Compliance Monitoring is the ongoing process of verifying that an organization's systems, processes, and people continuously adhere to regulatory requirements, internal policies, and industry standards — not just at audit time, but every day. For cloud-native and regulated businesses in 2026, it is the difference between a clean audit and a costly breach.
What is Compliance Monitoring?
Compliance monitoring is the systematic, continuous practice of evaluating whether an organization's operations, systems, and people conform to the laws, regulations, and internal standards that govern them. Unlike a one-time audit, compliance monitoring runs as an always-on feedback loop — collecting evidence, flagging exceptions, and enabling rapid remediation before regulators ever knock on the door.
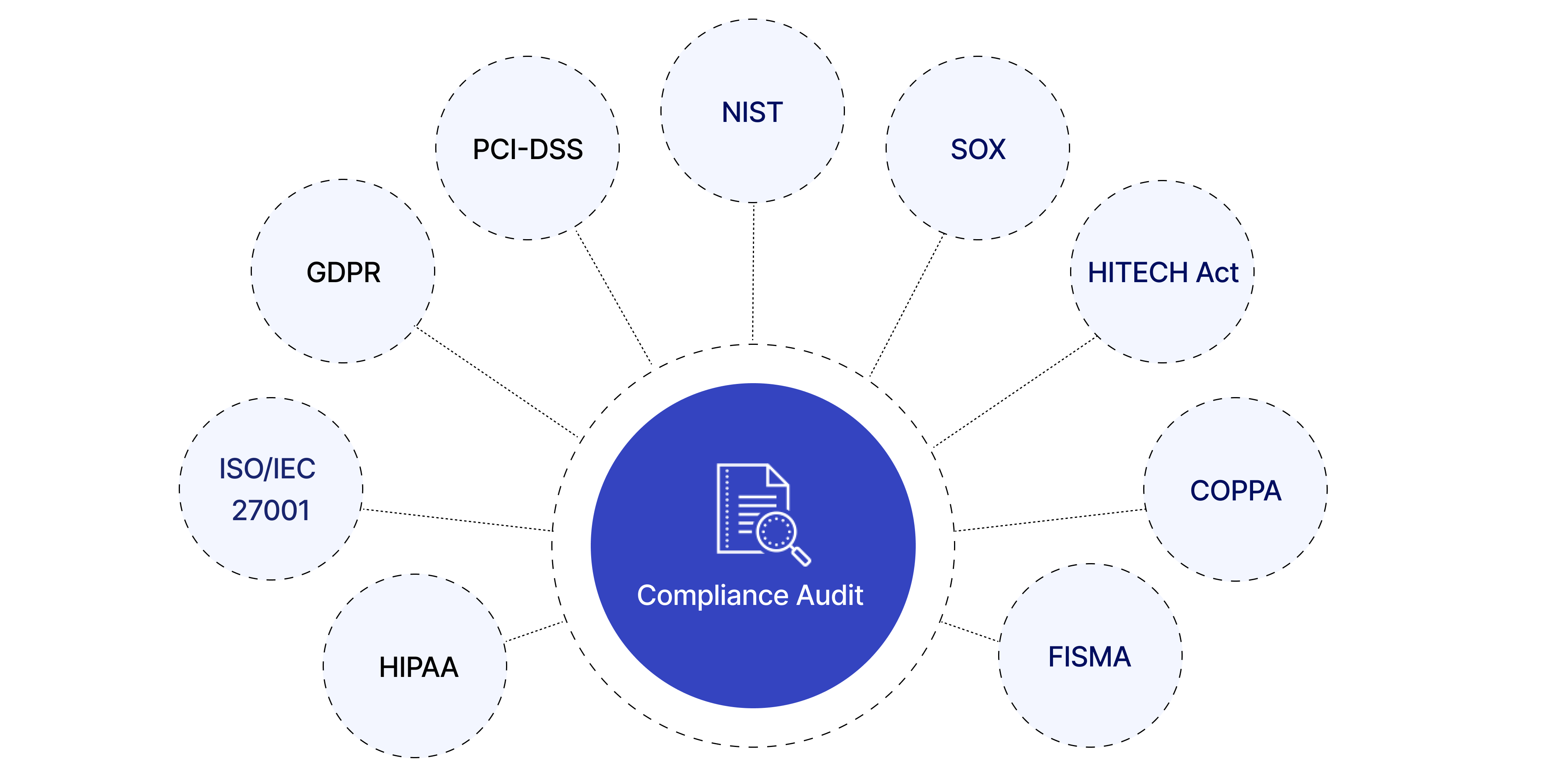
The practice is critical across heavily regulated industries:
Healthcare — HIPAA, HITECH, 21 CFR Part 11
Finance & Banking — PCI DSS, SOX, Basel III, MiFID II
Cloud & SaaS — SOC 2, ISO 27001, CSA CCM
EU-regulated entities — GDPR, NIS2, DORA
Energy & Utilities — NERC CIP, ISO 50001
Pharmaceuticals — GxP, FDA 21 CFR
💡 In short: Compliance monitoring is your organization's immune system. Audits are the annual check-up. Monitoring is what keeps you healthy between check-ups.
Why Compliance Monitoring Matters in 2026
Regulatory landscapes have never moved faster. GDPR fines reached record highs in 2024–2025, NIS2 entered enforcement mode across the EU, and DORA (Digital Operational Resilience Act) took effect for financial entities. Meanwhile, cloud adoption has created entirely new attack surfaces that traditional point-in-time audits simply cannot cover.
Risk Without MonitoringTypical Business ImpactProbability (unmonitored)Undetected misconfigured S3 bucket / cloud storageData breach, regulatory fine, brand damageHighStale privileged access not reviewedInsider threat, audit failure, SOX violationVery HighMissing audit log retentionInability to prove compliance, automatic audit failureHighBackup not testedUnrecoverable data loss, SLA breach, recovery failureMediumUnpatched critical CVE beyond SLAExploitable vulnerability, CVSS breach, PCI non-complianceHighWhy Compliance Monitoring Matters in 2026
Strong compliance monitoring builds trust with enterprise clients and partners, significantly reduces audit preparation time, and enables a proactive risk posture instead of a reactive, fire-fighting one.
Compliance Monitoring vs Compliance Audit vs Compliance Management
These three terms are often used interchangeably but they describe distinct activities that work together. Understanding the difference helps organizations allocate resources correctly.
DimensionCompliance MonitoringCompliance AuditCompliance ManagementFrequencyContinuous / near-real-timePeriodic (annual, quarterly)Ongoing governancePurposeDetect & alert on deviationsFormal independent assessmentPolicies, training, cultureOutputAlerts, dashboards, exception logsAudit report, findings, attestationPolicies, procedures, risk registerWho leadsEngineering / Security / DevOpsInternal audit / Third-party auditorCompliance Officer / GRC teamAnalogyBlood pressure cuff worn dailyAnnual physical with doctorHealthy lifestyle programCompliance Monitoring vs Compliance Audit vs Compliance Management
✅ Monitoring answers
Is MFA enforced right now?
Are all logs being retained?
Did anything change in IAM this week?
Are backups completing successfully?
Is encryption enabled on all storage?
📋 Auditing answers
Were controls effective over the period?
Did evidence satisfy the framework?
What is the organization's control maturity?
What formal findings require remediation?
Is the organization SOC 2 / ISO 27001 ready?
Explore our Compliance Audit services
The 7-Step Compliance Monitoring Process
Effective compliance monitoring is not a single tool or dashboard — it's a disciplined cycle. Here is the process Gart uses when setting up or maturing a client's compliance monitoring program:
1. Define Scope & Applicable Frameworks
Identify which regulations, standards, and internal policies apply. Map your systems, data flows, and third-party integrations to determine the monitoring perimeter. Ambiguous scope is the most common reason monitoring programs fail.
2. Inventory Systems & Controls
Catalogue all assets (cloud, on-prem, SaaS, CI/CD pipelines) and map each one to a control objective. Assign control owners. Without ownership, no one acts when an exception fires.
3. Define Evidence Collection Rules
For each control, specify what constitutes "evidence of compliance" — a log entry, a configuration state, a test result, a screenshot, or a signed document. Define collection frequency (real-time, daily, monthly) and acceptable format for auditors.
4. Instrument & Automate Collection
Deploy monitoring agents, SIEM rules, cloud policy engines (AWS Config, Azure Policy, GCP Security Command Center), and IaC scanning tools. Automate evidence collection wherever possible — manual evidence gathering at audit time is a costly, error-prone anti-pattern.
5. Monitor Exceptions & Triage Alerts
Create alert thresholds for control deviations. Not every alert is a breach — build a triage process that separates noise from genuine risk. Route high-priority exceptions to security/engineering immediately; lower-priority items to a weekly review queue.
6. Prioritize Risks & Remediate
Score exceptions by likelihood and impact. Maintain a risk register that tracks open findings, owners, and target remediation dates. Escalate unresolved critical findings to leadership with a clear business-impact framing.
7. Re-test, Report & Continuously Improve
After remediation, re-test the control to confirm it is effective. Produce compliance health reports for leadership and auditors. Run a quarterly retrospective to tune alert thresholds and update monitoring scope as regulations and infrastructure evolve.
Key Controls & Evidence to Monitor
Across hundreds of compliance engagements, the controls below consistently appear on auditor checklists. These are the areas where automated compliance monitoring delivers the highest return:
Control AreaWhat to MonitorEvidence Auditors WantRelevant FrameworksIdentity & Access (IAM)Privileged role assignments, inactive accounts, MFA status, service account permissionsAccess review logs, MFA adoption rate, least-privilege config exportsSOC 2, ISO 27001, HIPAAAudit LoggingLog completeness, retention period, tamper-evidence, SIEM ingestion healthLog retention policy, SIEM dashboard, CloudTrail / Audit Log exportsPCI DSS, SOX, NIS2, GDPREncryptionData-at-rest encryption on storage, TLS version on endpoints, key rotation schedulesEncryption config exports, key management audit logs, TLS scan reportsPCI DSS, HIPAA, GDPR, ISO 27001Patch ManagementCVE scan results, SLA adherence per severity, open critical/high vulnerabilitiesScan reports, patch cadence logs, SLA compliance metricsSOC 2, PCI DSS, ISO 27001Backup & RecoveryBackup job success rate, RPO/RTO test results, offsite replication statusBackup logs, recovery test records, DR test reportsSOC 2, ISO 22301, DORA, NIS2Vendor / Third-Party AccessActive vendor sessions, access scope, contract/NDA currency, SOC 2 report datesVendor access logs, contract register, third-party risk assessmentsISO 27001, SOC 2, GDPR, NIS2Network & PerimeterFirewall rule changes, open ports, egress filtering, WAF alert volumesFirewall config snapshots, IDS/IPS logs, pen test reportsPCI DSS, SOC 2, NIS2Incident ResponseMean time to detect (MTTD), mean time to respond (MTTR), breach notification timelinesIncident logs, CSIRT reports, post-mortemsGDPR (72h), NIS2, HIPAA, DORAKey Controls & Evidence to Monitor
Continuous Compliance Monitoring for Cloud Environments
Cloud infrastructure changes constantly — teams spin up resources, update IAM policies, and deploy code multiple times per day. This makes continuous compliance monitoring not a nice-to-have but a fundamental requirement. Manual checks against cloud state are obsolete before the ink dries.
AWS Compliance Monitoring — Key Automated Checks
AWS Config Rules — detect non-compliant resources in real time (e.g., unencrypted EBS volumes, public S3 buckets, missing CloudTrail)
AWS Security Hub — aggregates findings from GuardDuty, Inspector, Macie into a single compliance posture score
CloudTrail + Athena — query audit logs for unauthorized IAM changes, API calls outside approved regions
IAM Access Analyzer — surfaces external access to resources and unused roles/permissions
Azure Compliance Monitoring — Key Automated Checks
Azure Policy & Defender for Cloud — enforce and score compliance against CIS, NIST SP 800-53, ISO 27001 benchmarks
Microsoft Purview — data classification, governance, and audit trail across Azure and M365
Azure Monitor + Sentinel — SIEM-class alerting on suspicious activity with compliance-relevant playbooks
Privileged Identity Management (PIM) — just-in-time access with mandatory justification and approval workflows
GCP Compliance Monitoring — Key Automated Checks
Security Command Center — organization-wide misconfiguration detection and compliance benchmarking
VPC Service Controls — perimeter security policies that prevent data exfiltration
Cloud Audit Logs — immutable, per-service activity and data access logs
Policy Intelligence — recommends IAM role right-sizing based on actual usage data
🔗
For authoritative cloud security benchmarks, the CIS Benchmarks provide configuration baselines for AWS, Azure, GCP, Kubernetes, and 100+ other platforms — an industry-standard starting point for any cloud compliance monitoring program.
See Gart's Cloud Computing & Security services
Industry-Specific Compliance Monitoring Frameworks
Compliance monitoring requirements differ significantly by industry and geography. Below are the frameworks Gart's clients most commonly monitor against, along with the controls that require continuous (not just periodic) monitoring.
FrameworkIndustry / RegionKey Continuous Monitoring RequirementsResourcesISO 27001Global / All industriesAccess control review, log management, vulnerability scanning, supplier reviewISO.orgSOC 2 Type IISaaS / TechnologyContinuous availability, logical access, change management, incident responseAICPAHIPAAHealthcare (US)ePHI access logs, encryption at rest/transit, workforce activity auditsHHS.govPCI DSS v4.0Payment / E-commerceReal-time network monitoring, file integrity monitoring, quarterly vulnerability scansPCI SSCNIS2EU / Critical sectorsIncident detection within 24h, risk assessments, supply chain security checksENISAGDPREU / Global processing EU dataData subject request tracking, breach detection (<72h notification), processor auditsGDPR.euIndustry-Specific Compliance Monitoring Frameworks
How to prepare for a HIPAA Audit - Gart's PCI DSS Audit guide
First-Hand Experience
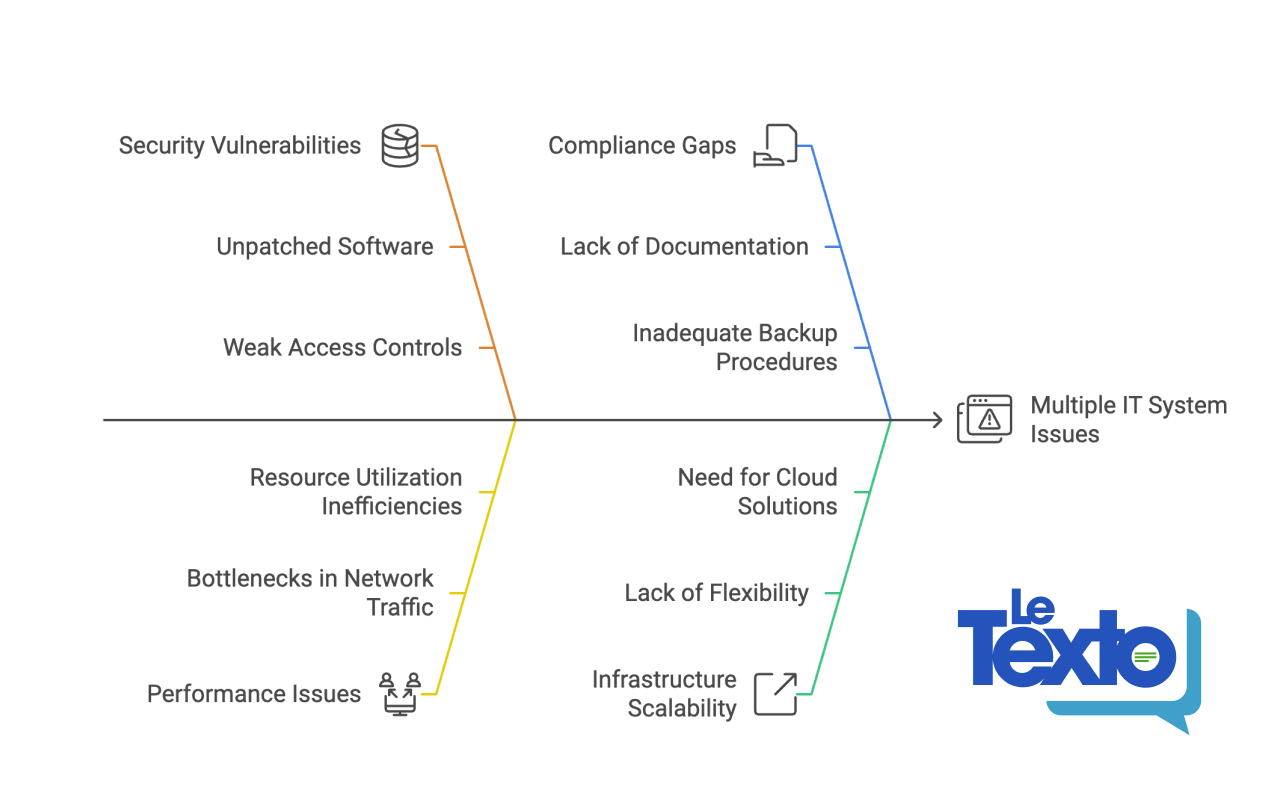
What We Usually Find During Compliance Monitoring Reviews
After reviewing postures across dozens of regulated environments, these are the patterns we encounter repeatedly — regardless of organization size.
👥
Incomplete or stale access reviews
Former employees and service accounts with active permissions weeks after departure. IAM hygiene is rarely automated, and reviews are often rubber-stamped.
📋
Missing backup test evidence
Backups appear healthy, but nobody has tested a restore in 6–18 months. Auditors want dated restore test logs with RPO/RTO outcomes, not just success metrics.
📊
Fragmented or incomplete audit logs
Gaps in the log chain (like disabled S3 data-event logging) make it impossible to reconstruct an incident or prove that one didn't happen.
🔔
Alert fatigue masking real issues
Thousands of low-fidelity alerts lead teams to mute notifications or build exceptions, inadvertently disabling detection for real threats.
📄
Policy-to-implementation gaps
Written policies say "encryption required," but reality reveals unencrypted legacy buckets. Continuous monitoring is the only way to detect this drift.
🔧
Automation is first patched, last monitored
CI/CD pipelines move faster than human reviewers. IaC repositories often lack policy-as-code scanning, leaving non-compliant resources active for months.
Featured Success Story
Case study: ISO 27001 compliance for Spiral Technology
→
Compliance Monitoring Tools & Automation
The right tooling depends on your stack, frameworks, and team maturity. Most organizations use a layered approach rather than a single platform:
CategoryRepresentative ToolsBest ForCloud Security Posture Management (CSPM)AWS Security Hub, Wiz, Prisma Cloud, Orca Security, Defender for CloudCloud misconfiguration detection, continuous benchmarkingSIEM / Log ManagementSplunk, Elastic SIEM, Microsoft Sentinel, Datadog SecurityLog correlation, anomaly detection, audit evidenceGRC PlatformsVanta, Drata, Secureframe, ServiceNow GRC, OneTrustEvidence collection automation, audit-ready reportingPolicy-as-Code / IaC ScanningOpen Policy Agent (OPA), Checkov, Terrascan, tfsec, ConftestPrevent non-compliant infrastructure from being deployedVulnerability ManagementTenable Nessus, Qualys, AWS Inspector, Trivy (containers)CVE detection, patch SLA monitoring, container scanningIdentity GovernanceSailPoint, CyberArk, Azure PIM, AWS IAM Access AnalyzerAccess reviews, least-privilege enforcement, PAM
⚠️ Tool sprawl is a compliance risk: More tools mean more integrations to maintain, more alert queues to manage, and more places where evidence can fall through the cracks. Start with native cloud tools and expand deliberately. The Linux Foundation and CNCF maintain open-source compliance tooling for cloud-native environments worth evaluating before adding commercial licenses.
Compliance Monitoring Best Practices
1. Shift compliance left into the development pipeline
The cheapest time to catch a compliance violation is before the resource is deployed. Integrate policy-as-code scanning (OPA, Checkov) into your CI/CD pipeline so that non-compliant Terraform or Helm charts never reach production. Treat compliance failures as build-breaking errors, not post-deploy recommendations.
2. Automate evidence collection — not just detection
Detection without evidence collection is useless at audit time. Configure your monitoring tools to export and archive compliance evidence (configuration snapshots, access review logs, scan reports) automatically to an immutable store. Auditors need evidence from a defined period — not a screenshot taken the morning of the audit.
3. Assign control owners, not just tool owners
Every control needs a named human owner who is accountable for exceptions. When an alert fires that MFA is disabled on a privileged account, "the security team" is not a sufficient owner — a specific person must be on call to investigate and remediate within the SLA.
4. Tune alerts ruthlessly to eliminate fatigue
Compliance monitoring programs that generate thousands of daily alerts quickly become ignored. Start with a small set of high-fidelity, high-impact alerts. Expand incrementally after each is tuned to near-zero false positive rates. A team that responds to 20 real alerts per day is more secure than one drowning in 2,000 noisy ones.
5. Monitor your monitoring
Monitoring pipelines break silently. Log shippers stop, API rate limits are hit, SIEM ingestion queues fill up. Build meta-monitoring to detect when evidence collection or alerting pipelines have gaps — and treat those gaps as compliance findings in their own right.
6. Conduct a quarterly compliance posture review
Beyond continuous automated monitoring, schedule a quarterly human review of the compliance posture. Review open exceptions, re-assess risk scores, retire obsolete controls, and update monitoring scope to cover new systems and regulatory changes.
Compliance Monitoring Checklist for Cloud Teams
A starting point for cloud-first compliance. Each item requires a named owner, a monitoring cadence, and a defined evidence artifact.
✓
MFA enforced on all privileged and administrative accounts
✓
Access reviews completed for all privileged roles (minimum quarterly)
✓
Service accounts audited for least-privilege and no unused permissions
✓
Audit logging enabled and retained (90 days min; 1 year for PCI/HIPAA)
✓
SIEM ingestion health monitored — no silent log gaps
✓
Data-at-rest encryption confirmed on all storage (S3, RDS, EBS, blobs)
✓
TLS 1.2+ enforced; TLS 1.0/1.1 disabled on all endpoints
✓
Encryption key rotation scheduled and verified
✓
Vulnerability scans run weekly; critical/high CVEs remediated within SLA
✓
Patch management SLA compliance tracked and reported
✓
Backups verified complete daily; restore tests documented quarterly
✓
DR test completed at least annually; RPO/RTO outcomes logged
✓
No public cloud storage buckets without explicit business justification
✓
Firewall change log reviewed; unauthorized rule changes alerting
✓
Vendor/third-party access scoped, time-limited, and reviewed quarterly
✓
Incident response plan tested; MTTD and MTTR tracked
✓
Policy-as-code scans integrated into CI/CD pipelines
✓
Compliance evidence archived in immutable storage for audit period
✓
Monitoring pipeline health checked — no silent collection failures
✓
Quarterly posture review conducted with named control owners
Gart Solutions · Compliance Monitoring Services
How Gart Helps You Build a Continuous Compliance Monitoring Program
We work with CTOs, CISOs, and engineering leaders to design, implement, and run compliance monitoring programs that hold up under real auditor scrutiny — not just on paper.
🗺️
Scope & Framework Mapping
We identify applicable frameworks (ISO 27001, SOC 2, HIPAA, PCI DSS, NIS2, GDPR) and map your cloud infrastructure to each control objective.
🔧
Monitoring Setup & Automation
We deploy CSPM tools, SIEM rules, and policy-as-code pipelines — so evidence is collected automatically, not manually on audit day.
📊
Gap Analysis & Risk Register
We deliver a clear view of your current compliance posture, prioritized by risk, with a remediation roadmap and accountable owners.
🔄
Ongoing Reviews & Readiness
Monthly exception reviews and pre-audit evidence packages — so you're never scrambling the week before an official audit.
☁️
Cloud-Native Expertise
AWS, Azure, GCP, Kubernetes, and CI/CD. We speak infrastructure as code and translate compliance into DevOps workflows.
📋
Audit-Ready Deliverables
Exception logs, risk matrices, and control evidence archives. Everything formatted for the specific framework you're being audited against.
Get a Compliance Audit
Talk to an Expert
Fedir Kompaniiets
Co-founder & CEO, Gart Solutions · Cloud Architect & DevOps Consultant
Fedir is a technology enthusiast with over a decade of diverse industry experience. He co-founded Gart Solutions to address complex tech challenges related to Digital Transformation, helping businesses focus on what matters most — scaling. Fedir is committed to driving sustainable IT transformation, helping SMBs innovate, plan future growth, and navigate the "tech madness" through expert DevOps and Cloud managed services. Connect on LinkedIn.

Healthcare technology solutions must navigate a complex web of regulations designed to protect patient data and maintain confidentiality, integrity, and availability.
Six significant compliance frameworks that healthcare providers and technology developers must adhere to are HIPAA, CCPA, GDPR, NIST, HiTECH, and PIPEDA.
Let’s take a closer look at each of those frameworks:
HIPAA Compliance
The Health Insurance Portability and Accountability Act (HIPAA) is a critical regulation for any technological solutions developed for the US market. Enacted in 1996, HIPAA mandates the protection of Protected Healthcare Information (PHI). It ensures that electronically protected health information maintains its confidentiality, integrity, and availability. Compliance with HIPAA involves implementing robust security measures to prevent unauthorized access, breaches, and misuse of patient data. This includes encryption, access controls, and regular audits to ensure that all processes align with HIPAA standards.
CCPA Compliance
The California Consumer Privacy Act (CCPA) is another cornerstone of data protection in the United States. Although it primarily targets businesses operating in California, its implications are far-reaching, especially for healthcare providers handling large volumes of personal data. The CCPA focuses on transparency, requiring organizations to inform clients about the data collected, its purpose, and how it will be used. Patients have the right to request a detailed report of their data, demand its deletion, or opt out of data sharing with third parties. Ensuring CCPA compliance necessitates rigorous data management practices and responsive mechanisms to address patient requests promptly.
GDPR Compliance
The General Data Protection Regulation (GDPR) represents one of the most stringent data protection laws globally. Introduced in Europe in 2018, GDPR applies to any healthcare apps and services operating within the European Union. Its reach extends to any company processing data related to EU citizens, regardless of the company's location. GDPR emphasizes patient consent, data minimization, and the right to be forgotten. Healthcare providers must ensure that data is collected and processed transparently, securely, and only for specified purposes. Non-compliance can result in severe financial penalties, making adherence to GDPR a top priority for any organization handling personal health data in Europe.
NIST Compliance
The National Institute of Standards and Technology (NIST) framework is another collection of standards, tools, and technologies designed to protect users’ data in the United States. According to research, 70% of surveyed organizations consider the NIST framework as the best cybersecurity practice, but many say it requires significant investment. The NIST framework is renowned for its comprehensive approach to cybersecurity, offering guidelines for identifying, protecting, detecting, responding to, and recovering from cyber incidents. Implementing NIST standards helps healthcare organizations bolster their security posture, ensuring they can safeguard sensitive health information effectively.
HiTech Compliance
The Health Information Technology for Economic and Clinical Health (HiTECH) Act focuses more on the Electronic Health Record (EHR) systems' data security and is also valid in the United States. Enacted in 2009 and integrated into the HIPAA Final Omnibus Rule in 2013, HiTECH aims to promote the adoption and meaningful use of health information technology. Now, HIPAA-compliant applications are considered HiTECH compliant. This alignment simplifies compliance efforts for healthcare providers, ensuring they meet rigorous standards for data protection and patient privacy across multiple regulatory frameworks.
PIPEDA Compliance
The Personal Information Protection and Electronic Documents Act (PIPEDA) governs cloud storage and other medical software working in the Canadian market. Compliance with PIPEDA is crucial for any healthcare technology solutions operating in Canada. An interesting fact is that if your app is compliant with PIPEDA, it’s most likely compliant with the GDPR since these two laws are quite similar. PIPEDA emphasizes obtaining consent for data collection, ensuring data accuracy, and implementing safeguards to protect personal information. Compliance with PIPEDA helps organizations build trust with Canadian patients and ensures robust data protection practices.
Project Example: Gart's Expertise in ISO 27001 Compliance
Challenges:
Our client, Spiral Technology, faced significant challenges related to data security and cloud migration. The primary concerns were ensuring compliance with ISO 27001 standards and seamlessly transitioning their data and operations to the cloud without compromising security or disrupting their services.
Proposed Solutions:
ISO 27001 Compliance
Gart Solutions provided expert guidance and support to Spiral Technology, helping them achieve ISO 27001 certification. This involved implementing comprehensive security measures, conducting thorough risk assessments, and establishing robust data protection protocols.
Seamless Cloud Migration
To address the challenge of cloud migration, Gart Solutions developed a detailed migration plan that minimized downtime and ensured data integrity, utilizing advanced encryption and secure data transfer methods to protect sensitive information during the transition.
Continuous Monitoring and Audits
For post-migration, Gart Solutions set up continuous monitoring and regular audits to maintain ISO 27001 compliance and address any emerging security threats promptly.
More details about this Case Study – by the link.
Interested in being prepared for a compliance audit & certification - contact Us!
We will help you to understand the specifics and be prepared, as well as from a technology integration and data management perspective.
Conclusion
Compliance in healthcare is an ongoing challenge that requires constant vigilance, investment in technology, and a thorough understanding of regulatory requirements.
By adhering to HIPAA, CCPA, GDPR, NIST, HiTECH, and PIPEDA, healthcare providers can protect patient data, build trust, and avoid costly penalties. As the regulatory landscape continues to evolve, staying informed and proactive in compliance efforts will remain essential for success in the healthcare industry.
The NIS2 (Network and Information Security Directive) is a comprehensive directive that mandates organizations to implement robust security measures and document compliance to protect critical assets and ensure community continuity.
For organizations subject to NIS2 requirements, CISOs, and IT security officers must ensure robust internal compliance preparedness.
Why NIS2 Compliance Matters
NIS2 aims to enhance the overall level of cybersecurity in the EU by:
Improving the resilience of critical infrastructure.
Enhancing the security of network and information systems.
Ensuring rapid response to and recovery from cyber incidents.
For organizations subject to NIS2 requirements, compliance is not just a legal obligation but a vital component of risk management and operational continuity. Failing to comply can result in significant financial penalties, reputational damage, and operational disruptions.
Who is affected by NIS2?
NIS2 affects all big organizations that work in the European Union and are considered important to society. This includes organizations that:
Have 50 or more employees, or
Make over €10 million in revenue each year
NIS2 puts these organizations into two groups:
Essential organizations - These are very important sectors like energy, healthcare, transportation, and water supply.
Important organizations - These are sectors like manufacturing, food production, waste management, and postal services.
So in simple terms, if your fairly large organization operates in the EU and provides crucial services or products to society, then NIS2 applies to you. The directive aims to ensure these vital entities have strong cybersecurity measures in place.
The penalties for not following NIS2 rules are different depending on whether an organization is labeled as "essential" or "important".
For essential organizations:
They can be fined up to €10 million, or
They can be fined at least 2% of their total worldwide revenue from the previous year, whichever amount is higher.
For important organizations:
They can be fined up to €7 million, or
They can be fined at least 1.4% of their total worldwide revenue from the previous year, whichever amount is higher.
Gart’s NIS2 Solution
Gart offers a solution that simplifies the complexity of NIS2 compliance. The solution provides a systematic approach tailored to your ongoing operations and compliance efforts. By adopting Gart’s solution, you gain access to:
A systematic compliance framework for analyzing and documenting the security of critical assets.
Assurance of effective compliance work throughout your organization, aligned with good security practices and NIS2 requirements by applying ISO/EIC 27001/2 security principles.
Use of questionnaires to review the directive's requirements and ensure all documentation requirements are met, preparing you for audits.
Clear guidance on how to register significant security incidents with CSIRT, ensuring a proactive approach.
Read more: Gart’s Expertise in ISO 27001 Compliance Empowers Spiral Technology for Seamless Audits and Cloud Migration
How Does Gart Solution Support NIS2 Compliance?
NIS2 Requirement 1: Have policies for analyzing risks and information security
Gart can find and evaluate all assets, systems, weaknesses, and cyber/operational risks in critical infrastructure environments. It uses this detailed visibility to automatically create and enforce network security policies that reduce exposure to those identified risks.
In simple terms, Gart's solution allows organizations to:
Discover all their critical assets, systems, and potential vulnerabilities
Assess the cyber and operational risks in their environments
Automatically define security policies to protect against those risks
Enforce those security policies across their networks
NIS2 Requirement 2: Dealing with Security Incidents
Gart Solutions constantly keeps watch over all critical infrastructure systems for any signs of potential threats, both known and new. It analyzes all security alerts in detail to prioritize the most important issues. Gart also integrates with existing security tools like SIEM and SOAR to extend an organization's security processes across all of its critical systems.
In simpler terms, Gart's solution allows organizations to:
Continuously monitor all their vital systems and networks
Quickly detect any potential cyber threats, even new unidentified ones
Understand the context and importance of every security alert
Work seamlessly with their existing security tools and workflows
Expand their incident response capabilities to cover all critical infrastructure
NIS2 Requirement 3: Managing Crises
Gart provides:
A complete, up-to-date list of all critical systems
Logging of all changes and unusual activity in assets and networks
Ability to create and enforce security policies to separate networks and control access
Ready integration with backup and recovery tools
All of these capabilities from Gart help organizations improve their overall crisis management and ensure the continuity of essential operations.
In simpler terms, Gart's solution allows organizations to:
Know exactly what critical assets they have at all times
Track all activity so they can investigate incidents
Lock down systems by enforcing strict security controls
Quickly backup and restore systems if needed
NIS2 Requirement 4: Security of Networks and Information Systems
By utilizing Gart's capabilities, customers can effectively:
Identify vulnerabilities and insecure configurations in their critical networks and systems
Assess and manage the cyber risks to their operational environments
Allow remote access for personnel to do their work securely
In simple terms, Gart helps organizations implement robust security measures for their networks and information systems as required by NIS2. This includes finding and fixing vulnerabilities, evaluating risks, and controlling access - all crucial for securing vital operational technology.
NIS2 Requirement 5: Basic Cybersecurity Practices and Training
Gart's solution helps organizations:
Identify areas where they need to improve their basic cybersecurity habits and procedures based on risk assessments.
Ensure all personnel, whether employees or vendors, follow proper access controls, password management, and other essential cybersecurity practices.
Use the recommendations to develop training programs to raise cybersecurity awareness and skills.
NIS2 Requirement 6: Policies and Procedures for Data Encryption
Gart provides:
1) Encryption of all user data, critical system data, and other sensitive information in compliance with NIS2, GDPR, and other regulations.
2) Alerts when sensitive data like personal health records is being processed in a way that violates security policies or could lead to a data breach.
Here's a rewording in simple language:
NIS2 Requirement 7: Using Multi-Factor Authentication and Secure Communications
Gart helps organizations:
- Enforce strong access controls like multi-factor authentication across their workforce and supply chain vendors/partners
- Allow only authorized and verified personnel to access critical systems remotely or on-site
- Ensure all communications to operational technology are fully secured
- Meet audit requirements by recording all access sessions
Get a sample of IT Audit
Sign up now
Get on email
Loading...
Thank you!
You have successfully joined our subscriber list.
Key Features:
Mapping of Critical Assets
We will create an overview of the various types of critical assets within your value chain and document their security levels.
Risk Assessment of Critical Assets, Systems, and Processes
We will conduct a risk assessment based on the current threat landscape, the assets' placement within the value chain, and their potential societal consequences.
GAP Analysis
We will obtain a clear overview of your current compliance level and implementation, identifying the essential control objectives required for NIS2.
Automated Processes
We will automate control follow-ups and communication with internal stakeholders to ensure all relevant tasks are carried out correctly and on time.
Compliance Control and Scope of SoA
We will begin with an initial compliance review, prioritize, and scope the Statement of Applicability (SoA) based on NIS2 requirements.
Create Awareness and Communicate Directly with Stakeholders
We will create awareness and directly communicate with stakeholders to keep everyone informed about policy and procedural changes, ensuring everyone understands their role.
Overview of Reporting to CSIRT
We will establish a process for reporting significant incidents and threats to the organization or its supply chain to CSIRT, protecting critical assets quickly and efficiently.
Ongoing Auditing
We will document internal compliance with NIS2 via dedicated management controls and functionality for auditing critical suppliers.
About the NIS2 Directive or NIS2 framework
The NIS 2 Directive, also referred to as the NIS2 framework, is a European Union regulation aimed at enhancing cybersecurity across the bloc. Here's a breakdown of the key points:
Goals:
Improve overall cybersecurity posture in the EU.
Strengthen existing cybersecurity measures in critical sectors.
Ensure a consistent approach to cybersecurity risk management across member states.
Key Features:
Broader Scope: NIS2 applies to a wider range of sectors compared to the previous NIS Directive. This includes essential services (energy, transport, water, etc.) and important entities in sectors like waste management, postal services, manufacturing, and more.
Enhanced Risk Management: Organizations must implement robust cybersecurity measures to manage risks to their network and information systems. This includes measures to prevent incidents, minimize their impact, and report them effectively.
Incident Reporting: Entities are required to report significant incidents to relevant authorities. This allows for faster response and improved coordination across member states.
Supply Chain Security: The directive emphasizes the importance of supply chain security. Organizations need to consider the cybersecurity risks associated with their suppliers and vendors.
Cooperation and Information Sharing: Increased cooperation and information sharing among member states and relevant authorities are crucial aspects of NIS2.
Current Status:
Adopted in December 2022 and came into effect in January 2023.
EU member states have until October 17, 2024 to transpose the NIS2 Directive into national law.
By April 17, 2025, member states need to establish a list of essential entities falling under the directive.
NIS2-Compliance-Checklist-A-Comprehensive-Guide-to-Audit_Free-PDFDownload
Conclusion
The European Union's Network and Information Security Directive, known as NIS2, sets stringent requirements for organizations to safeguard their critical assets and ensure the continuity of essential services.
Gart is here to guide you through every step of the process, providing the expertise, tools, and support you need to achieve and maintain compliance. With our systematic approach, you can focus on your core business operations, confident that your information security is in capable hands.
Are you ready to simplify your NIS2 compliance journey? Contact Gart today to learn more about how we can help you strengthen your information security and achieve regulatory compliance with ease.