metrics (CPU utilization, memory, request queue depth, response time) and triggers scaling actions when thresholds are crossed. AWS Auto Scaling Groups, Azure Virtual Machine Scale Sets, and Kubernetes Horizontal Pod Autoscaler (HPA) all operate reactively.
Example
A web application scales from 3 to 12 pods when average CPU utilization across the cluster exceeds 70% for 2 consecutive minutes. When utilization drops below 30%, it scales back to 3 pods over a cooldown period.
2. Predictive Auto-Scaling
Machine learning models analyze historical load patterns to predict future demand and pre-provision resources ahead of anticipated traffic spikes. AWS Predictive Scaling uses this approach, training on your application's historical CloudWatch metrics.
Predictive scaling is particularly valuable for workloads with consistent patterns — e-commerce sites with known peak shopping hours, SaaS tools with business-hours usage patterns, or media platforms with event-driven traffic surges.
3. Scheduled Auto-Scaling
For completely predictable load patterns, scheduled scaling sets specific capacity values at specific times. A company that knows from experience that traffic triples at 9 AM UTC every weekday can pre-scale at 8:45 AM — eliminating the cold-start lag of reactive scaling.
Kubernetes and Container-Native Scalability
Kubernetes has become the de facto infrastructure scalability platform for containerized workloads. It provides three complementary scaling mechanisms that work together:
Horizontal Pod Autoscaler (HPA): Scales the number of pod replicas based on CPU, memory, or custom metrics. This is horizontal scaling at the application layer.
Vertical Pod Autoscaler (VPA): Adjusts CPU and memory requests/limits for containers based on historical usage. This is vertical scaling at the container layer.
Cluster Autoscaler: Adds or removes worker nodes from the cluster itself based on pod scheduling pressure. This is horizontal scaling at the infrastructure layer.
Kubernetes Scalability Architecture
A production-grade Kubernetes deployment combining all three autoscalers achieves both vertical efficiency (VPA right-sizes containers) and horizontal resilience (HPA + Cluster Autoscaler handle demand spikes) — representing the state of the art in modern infrastructure scalability.
Hybrid Scaling: The Production Reality
Real-world infrastructure scalability is rarely purely horizontal or purely vertical. Most mature production architectures combine both approaches, applying the right strategy at each layer of the stack:
Stack LayerCommon Scaling ApproachRationaleWeb/API tierHorizontal (auto-scaling)Stateless; auto-scaling trivially adds/removes instancesApplication logicHorizontal (microservices)Independent services scale based on individual demandPrimary databaseVertical first, then read replicasWrite path benefits from powerful single instance; read scaling via replicasCache layerVertical (larger RAM instances)In-memory cache performance scales directly with RAMMessage queuesHorizontal (partitioning)Kafka/RabbitMQ throughput scales by adding partitions/consumersObject storageHorizontal (managed service)S3/Azure Blob scales infinitely; abstracted by providerBatch processingHorizontal (worker pools)Jobs parallelized across many workers; ephemeral scaling idealHybrid Scaling: The Production Reality
"The question is never 'which scaling approach is better?' — it's 'which scaling approach is right for this workload, at this tier, at this stage of growth?' Mature infrastructure scalability requires architectural nuance, not dogma." — Fedir Kompaniiets, Co-founder, Gart Solutions
Infrastructure Scalability Decision Framework
The right scaling strategy is not a matter of preference — it follows from the specific characteristics of your workload, team, and growth trajectory. Use this decision framework before committing to a scaling approach:
5-Question Scalability Decision Framework
Is the workload stateful or stateless?Stateless → horizontal scaling is straightforward. Stateful → evaluate distributed state management complexity before choosing horizontal, or favor vertical for simplicity.
Is demand predictable or variable?Predictable & bounded → vertical scaling may be sufficient and more cost-effective. Variable or spiky → horizontal scaling with auto-scaling is essential to avoid over-provisioning.
What are the latency requirements?Ultra-low latency (<1ms) → vertical scaling or co-located horizontal nodes. Standard web latency → horizontal scaling with load balancing works well.
What is the fault tolerance requirement?Mission-critical, zero downtime → horizontal scaling with redundancy is mandatory. Scheduled maintenance acceptable → vertical scaling may be viable.
What is the growth trajectory?Limited, known growth → vertical scaling handles this cleanly. Rapid or unbounded growth → horizontal scaling prevents the escalating cost and disruption of repeated hardware upgrades.
Industry-Specific Scalability Patterns
E-Commerce
E-commerce platforms face the classic variable load problem: normal traffic during weekdays, massive spikes during sales events and holidays. The optimal infrastructure scalability pattern is horizontal for the web/application tier with reactive auto-scaling, combined with vertical for the primary transactional database, supplemented by read replicas for product catalog queries.
Financial Services
Payment processing and trading platforms have extreme reliability and latency requirements. vertical scaling with premium hardware for the critical transaction path, horizontal for fraud detection microservices and reporting workloads, with active-active geographic redundancy for business continuity.
Healthcare Technology
Healthcare platforms combine predictable baseline load (scheduled appointments, EHR access) with unpredictable spikes (emergency systems). Hybrid approach: vertically scaled core clinical databases (consistency and latency critical), horizontally scaled patient-facing APIs, with strict data sovereignty controls limiting geographic distribution options.
SaaS Platforms
Multi-tenant SaaS products are the native home of horizontal scaling. Tenant workloads are isolated, stateless application tiers scale out during business hours, and per-tenant database strategies (shared vs. dedicated) allow granular infrastructure scalability at the data layer.
Infrastructure Scalability and Cost Optimization
Scaling decisions have direct financial consequences. An infrastructure that scales incorrectly — either under-provisioned or over-provisioned — causes measurable business harm. Building cost awareness into scalability strategy is non-negotiable.
The Over-Provisioning Problem
Traditional on-premise infrastructure forces teams to size for peak load. A server cluster capable of handling Black Friday traffic sits at 10–15% utilization for 350 days of the year. This is structural waste embedded in the infrastructure design.
Cloud-native horizontal scaling solves this: auto-scaling groups provision capacity on demand and deprovision it when the spike passes. Done well, this eliminates the peak-sizing premium entirely.
Reserved vs. On-Demand Capacity
A mature infrastructure scalability cost strategy combines three capacity tiers:
Reserved instances (1–3 year commitments) for predictable baseline load — delivering 30–60% savings vs. on-demand pricing.
On-demand instances for the variable load band between baseline and peak — paying only for what is used.
Spot/preemptible instances for fault-tolerant batch workloads and non-critical processing — up to 90% cost reduction vs. on-demand.
💰 Cost ImpactOrganizations that implement proper horizontal auto-scaling with a tiered capacity purchasing strategy consistently report 40–65% reductions in compute costs compared to statically provisioned vertical infrastructure sized for peak load.
FinOps and Scalability
Infrastructure scalability and cloud financial management (FinOps) are deeply interconnected. Scaling decisions that look technically correct can be financially destructive without proper cost governance:
Tag all scaling groups with team, service, and environment to attribute costs accurately
Set budget alerts that trigger at 80% of monthly targets — before costs spiral
Review scaling policies monthly; demand patterns evolve and policies become stale
Measure cost-per-unit-of-value (cost per transaction, cost per user) not just absolute spend
Run rightsizing analysis quarterly — vertical over-provisioning compounds silently
Modern Infrastructure Scalability: Serverless and Beyond
The horizontal/vertical dichotomy is evolving. A new generation of infrastructure abstractions removes scaling decisions from the operator entirely:
Serverless Computing
AWS Lambda, Azure Functions, and Google Cloud Run abstract infrastructure scaling completely. The platform scales from zero to thousands of concurrent executions automatically. The developer writes functions; the cloud manages provisioning. This is the logical endpoint of horizontal scaling taken to its extreme — infinite theoretical scale, zero operational overhead for capacity management.
The tradeoff: cold starts, execution time limits, and architectural constraints make serverless unsuitable for long-running, stateful, or latency-critical workloads. It is optimal for event-driven, short-duration, stateless functions.
Database Scalability Patterns
Databases are traditionally the hardest layer to scale horizontally. Modern approaches include:
Read replicas: Horizontal read scaling — offload read queries to replicas while writes hit the primary instance.
Sharding: Partition data across multiple database nodes based on a shard key. Enables horizontal scaling of writes but adds application-level complexity.
NewSQL databases (CockroachDB, PlanetScale, Vitess): Combine SQL semantics with distributed horizontal scalability — the best of both worlds for transactional workloads.
CQRS + Event Sourcing: Architectural patterns that separate read and write models, enabling each to scale independently and asymmetrically.
Infrastructure Scalability in Kubernetes
Kubernetes has become the standard runtime for horizontally scalable workloads. Key scalability capabilities include:
Horizontal Pod Autoscaler
Vertical Pod Autoscaler
Cluster Autoscaler
KEDA (Event-Driven Autoscaling)
Pod Disruption Budgets
Node Affinity Rules
Topology Spread Constraints
Resource Quotas
KEDA (Kubernetes Event-Driven Autoscaling) extends HPA to scale based on external event sources — queue depth in SQS, topics in Kafka, or custom metrics from Prometheus. This enables true demand-driven scalability beyond CPU/memory thresholds.
Choosing the Right Infrastructure Scalability Strategy
The decision between horizontal and vertical scaling — or a hybrid approach — should be based on a systematic assessment of your workload, not intuition or convention. The right answer varies by application, by layer, by growth stage, and by team capability.
Start Small, Monitor, Then Scale
The single most valuable infrastructure scalability practice is instrumentation before scaling decisions. You cannot optimize what you cannot measure. Before choosing how to scale, establish:
Baseline performance metrics under normal load (p50, p95, p99 latencies)
Resource utilization patterns over time (CPU, memory, disk I/O, network)
Identified bottlenecks — is performance limited by compute, memory, I/O, or network?
User-facing SLOs and how current headroom compares to them
This data transforms scaling from guesswork into an evidence-based engineering decision.
Scalability Is an Architecture Concern, Not an Operations Reaction
The most expensive infrastructure scalability scenarios are those that require urgent reactive decisions under pressure. Teams that build scalability thinking into their architecture from the start — designing for statelessness, separating concerns, building in observability — avoid the costly, risky emergency retrofits that plague systems designed without growth in mind.
Best Practices Summary
Design stateless where possible — it unlocks horizontal scalability. Scale databases last, and carefully — data layer scaling is hardest. Combine vertical baseline with horizontal peak handling — hybrid architectures are the production norm. Automate scaling decisions — human reaction time is too slow for modern traffic patterns. Monitor cost alongside performance — scalability without financial governance is waste.
How Gart Can Help You with Cloud Scalability
Ultimately, the determining factors are your cloud needs and cost structure. Without the ability to predict the true aspects of these components, each business can fall into the trap of choosing the wrong scaling strategy for them. Therefore, cost assessment should be a priority. Additionally, optimizing cloud costs remains a complex task regardless of which scaling system you choose.
Here are some ways Gart can help you with cloud scalability:
Assess your cloud needs and cost structure: We can help you understand your current cloud usage and identify areas where you can optimize your costs.
Develop a cloud scaling strategy: We can help you choose the right scaling approach for your specific needs and budget.
Implement your cloud scaling strategy: We can help you implement your chosen scaling strategy and provide ongoing support to ensure that it meets your needs.
Optimize your cloud costs: We can help you identify and implement cost-saving measures to reduce your cloud bill.
Gart has a team of experienced cloud experts who can help you with all aspects of cloud scalability. We have a proven track record of helping businesses optimize their cloud costs and improve their cloud performance.
Contact Gart today to learn more about how we can help you with cloud scalability.
We look forward to hearing from you!
Fedir Kompaniiets
Co-founder & CEO, Gart Solutions · Cloud Architect & DevOps Consultant
Fedir is a technology enthusiast with over a decade of diverse industry experience. He co-founded Gart Solutions to address complex tech challenges related to Digital Transformation, helping businesses focus on what matters most — scaling. Fedir is committed to driving sustainable IT transformation, helping SMBs innovate, plan future growth, and navigate the "tech madness" through expert DevOps and Cloud managed services. Connect on LinkedIn.
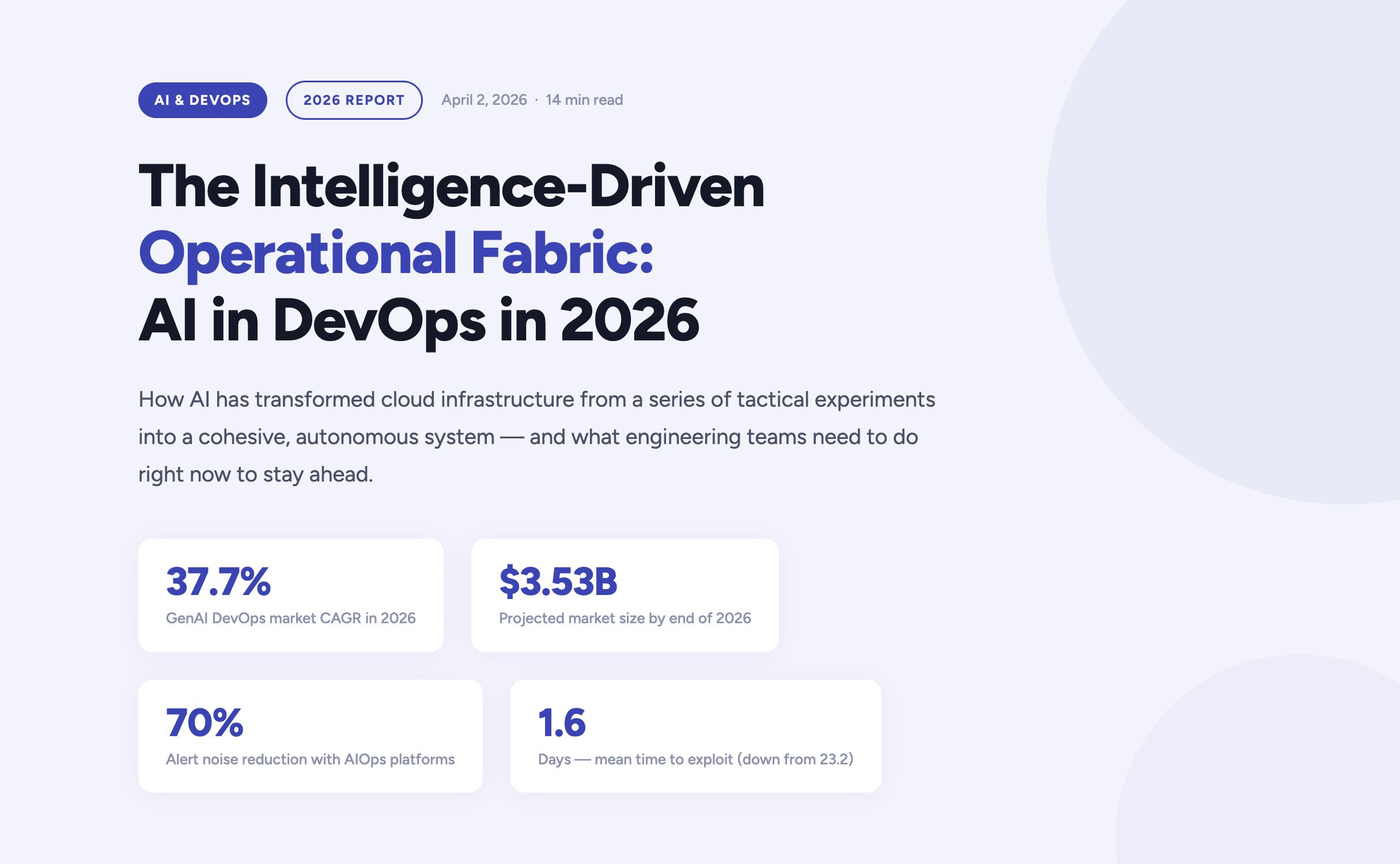
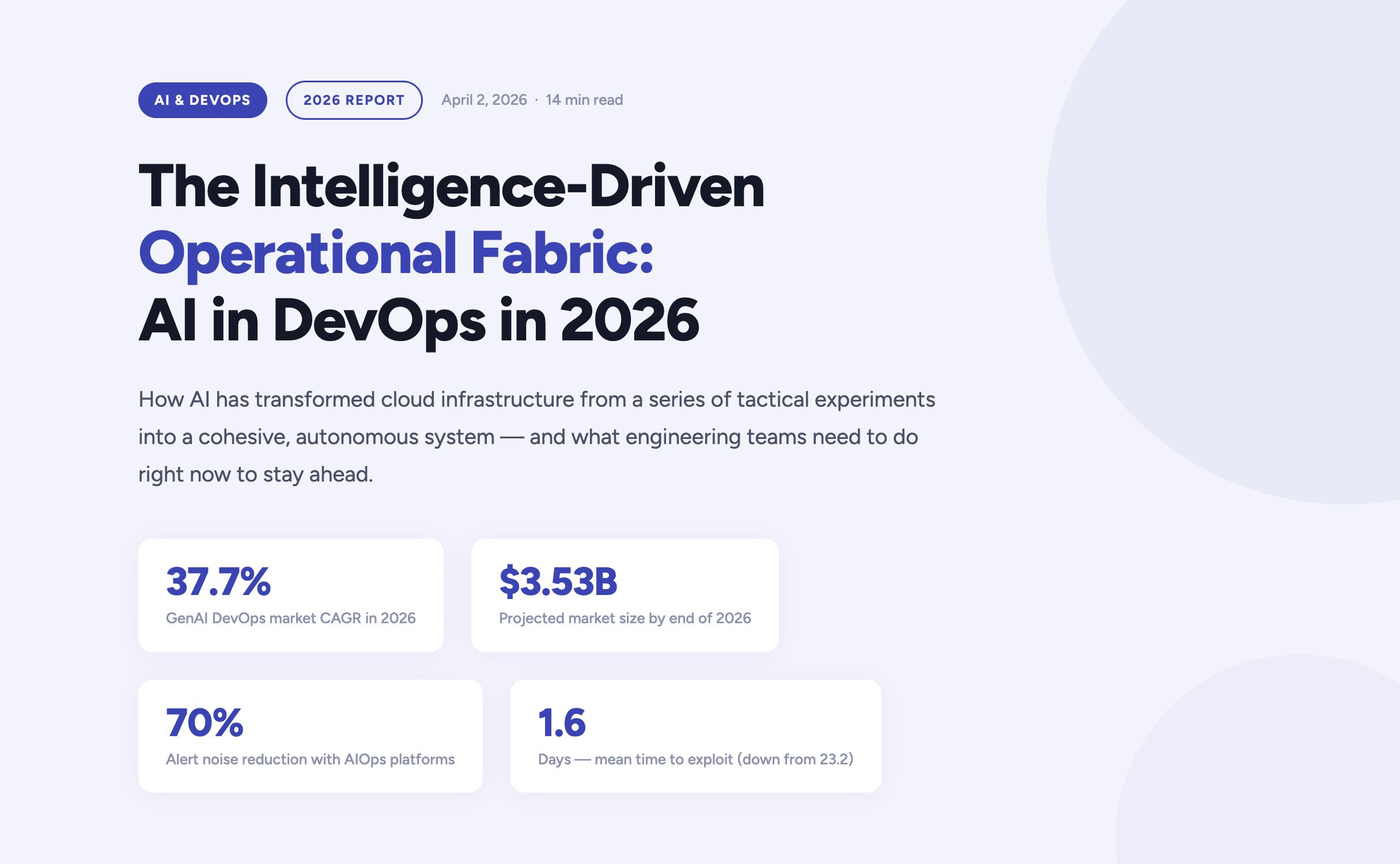
The year 2026 marks a definitive turning point in how enterprises build, deploy, and operate software. Artificial Intelligence has moved far beyond the experimental phase inside DevOps pipelines — it now forms the connective tissue of the entire software delivery lifecycle. According to current market analysis, the generative AI segment of the DevOps market is growing at a compound annual rate of 37.7%, expected to reach $3.53 billion by the end of this year alone.
For engineering teams, platform engineers, and CTOs navigating this shift, the questions are no longer "should we adopt AI?" but rather "how do we govern it?", "where does it amplify our strengths?", and critically — "where does it expose our weaknesses?". This article answers those questions, grounded in the realities of operating cloud infrastructure in 2026.
https://youtu.be/4FNyMRmHdTM?si=F2yOv89QU9gQ7Hif
The AI velocity paradox — why more code isn't always better
One of the most striking findings in the 2026 DevOps landscape is what researchers have begun calling the AI Velocity Paradox. AI-assisted coding tools have dramatically accelerated the code creation phase of the Software Development Life Cycle. However, the downstream delivery systems responsible for testing, securing, and deploying that code have often failed to keep pace — creating a structural mismatch between production and operations capacity.
The data tells a clear story. Teams that use AI coding tools daily are three times more likely to deploy frequently — but they also report significantly higher rates of quality failures, security incidents, and engineer burnout.
The AI DevOps maturity gap — occasional vs. daily AI tool users
The AI DevOps Maturity Gap — 2026 Analysis
Performance Indicator
Occasional AI Usage
Daily AI Usage
Daily deployment frequency
15% of teams
45% of teams
Frequent deployment issues
Minimal
69% of teams
Mean Time to Recovery (MTTR)
6.3 hours
7.6 hours
Quality / security problems
Baseline
51% quality / 53% security
Engineers working overtime
66%
96%
The root cause is structural: a "six-lane highway" of AI-accelerated code generation is funneling into a "two-lane bridge" of operational capacity. Engineers spend an average of 36% of their time on repetitive manual tasks — chasing tickets, rerunning failed jobs, manually validating AI-generated code — while developer burnout now affects 47% of the engineering workforce.
The implication is clear: AI does not automatically improve DevOps outcomes. Applied to brittle pipelines or fragmented telemetry, it accelerates instability. Applied to robust, standardized foundations, it becomes a force multiplier. The organizations that succeed in 2026 are those that modernize their entire delivery system — not just the IDE.
Tech should do more than work — it should do good, and it should scale purposefully."
Fedir Kompaniiets, CEO, Gart Solutions
Intent-to-Infrastructure — the evolution of IaC
Infrastructure as Code has been a DevOps cornerstone for years, but the model is undergoing a fundamental transformation in 2026. The industry is moving away from hand-crafted Terraform scripts and declarative state management toward what practitioners call Intent-to-Infrastructure — AI-powered platforms that interpret high-level business requirements and autonomously provision compliant, cost-optimized environments.
The evolution of Infrastructure as Code
The Evolution of Infrastructure as Code
Generation
Primary Mechanism
Governance Model
Outcome Focus
IaC 1.0 — Legacy
Manual scripting (Terraform, Ansible)
Periodic manual audits
Resource provisioning
IaC 2.0 — Standard
Declarative state management
Automated policy checks
Environment consistency
Intent-Driven (2026)
AI translation of requirements
Continuous autonomous reconciliation
Business-aligned outcomes
In the intent-driven model, a developer can express a requirement in plain language — for example, "provision a production-ready Kubernetes cluster with SOC 2-compliant networking for our EU-West workload" — and the platform autonomously generates, validates, and manages the resources. Compliance is no longer a retrospective audit exercise; it is embedded at the moment of generation.
This approach directly addresses one of the most persistent gaps in enterprise cloud governance: the Confidence Gap. While 77% of organizations report confidence in their AI-generated infrastructure, only 39% maintain the fully automated audit trails needed to actually verify those outputs. Intent-driven platforms close this gap by creating immutable, traceable records of every provisioning decision.
Key IaC Capabilities in 2026
Natural language provisioning — Describe infrastructure requirements in plain English, receiving validated, compliant Terraform or Pulumi code.
Golden path enforcement — Pre-approved patterns ensure every environment is secure by default, reducing misconfiguration risk.
Continuous autonomous reconciliation — AI continuously monitors for drift and self-corrects without human intervention.
Policy-as-code integration — OPA, Sentinel, and custom guardrails are embedded into generation pipelines, not added as an afterthought.
Cost-aware provisioning — FinOps constraints are applied at generation time, preventing over-provisioning before it happens.
AIOps and the new era of observability
As cloud-native architectures scale in complexity, the challenge facing modern platform engineers is no longer the collection of telemetry data — it is the meaningful interpretation of it. According to Gartner, over 60% of production incidents in 2026 are caused by poor interpretation of existing data, not a lack of visibility. Teams are drowning in signals while missing the meaning.
This has driven the rapid maturation of AIOps — Artificial Intelligence for IT Operations — which shifts the operational model from reactive incident firefighting to predictive, self-healing systems. Modern AIOps platforms in 2026 are built on three core capabilities:
Predictive incident management
AI models trained on historical delivery patterns, change velocity data, and error logs can now surface probabilistic risk assessments hours before a service outage occurs. Rather than reacting to pages at 3am, platform teams receive prioritized warnings during business hours with recommended remediation paths.
Autonomous remediation
For well-understood failure patterns — pod OOMKill events, connection pool exhaustion, SSL certificate expiry — AI agents can execute validated runbooks autonomously, patching or scaling systems within seconds of detection. Human intervention is reserved for novel or high-impact scenarios.
Intelligent alert prioritization
By correlating weak signals across application, infrastructure, and network layers, modern AIOps platforms reduce alert noise by up to 70%. Engineers no longer triage a wall of Slack notifications — they engage with a curated, context-rich incident queue.
60%+
Incidents from misinterpretation
70%
Less alert noise via AIOps
36%
Engineer time lost to manual tasks
eBPF
Deep visibility sans code changes
DevSecOps 2.0 — when autonomous security becomes non-negotiable
The security landscape of 2026 is unforgiving. The mean time to exploit a known vulnerability has collapsed from 23.2 days in 2025 to just 1.6 days — faster than any human-speed security process can respond. This has driven a fundamental rearchitecting of DevSecOps, from a set of "shift left" practices to a fully autonomous, self-healing security model.
Traditional vs. AI-Enhanced DevSecOps
Security Metric
Traditional DevSecOps
AI-Enhanced DevSecOps (2026)
Vulnerability identification
Periodic scanning of dependencies
Real-time scanning of code, containers, and runtimes
Threat response
Manual triage and incident response
Automated isolation of compromised resources
Compliance evidence
Manual spreadsheet collection
Automated, immutable audit trails
Risk assessment
Static CVSS vulnerability scoring
Contextual scoring based on reachability and blast radius
For regulated industries — healthcare, financial services, legal — compliance is no longer a quarterly exercise. In 2026, the most resilient organizations implement Compliance-by-Design infrastructure, where HIPAA, HITECH, SOC 2, and PCI-DSS controls are embedded directly into DevOps pipelines. Every commit, every deployment, every configuration change produces a verifiable, immutable compliance artifact — not as overhead, but as a natural byproduct of the engineering workflow.
The shift is cultural as well as technical: compliance is now understood as a growth enabler, not a hindrance. Organizations that can demonstrate real-time security posture attract enterprise customers, pass procurement audits, and move faster through regulated markets.
FinOps and the economics of intelligent infrastructure
Cloud spending has become a top-five P&L line item for most mid-to-large enterprises in 2026. Uncontrolled SaaS sprawl, over-provisioned Kubernetes clusters, and idle development environments have made AI-driven FinOps not just a cost-optimization strategy, but a boardroom-level priority.
The latest generation of FinOps tooling applies AI in two directions: reactive optimization (identifying and eliminating waste in existing infrastructure) and proactive cost governance (embedding unit cost constraints into provisioning workflows before resources are ever created). The results are significant — in some cases, organizations achieve savings of up to 80% on AWS compute budgets through spot instance migration, rightsizing, and automated idle resource termination.
Increasingly, FinOps and sustainability are being treated as two sides of the same coin. By eliminating idle compute and over-provisioned infrastructure, organizations simultaneously reduce cloud spend and digital carbon footprint — what practitioners are calling Green FinOps. At Gart Solutions, 70% of client workloads are optimized to run on green cloud platforms as part of a carbon-neutral-by-default infrastructure strategy.
"Applied to brittle pipelines or fragmented telemetry, AI accelerates instability. Applied to robust, standardized foundations, it becomes the force multiplier that allows organizations to scale resilience at the speed of code."
Roman Burdiuzha, CTO, Gart Solutions
Human-on-the-Loop governance — the new control model
As AI agents take over increasing portions of the operational layer, one of the defining debates of 2026 is where to draw the line on autonomy. The industry consensus has moved away from both extremes — fully manual "Human-in-the-Loop" (HITL) processes that create bottlenecks, and fully autonomous systems that introduce unacceptable risk — toward a middle path: Human-on-the-Loop (HOTL) governance.
In the HOTL model, AI agents operate autonomously within predefined guardrails. Humans shift from being operators to being overseers — setting policies, reviewing exceptions, and vetoing high-stakes decisions. The architecture is built on four pillars:
Step and cost thresholds — Hard limits on the number of actions an agent can execute per session, or the total tokens consumed, prevent infinite loops and runaway infrastructure costs.
The Veto Protocol — For high-risk decisions (budget reallocations, production changes above a defined blast radius), the agent surfaces a structured "Decision Summary" for asynchronous human review before proceeding.
Identity and access control — Agents are granted short-lived, task-scoped credentials. They never hold standing access to production environments; every session is authenticated, logged, and time-bounded.
Immutable audit trails — Every agent action generates a cryptographically signed record, ensuring full traceability for compliance and post-incident review.
This governance model is not a limitation on AI capability — it is what makes AI capability trustworthy enough to deploy at scale in regulated, high-stakes environments.
Industry-specific transformations
Manufacturing — the intelligent shop floor
Manufacturing organizations face a persistent challenge: deeply siloed data environments where Management Execution Systems (MES), ERP platforms, IoT sensor networks, and POS systems rarely communicate in real time. In 2026, cloud-native, AI-powered integration layers are dissolving these silos — enabling predictive maintenance, real-time production analytics, and supply chain transparency from raw material to finished product.
For one manufacturing client, a custom Green FinOps strategy eliminated over-provisioned infrastructure while a blockchain-based supply chain integration created end-to-end product traceability. The combined impact: measurable cost savings, improved regulatory compliance, and a more resilient operational model.
Healthcare — securing the patient data journey
In healthcare, the stakes of a misconfigured infrastructure are clinical as well as financial. DevOps practices in this sector are purpose-built around securing electronic health records, ensuring FDA and HIPAA compliance, and protecting medical device software against zero-day vulnerabilities. AI-driven monitoring continuously scans for "blind spots" that could lead to clinical data loss — not just at deployment time, but across the full runtime lifecycle.
SaaS and fintech — scaling without headcount sprawl
SaaS companies and fintech startups are increasingly turning to DevOps-as-a-Service to manage global availability and rapid iteration cycles without proportional growth in engineering headcount. By embedding automated security tasks, infrastructure-as-code provisioning, and AI-driven observability into every deployment, these teams can scale their products while maintaining the operational quality standards that enterprise customers demand.
Build your intelligent operational fabric
Partner with Gart Solutions for resilient, AI-powered cloud infrastructure.
Talk to an engineer →
Your 2026 AI DevOps roadmap
Organizations that are successfully navigating the AI transition in 2026 share a common pattern. They did not bolt AI onto existing processes — they built the foundations first, then amplified them. The roadmap has four distinct stages:
Data readiness audit
Ensure that observability data — logs, metrics, traces, events — is clean, normalized, and accessible across organizational silos. AI models are only as good as the telemetry they consume. Fragmented, noisy data produces fragmented, unreliable AI recommendations.
High-ROI use case selection
Start with workflows where AI delivers measurable, auditable value — automated testing, incident triage, IaC generation, cost anomaly detection. Build confidence and governance muscle before expanding to higher-risk autonomous operations.
Governance architecture
Establish the guardrails — HOTL oversight protocols, agent identity controls, immutable audit trails, cost thresholds — before deploying autonomous agents into production environments. Governance is not friction; it is what makes speed sustainable.
AI fluency across the engineering organization
Develop the skills required to oversee, interact with, and continuously improve intelligent agents. The competitive advantage in 2027 will belong to teams that can govern AI effectively — not just deploy it.
The 2026 AI-native DevOps toolchain
The toolchain of 2026 is defined by intelligence at every stage of the delivery pipeline. Unlike earlier generations of tooling that added AI as an afterthought, these platforms are AI-native — built from the ground up to learn, adapt, and act autonomously.
The AI DevOps Tooling Landscape (2026)
Tool
Domain
Key AI Capability
Snyk
Security
Real-time AI scanning for dependencies, containers, and IaC
Spacelift
Infrastructure
Multi-tool IaC management with AI policy enforcement
Harness
CI/CD
Intelligent software delivery with autonomous deployment verification
Datadog
Monitoring
AI-augmented full-stack visibility, anomaly detection, log correlation
PagerDuty
Incident Management
ML-based event correlation and intelligent noise reduction
StackGen
Platform Eng.
AI-powered intent-to-infrastructure generation
K8sGPT
Kubernetes
Natural language explanation and diagnosis of cluster errors
Sysdig Sage
DevSecOps
AI analyst for runtime security threat detection and CNAPP
Cast AI
FinOps
Autonomous Kubernetes cost optimization and rightsizing
Conclusion — from manual doers to intelligent orchestrators
The convergence of AI and DevOps in 2026 has redefined what is possible in software delivery. The organizations that thrive are not those that deploy the most AI tools — they are those that build the most resilient foundations and then amplify those foundations intelligently. Cloud infrastructure is no longer a hosting environment. It is an intelligent fabric that predicts, learns, and self-heals.
The transition is as cultural as it is technical. Engineering teams are moving from being manual operators to being intelligent orchestrators — governing not through a queue of tickets, but through the strategic definition of intent and the rigorous enforcement of outcomes. For those willing to make this shift, the competitive advantage is significant, durable, and compounding.
As Gart Solutions has built its entire practice around: tech should do more than work — it should do good, and it should scale purposefully.
Build your intelligent operational fabric with us
A boutique DevOps and cloud infrastructure partner for engineering teams that want to scale reliably, securely, and sustainably — without the overhead of a hyperscaler.
DevOps as a Service
Full-lifecycle CI/CD design, automation, and platform engineering for teams that need reliable, battle-tested delivery pipelines at startup speed.
Cloud migration & adoption
Strategic migration from on-premise or legacy cloud environments to modern, cost-optimized, and green cloud architectures on AWS, GCP, or Azure.
DevSecOps automation
Compliance-by-design infrastructure for regulated industries — embedding HIPAA, SOC 2, and PCI-DSS controls directly into your delivery pipeline.
AIOps & observability
End-to-end observability strategy — from eBPF telemetry and distributed tracing to AI-powered alerting, anomaly detection, and autonomous runbook execution.
FinOps & cloud cost optimization
Cloud cost audits, spot instance migration, idle resource termination, and Kubernetes rightsizing — achieving savings of up to 80% on cloud budgets.
Managed infrastructure
24/7 proactive management of your cloud infrastructure, with SLA-backed uptime guarantees, automated scaling, and continuous compliance monitoring.

In my experience optimizing cloud costs, especially on AWS, I often find that many quick wins are in the "easy to implement - good savings potential" quadrant.
[lwptoc]
That's why I've decided to share some straightforward methods for optimizing expenses on AWS that will help you save over 80% of your budget.
Choose reserved instances
Potential Savings: Up to 72%
Choosing reserved instances involves committing to a subscription, even partially, and offers a discount for long-term rentals of one to three years. While planning for a year is often deemed long-term for many companies, especially in Ukraine, reserving resources for 1-3 years carries risks but comes with the reward of a maximum discount of up to 72%.
You can check all the current pricing details on the official website - Amazon EC2 Reserved Instances
Purchase Saving Plans (Instead of On-Demand)
Potential Savings: Up to 72%
There are three types of saving plans: Compute Savings Plan, EC2 Instance Savings Plan, SageMaker Savings Plan.
AWS Compute Savings Plan is an Amazon Web Services option that allows users to receive discounts on computational resources in exchange for committing to using a specific volume of resources over a defined period (usually one or three years). This plan offers flexibility in utilizing various computing services, such as EC2, Fargate, and Lambda, at reduced prices.
AWS EC2 Instance Savings Plan is a program from Amazon Web Services that offers discounted rates exclusively for the use of EC2 instances. This plan is specifically tailored for the utilization of EC2 instances, providing discounts for a specific instance family, regardless of the region.
AWS SageMaker Savings Plan allows users to get discounts on SageMaker usage in exchange for committing to using a specific volume of computational resources over a defined period (usually one or three years).
The discount is available for one and three years with the option of full, partial upfront payment, or no upfront payment. EC2 can help save up to 72%, but it applies exclusively to EC2 instances.
Utilize Various Storage Classes for S3 (Including Intelligent Tier)
Potential Savings: 40% to 95%
AWS offers numerous options for storing data at different access levels. For instance, S3 Intelligent-Tiering automatically stores objects at three access levels: one tier optimized for frequent access, 40% cheaper tier optimized for infrequent access, and 68% cheaper tier optimized for rarely accessed data (e.g., archives).
S3 Intelligent-Tiering has the same price per 1 GB as S3 Standard — $0.023 USD.
However, the key advantage of Intelligent Tiering is its ability to automatically move objects that haven't been accessed for a specific period to lower access tiers.
Every 30, 90, and 180 days, Intelligent Tiering automatically shifts an object to the next access tier, potentially saving companies from 40% to 95%. This means that for certain objects (e.g., archives), it may be appropriate to pay only $0.0125 USD per 1 GB or $0.004 per 1 GB compared to the standard price of $0.023 USD.
Information regarding the pricing of Amazon S3
AWS Compute Optimizer
Potential Savings: quite significant
The AWS Compute Optimizer dashboard is a tool that lets users assess and prioritize optimization opportunities for their AWS resources.
The dashboard provides detailed information about potential cost savings and performance improvements, as the recommendations are based on an analysis of resource specifications and usage metrics.
The dashboard covers various types of resources, such as EC2 instances, Auto Scaling groups, Lambda functions, Amazon ECS services on Fargate, and Amazon EBS volumes.
For example, AWS Compute Optimizer reproduces information about underutilized or overutilized resources allocated for ECS Fargate services or Lambda functions. Regularly keeping an eye on this dashboard can help you make informed decisions to optimize costs and enhance performance.
Use Fargate in EKS for underutilized EC2 nodes
If your EKS nodes aren't fully used most of the time, it makes sense to consider using Fargate profiles. With AWS Fargate, you pay for a specific amount of memory/CPU resources needed for your POD, rather than paying for an entire EC2 virtual machine.
For example, let's say you have an application deployed in a Kubernetes cluster managed by Amazon EKS (Elastic Kubernetes Service). The application experiences variable traffic, with peak loads during specific hours of the day or week (like a marketplace or an online store), and you want to optimize infrastructure costs. To address this, you need to create a Fargate Profile that defines which PODs should run on Fargate. Configure Kubernetes Horizontal Pod Autoscaler (HPA) to automatically scale the number of POD replicas based on their resource usage (such as CPU or memory usage).
Manage Workload Across Different Regions
Potential Savings: significant in most cases
When handling workload across multiple regions, it's crucial to consider various aspects such as cost allocation tags, budgets, notifications, and data remediation.
Cost Allocation Tags: Classify and track expenses based on different labels like program, environment, team, or project.
AWS Budgets: Define spending thresholds and receive notifications when expenses exceed set limits. Create budgets specifically for your workload or allocate budgets to specific services or cost allocation tags.
Notifications: Set up alerts when expenses approach or surpass predefined thresholds. Timely notifications help take actions to optimize costs and prevent overspending.
Remediation: Implement mechanisms to rectify expenses based on your workload requirements. This may involve automated actions or manual interventions to address cost-related issues.
Regional Variances: Consider regional differences in pricing and data transfer costs when designing workload architectures.
Reserved Instances and Savings Plans: Utilize reserved instances or savings plans to achieve cost savings.
AWS Cost Explorer: Use this tool for visualizing and analyzing your expenses. Cost Explorer provides insights into your usage and spending trends, enabling you to identify areas of high costs and potential opportunities for cost savings.
Transition to Graviton (ARM)
Potential Savings: Up to 30%
Graviton utilizes Amazon's server-grade ARM processors developed in-house. The new processors and instances prove beneficial for various applications, including high-performance computing, batch processing, electronic design automation (EDA) automation, multimedia encoding, scientific modeling, distributed analytics, and machine learning inference on processor-based systems.
The processor family is based on ARM architecture, likely functioning as a system on a chip (SoC). This translates to lower power consumption costs while still offering satisfactory performance for the majority of clients. Key advantages of AWS Graviton include cost reduction, low latency, improved scalability, enhanced availability, and security.
Spot Instances Instead of On-Demand
Potential Savings: Up to 30%
Utilizing spot instances is essentially a resource exchange. When Amazon has surplus resources lying idle, you can set the maximum price you're willing to pay for them. The catch is that if there are no available resources, your requested capacity won't be granted.
However, there's a risk that if demand suddenly surges and the spot price exceeds your set maximum price, your spot instance will be terminated.
Spot instances operate like an auction, so the price is not fixed. We specify the maximum we're willing to pay, and AWS determines who gets the computational power. If we are willing to pay $0.1 per hour and the market price is $0.05, we will pay exactly $0.05.
Use Interface Endpoints or Gateway Endpoints to save on traffic costs (S3, SQS, DynamoDB, etc.)
Potential Savings: Depends on the workload
Interface Endpoints operate based on AWS PrivateLink, allowing access to AWS services through a private network connection without going through the internet. By using Interface Endpoints, you can save on data transfer costs associated with traffic.
Utilizing Interface Endpoints or Gateway Endpoints can indeed help save on traffic costs when accessing services like Amazon S3, Amazon SQS, and Amazon DynamoDB from your Amazon Virtual Private Cloud (VPC).
Key points:
Amazon S3: With an Interface Endpoint for S3, you can privately access S3 buckets without incurring data transfer costs between your VPC and S3.
Amazon SQS: Interface Endpoints for SQS enable secure interaction with SQS queues within your VPC, avoiding data transfer costs for communication with SQS.
Amazon DynamoDB: Using an Interface Endpoint for DynamoDB, you can access DynamoDB tables in your VPC without incurring data transfer costs.
Additionally, Interface Endpoints allow private access to AWS services using private IP addresses within your VPC, eliminating the need for internet gateway traffic. This helps eliminate data transfer costs for accessing services like S3, SQS, and DynamoDB from your VPC.
Optimize Image Sizes for Faster Loading
Potential Savings: Depends on the workload
Optimizing image sizes can help you save in various ways.
Reduce ECR Costs: By storing smaller instances, you can cut down expenses on Amazon Elastic Container Registry (ECR).
Minimize EBS Volumes on EKS Nodes: Keeping smaller volumes on Amazon Elastic Kubernetes Service (EKS) nodes helps in cost reduction.
Accelerate Container Launch Times: Faster container launch times ultimately lead to quicker task execution.
Optimization Methods:
Use the Right Image: Employ the most efficient image for your task; for instance, Alpine may be sufficient in certain scenarios.
Remove Unnecessary Data: Trim excess data and packages from the image.
Multi-Stage Image Builds: Utilize multi-stage image builds by employing multiple FROM instructions.
Use .dockerignore: Prevent the addition of unnecessary files by employing a .dockerignore file.
Reduce Instruction Count: Minimize the number of instructions, as each instruction adds extra weight to the hash. Group instructions using the && operator.
Layer Consolidation: Move frequently changing layers to the end of the Dockerfile.
These optimization methods can contribute to faster image loading, reduced storage costs, and improved overall performance in containerized environments.
Use Load Balancers to Save on IP Address Costs
Potential Savings: depends on the workload
Starting from February 2024, Amazon begins billing for each public IPv4 address. Employing a load balancer can help save on IP address costs by using a shared IP address, multiplexing traffic between ports, load balancing algorithms, and handling SSL/TLS.
By consolidating multiple services and instances under a single IP address, you can achieve cost savings while effectively managing incoming traffic.
Optimize Database Services for Higher Performance (MySQL, PostgreSQL, etc.)
Potential Savings: depends on the workload
AWS provides default settings for databases that are suitable for average workloads. If a significant portion of your monthly bill is related to AWS RDS, it's worth paying attention to parameter settings related to databases.
Some of the most effective settings may include:
Use Database-Optimized Instances: For example, instances in the R5 or X1 class are optimized for working with databases.
Choose Storage Type: General Purpose SSD (gp2) is typically cheaper than Provisioned IOPS SSD (io1/io2).
AWS RDS Auto Scaling: Automatically increase or decrease storage size based on demand.
If you can optimize the database workload, it may allow you to use smaller instance sizes without compromising performance.
Regularly Update Instances for Better Performance and Lower Costs
Potential Savings: Minor
As Amazon deploys new servers in their data processing centers to provide resources for running more instances for customers, these new servers come with the latest equipment, typically better than previous generations. Usually, the latest two to three generations are available. Make sure you update regularly to effectively utilize these resources.
Take Memory Optimize instances, for example, and compare the price change based on the relevance of one instance over another. Regular updates can ensure that you are using resources efficiently.
InstanceGenerationDescriptionOn-Demand Price (USD/hour)m6g.large6thInstances based on ARM processors offer improved performance and energy efficiency.$0.077m5.large5thGeneral-purpose instances with a balanced combination of CPU and memory, designed to support high-speed network access.$0.096m4.large4thA good balance between CPU, memory, and network resources.$0.1m3.large3rdOne of the previous generations, less efficient than m5 and m4.Not avilable
Use RDS Proxy to reduce the load on RDS
Potential for savings: Low
RDS Proxy is used to relieve the load on servers and RDS databases by reusing existing connections instead of creating new ones. Additionally, RDS Proxy improves failover during the switch of a standby read replica node to the master.
Imagine you have a web application that uses Amazon RDS to manage the database. This application experiences variable traffic intensity, and during peak periods, such as advertising campaigns or special events, it undergoes high database load due to a large number of simultaneous requests.
During peak loads, the RDS database may encounter performance and availability issues due to the high number of concurrent connections and queries. This can lead to delays in responses or even service unavailability.
RDS Proxy manages connection pools to the database, significantly reducing the number of direct connections to the database itself.
By efficiently managing connections, RDS Proxy provides higher availability and stability, especially during peak periods.
Using RDS Proxy reduces the load on RDS, and consequently, the costs are reduced too.
Define the storage policy in CloudWatch
Potential for savings: depends on the workload, could be significant.
The storage policy in Amazon CloudWatch determines how long data should be retained in CloudWatch Logs before it is automatically deleted.
Setting the right storage policy is crucial for efficient data management and cost optimization. While the "Never" option is available, it is generally not recommended for most use cases due to potential costs and data management issues.
Typically, best practice involves defining a specific retention period based on your organization's requirements, compliance policies, and needs.
Avoid using an undefined data retention period unless there is a specific reason. By doing this, you are already saving on costs.
Configure AWS Config to monitor only the events you need
Potential for savings: depends on the workload
AWS Config allows you to track and record changes to AWS resources, helping you maintain compliance, security, and governance. AWS Config provides compliance reports based on rules you define. You can access these reports on the AWS Config dashboard to see the status of tracked resources.
You can set up Amazon SNS notifications to receive alerts when AWS Config detects non-compliance with your defined rules. This can help you take immediate action to address the issue. By configuring AWS Config with specific rules and resources you need to monitor, you can efficiently manage your AWS environment, maintain compliance requirements, and avoid paying for rules you don't need.
Use lifecycle policies for S3 and ECR
Potential for savings: depends on the workload
S3 allows you to configure automatic deletion of individual objects or groups of objects based on specified conditions and schedules. You can set up lifecycle policies for objects in each specific bucket. By creating data migration policies using S3 Lifecycle, you can define the lifecycle of your object and reduce storage costs.
These object migration policies can be identified by storage periods. You can specify a policy for the entire S3 bucket or for specific prefixes. The cost of data migration during the lifecycle is determined by the cost of transfers. By configuring a lifecycle policy for ECR, you can avoid unnecessary expenses on storing Docker images that you no longer need.
Switch to using GP3 storage type for EBS
Potential for savings: 20%
By default, AWS creates gp2 EBS volumes, but it's almost always preferable to choose gp3 — the latest generation of EBS volumes, which provides more IOPS by default and is cheaper.
For example, in the US-east-1 region, the price for a gp2 volume is $0.10 per gigabyte-month of provisioned storage, while for gp3, it's $0.08/GB per month. If you have 5 TB of EBS volume on your account, you can save $100 per month by simply switching from gp2 to gp3.
Switch the format of public IP addresses from IPv4 to IPv6
Potential for savings: depending on the workload
Starting from February 1, 2024, AWS will begin charging for each public IPv4 address at a rate of $0.005 per IP address per hour. For example, taking 100 public IP addresses on EC2 x $0.005 per public IP address per month x 730 hours = $365.00 per month.
While this figure might not seem huge (without tying it to the company's capabilities), it can add up to significant network costs. Thus, the optimal time to transition to IPv6 was a couple of years ago or now.
Here are some resources about this recent update that will guide you on how to use IPv6 with widely-used services — AWS Public IPv4 Address Charge.
Collaborate with AWS professionals and partners for expertise and discounts
Potential for savings: ~5% of the contract amount through discounts.
AWS Partner Network (APN) Discounts: Companies that are members of the AWS Partner Network (APN) can access special discounts, which they can pass on to their clients. Partners reaching a certain level in the APN program often have access to better pricing offers.
Custom Pricing Agreements: Some AWS partners may have the opportunity to negotiate special pricing agreements with AWS, enabling them to offer unique discounts to their clients. This can be particularly relevant for companies involved in consulting or system integration.
Reseller Discounts: As resellers of AWS services, partners can purchase services at wholesale prices and sell them to clients with a markup, still offering a discount from standard AWS prices. They may also provide bundled offerings that include AWS services and their own additional services.
Credit Programs: AWS frequently offers credit programs or vouchers that partners can pass on to their clients. These could be promo codes or discounts for a specific period.
Seek assistance from AWS professionals and partners. Often, this is more cost-effective than purchasing and configuring everything independently. Given the intricacies of cloud space optimization, expertise in this matter can save you tens or hundreds of thousands of dollars.
More valuable tips for optimizing costs and improving efficiency in AWS environments:
Scheduled TurnOff/TurnOn for NonProd environments: If the Development team is in the same timezone, significant savings can be achieved by, for example, scaling the AutoScaling group of instances/clusters/RDS to zero during the night and weekends when services are not actively used.
Move static content to an S3 Bucket & CloudFront: To prevent service charges for static content, consider utilizing Amazon S3 for storing static files and CloudFront for content delivery.
Use API Gateway/Lambda/Lambda Edge where possible: In such setups, you only pay for the actual usage of the service. This is especially noticeable in NonProd environments where resources are often underutilized.
If your CI/CD agents are on EC2, migrate to CodeBuild: AWS CodeBuild can be a more cost-effective and scalable solution for your continuous integration and delivery needs.
CloudWatch covers the needs of 99% of projects for Monitoring and Logging: Avoid using third-party solutions if AWS CloudWatch meets your requirements. It provides comprehensive monitoring and logging capabilities for most projects.
Feel free to reach out to me or other specialists for an audit, a comprehensive optimization package, or just advice.