- Is Your Infrastructure Performant Enough to Meet Your Business Challenges?
- What Is an IT Infrastructure Audit?
- What an Audit Cover
- Audit Process — Step by Step
- Real Audit Examples and What You Get with Gart Solutions
- What you typically receive from a Gart Solutions audit
- Cost, and how to think about value
- Why organizations choose Gart Solutions
- Conclusion
Is Your Infrastructure Performant Enough to Meet Your Business Challenges?
As businesses scale, infrastructure stops being a background technical function and becomes a strategic growth engine. The real question is not whether your systems are running today. The question is whether your infrastructure is prepared for tomorrow.
Growing organizations frequently encounter scaling bottlenecks when their IT environments were never optimized for expansion. That shows up in the most frustrating ways: performance slows, cloud bills increase, security risks accumulate quietly, compliance requirements tighten, and leadership begins asking whether technology is enabling growth or limiting it. Those business challenges are familiar across industries, especially when uptime expectations and security obligations rise at the same time .
At Gart Solutions, we see this pattern repeatedly when conducting IT infrastructure audits. Systems often “work,” but beneath the surface there are architectural inefficiencies, over-provisioned resources, misconfigured IAM roles, incomplete logging setups, and disaster recovery plans that have never been tested. When a business grows fast, these issues stop being “technical debt” and start becoming real operational risk.
An infrastructure audit brings clarity. It answers questions executives actually care about:
- Can your architecture handle 2x or 5x growth?
- Are you aligned with ISO 27001, GDPR, HIPAA, SOC 2 expectations, or industry baselines?
- Are you overspending on cloud infrastructure due to waste and poor sizing?
- Are you one incident away from downtime because resilience is assumed, not proven?
A structured audit transforms infrastructure from reactive maintenance into proactive optimization. If your team needs a practical starting point, Gart Solutions’ IT Audit Services are designed to evaluate performance, security posture, compliance alignment, and cost efficiency — and then turn findings into a prioritized remediation roadmap.
What Is an IT Infrastructure Audit?
An IT Infrastructure Audit is a comprehensive, structured evaluation of your organization’s cloud and or on-premises environment designed to assess architecture health, scalability, security controls, compliance readiness, reliability, and cost efficiency. In practice, that means the audit looks at the systems you run, the way they connect, who can access what, how you detect problems, how you recover from failures, and whether you’re paying for resources you don’t need.
A professional audit examines compute resources, networking layers, storage systems, databases, monitoring tools, IAM configurations, encryption practices, and disaster recovery readiness . In cloud environments, it also checks whether your cloud service model and deployment approach fit business needs (IaaS, PaaS, SaaS; public, private, hybrid), and whether SLAs and contracts match expectations around uptime, availability, incident response, and audit rights .
At Gart Solutions, the audit methodology is structured around four pillars you can actually act on:
- Infrastructure Architecture Review
- Security and Compliance Assessment
- Performance and Reliability Analysis
- Cost Optimization and Resource Efficiency
The goal is not to produce a report that looks impressive. The goal is to make your infrastructure measurable, secure, scalable, and financially optimized, and then provide a clear path to get there.
Infrastructure vs Security vs Compliance Audits
People often use “IT audit” as a blanket term, but the intent matters.
An infrastructure audit focuses on whether your environment is built to perform reliably and scale efficiently, with sensible architecture and operational controls. A security audit focuses on vulnerabilities and defenses, including access control, encryption, logging, and exposure points . A compliance audit focuses on alignment with standards and regulations like ISO 27001, GDPR, HIPAA, PCI DSS, NIST, SOX, and others .
A good provider blends these lenses. That’s why a practical audit scope includes infrastructure review, performance assessment, security and compliance checks, cost assessment, and a roadmap for fixes .
Why Audits Matter in Cloud-First Businesses
Cloud makes it easy to ship fast. It also makes it easy to drift into chaos. Resources appear and never get cleaned up. IAM policies grow over time. Monitoring exists but alerts are noisy, so people ignore them. Backups happen, but restore is never tested. Then the business hits a high-traffic event, a compliance deadline, or a migration project and suddenly “good enough” breaks.
That’s why structured checklists matter. A cloud infrastructure checklist will typically require you to verify SLAs, validate IAM and MFA, confirm encryption for data at rest and in transit, ensure logging and monitoring are enabled, run vulnerability scanning and patch management, and test disaster recovery regularly . The audit turns those expectations into evidence: what you have, what you don’t, and what to fix first.
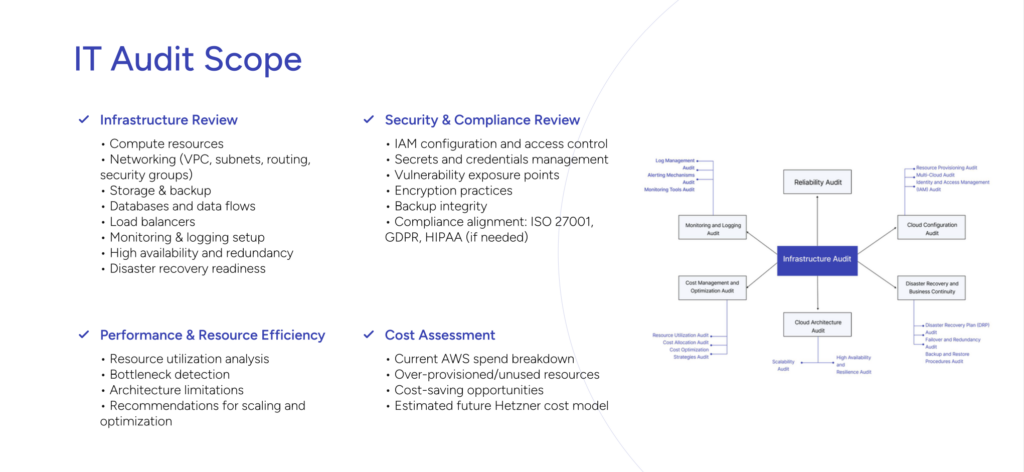
What an Audit Cover
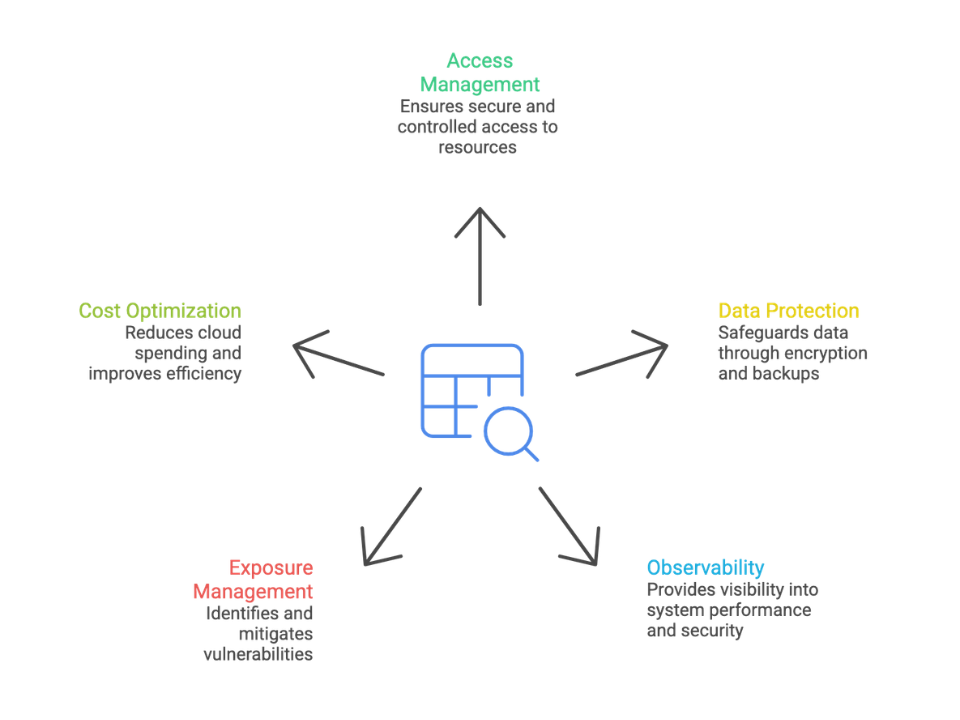
A high-quality IT Infrastructure Audit is broad enough to capture the real risks, but focused enough to produce a plan your team can execute. The most useful audits follow a practical scope: review the architecture, verify access control and data protection, validate observability and exposure management, and then tie everything to cost and business impact .
The scope below reflects what organizations most often need when they are scaling, tightening security, preparing for compliance, or planning migration.
Access, Identity, and Secrets Management
Identity is where most modern incidents begin. If access is too broad, too permanent, or poorly monitored, infrastructure risk rises fast.
A structured cloud audit checks IAM policies, access controls, and whether the principle of least privilege is enforced . It also confirms Multi-Factor Authentication (MFA) is enabled for accounts that can touch critical resources . Beyond that, it reviews user provisioning and deactivation processes and whether lifecycle management is automated, because “we’ll remove access later” is how access stays forever .
In migration or modernization projects, audits also look at secrets and credentials management, because hardcoded credentials, unmanaged tokens, and scattered secrets create hidden breach paths . The outcome you want is simple: fewer privileged accounts, clearer boundaries, stronger authentication, and traceable changes.
Data Protection: Encryption, Backups, and Recovery Readiness
Data protection is not a single control. It’s a chain. If any link is weak — encryption, key management, backups, retention, restore testing — the business is exposed.
A cloud infrastructure checklist typically requires confirmation that data at rest is encrypted with industry-standard algorithms and that key management practices are sound . It also requires data in transit encryption and secure transport protocols (HTTPS, SSH) for transfers between resources and between cloud and on-prem locations .
Then comes the question most teams avoid: can you actually restore? Audits verify backups are performed regularly, retention policies are defined, and disaster recovery plans exist and are tested . This isn’t theoretical. If your SLA requires uptime, DR is how you prove you can meet it, not just hope you will.
Observability: Logging, Monitoring, and Alerting
If you cannot see what’s happening, you cannot run infrastructure with confidence. Observability is what turns “we think it’s fine” into “we know it’s fine.”
Audits verify comprehensive logging for cloud resources and user activity is enabled, with secure retention and analysis practices . They assess continuous monitoring for suspicious behavior and resource anomalies, and whether monitoring integrates with your broader security operations, including SIEM workflows when applicable .
Alerting is its own discipline. The audit checks whether alerts are timely, meaningful, and routed to the right owners, with escalation procedures and response responsibilities clearly defined . A common “quiet failure” is that alerts exist, but they’re so noisy people mute them. A good audit treats alerting like a product: tune it, measure it, and make it actionable.
Exposure Management: Vulnerabilities, Patching, and Configuration Baselines
Modern infrastructure is built from moving parts. That’s why exposure management is about process, not one-off scanning.
A cloud checklist includes regular vulnerability scanning, patch management timelines, secure configuration baselines, and configuration management tools to keep settings consistent . It may also include periodic penetration testing and remediation plans for discovered issues .
Audits also look for practical “accidents waiting to happen”: open ports, permissive security groups, outdated images, untracked configuration changes, and brittle dependencies. If your business is aiming for compliance readiness, these checks become the evidence trail that helps you demonstrate control maturity.
Cost and Resource Optimization
Cloud waste is rarely malicious. It’s usually a byproduct of speed. Teams over-provision “just to be safe,” experiments never get cleaned up, and costs become hard to attribute across departments.
A structured audit checks resource inventory and visibility, tagging practices, right-sizing processes, and budgeting and monitoring for cloud spend . Migration-readiness audits also include cost modeling, identifying over-provisioned or unused resources and mapping cost-saving opportunities .
This is one reason audits often pay for themselves. When you find oversized workloads, idle instances, underused databases, or inefficient scaling policies, the savings can start immediately — and the business gets a cleaner architecture at the same time.
Audit Process — Step by Step
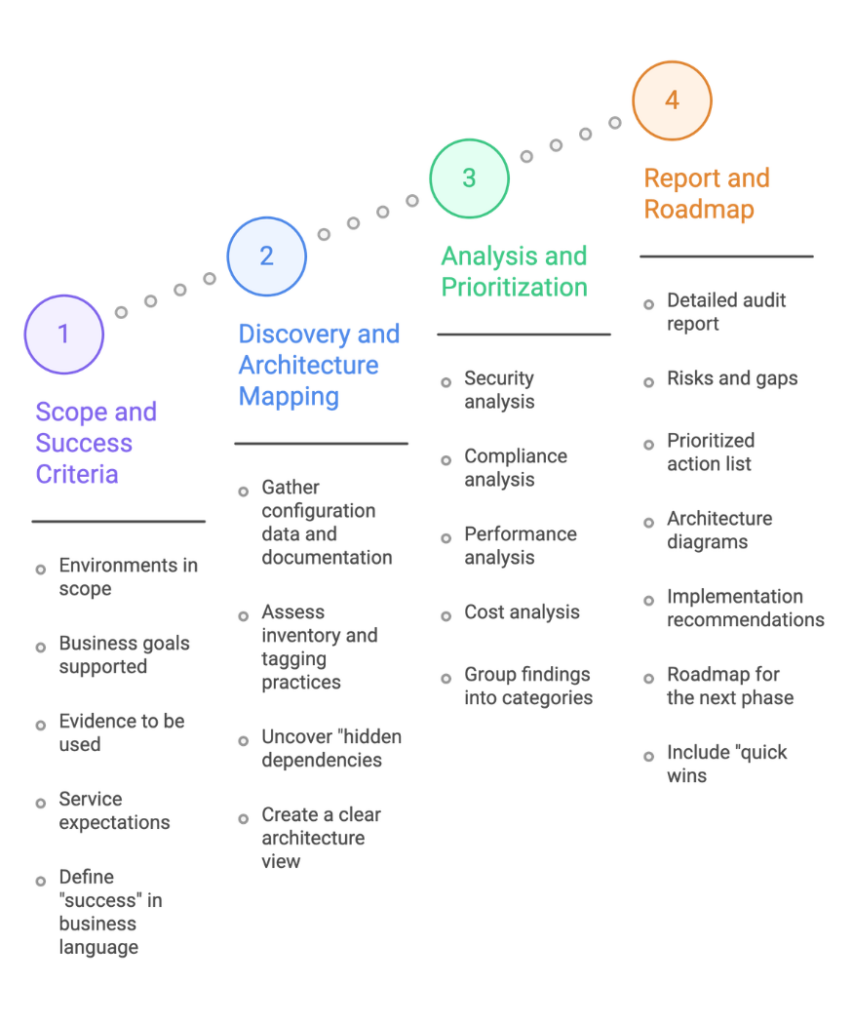
A good audit is not just “look around and send a report.” It’s a structured process designed to reduce uncertainty and produce an execution plan. In practice, the process follows four phases: scope, discovery, analysis, and delivery.
This approach is especially valuable before a migration or major change. One audit proposal explicitly frames the purpose as evaluating current infrastructure, identifying risks, and creating a clear roadmap for a secure and cost-efficient migration . That logic applies even if you are not migrating: you still want a roadmap built on evidence.
Phase 1 — Scope and Success Criteria
Scope is where audits succeed or fail. If the scope is too broad, you drown in details. If it’s too narrow, you miss the risks that actually matter.
This phase defines which environments are in scope (production, staging, multi-cloud, hybrid), what business goals the audit supports (scaling, compliance readiness, cost reduction, migration), and what evidence will be used. It also clarifies service expectations such as uptime targets, availability requirements, and disaster recovery objectives, often tied to SLAs .
A practical tip: define “success” in business language. For example, “reduce monthly cloud spend by addressing the top five waste drivers,” or “reach ISO 27001 audit readiness by closing priority security gaps.” That success framing makes it easier to prioritize findings later.
Phase 2 — Discovery and Architecture Mapping
Discovery is where assumptions get replaced with a map of reality.
Auditors gather configuration data and documentation across compute, networking (VPCs, subnets, routing, security groups), storage and backups, databases, monitoring and logging, HA and redundancy, and disaster recovery readiness . They also assess whether inventory and tagging practices provide full visibility of resources for identification and cost allocation .
This phase often uncovers “hidden dependencies” — services that are still in use but forgotten, older components that cannot be removed without breaking workflows, or workloads that depend on brittle networking rules. Those discoveries are gold, especially before a migration, because they reduce risk of downtime and data loss .
The most useful output here is a clear architecture view: what exists, how it connects, and where the critical paths are.
Phase 3 — Analysis and Prioritization
Now the audit turns raw information into decisions.
Security analysis evaluates IAM controls, least privilege enforcement, MFA status, secrets management, encryption practices, and exposure points . Compliance analysis maps controls to frameworks relevant to your business, such as ISO 27001, GDPR, or HIPAA . Performance analysis looks for bottlenecks, scaling limitations, reliability risks, and monitoring gaps . Cost analysis identifies waste, right-sizing opportunities, and budgeting and allocation improvements .
Prioritization matters. Not every issue is urgent. A good audit groups findings into:
- Critical risks that could lead to breach or downtime
- High-impact optimizations that improve performance or reduce cost fast
- Strategic improvements that increase maturity over time
This is where a provider’s experience shows. The goal is not to list everything wrong. The goal is to choose what to fix first for maximum business impact.
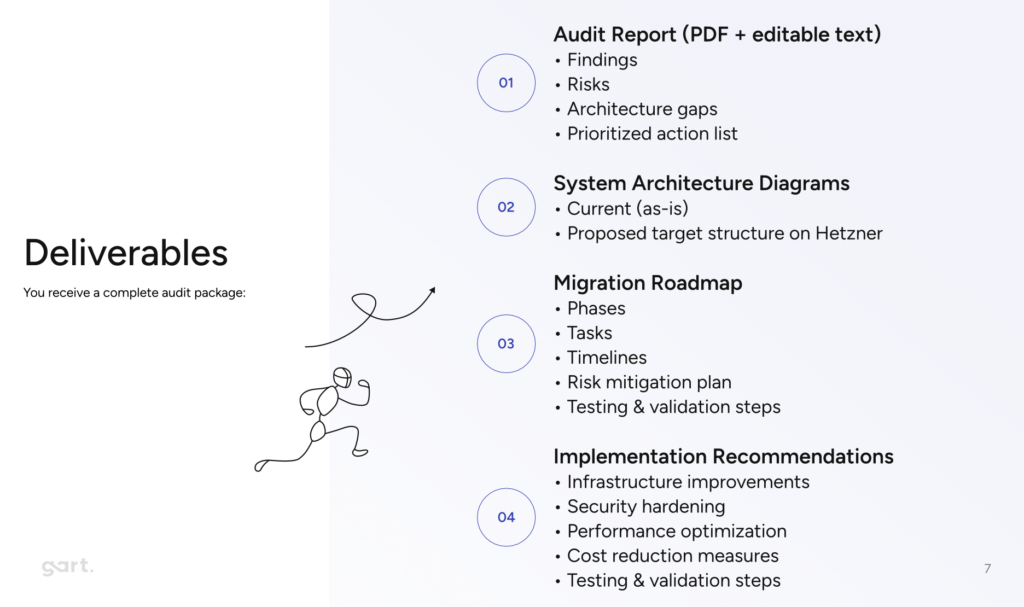
Phase 4 — Report and Roadmap
A professional audit ends with a deliverable package that teams can execute.
Typical deliverables include a detailed audit report, risks and gaps, a prioritized action list, architecture diagrams, implementation recommendations, and a roadmap for the next phase — whether that is migration, optimization, or compliance readiness . This matches what organizations often request: clear recommendations and prioritized fixes, plus a phased plan to implement them safely .
This is also where “quick wins” belong. If you want immediate impact before deep changes, Gart Solutions shares practical guidance on fast improvements in the Quick Wins IT Audit resource.
Real Audit Examples and What You Get with Gart Solutions
Educational theory is useful. Real outcomes are better — especially when you’re trying to justify budget, plan a migration, or prove your infrastructure can scale.
A documented case study shows how an AI art marketplace needed scalable AWS infrastructure to support 250,000 daily active users with 99.9 percent uptime, and the audit findings drove improvements across IAM security (MFA, least privilege), cost optimization (right-sizing and Reserved Instances), reliability (multi-AZ deployments, auto-scaling, monitoring), and data protection (backup policy gaps, Infrastructure as Code practices) . The business impact was exactly what leadership wants: higher reliability, cost savings, stronger security, and better long-term stability .
Another real scenario focused on ISO 27001 readiness and cloud migration preparation. The audit work included reviewing outstanding compliance tasks, securing cloud environments, implementing SSO with MFA, improving encryption and endpoint access controls, establishing a backup and disaster recovery plan, and reinforcing repository security measures . The result was compliance readiness progress, smoother migration execution, and stronger security alignment with ISO expectations .
If your goal is to promote audit work internally, these examples are useful for framing: audits are not “extra work,” they are the mechanism that turns growth and compliance pressure into a controlled plan.
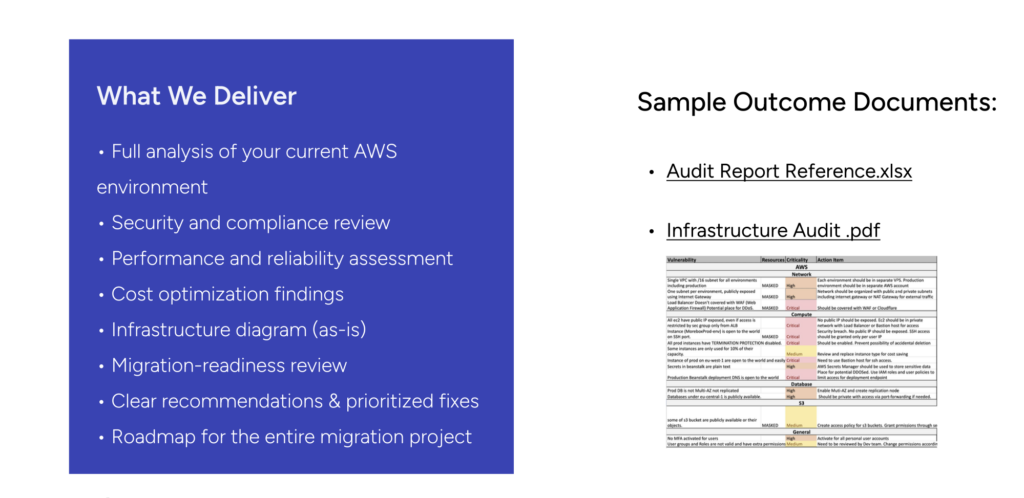
What you typically receive from a Gart Solutions audit
A structured audit engagement is designed to leave you with clarity and execution momentum. One audit scope outlines deliverables such as full environment analysis, security and compliance review, performance and reliability assessment, cost optimization findings, infrastructure diagrams, migration readiness review, and prioritized recommendations plus a roadmap . This approach aligns with what many teams actually need: not a “perfect state,” but a prioritized plan to reach a better state quickly and safely.
If you want to understand the control areas in advance, use the IT Infrastructure Audit Checklist as a reference.
It mirrors common audit coverage such as IAM and MFA enforcement, encryption, logging and SIEM integration, vulnerability management, backup and DR testing, and compliance logging .
Cost, and how to think about value
Audit cost depends on scope, complexity, compliance requirements, and deliverable depth. A focused pre-migration audit proposal lists a price point of $500 for a defined scope, with clear deliverables and roadmap outputs. For larger environments, multi-cloud setups, regulated industries, or deeper security testing, costs scale because evidence collection, analysis, and remediation planning require more time and specialized expertise.
The smarter way to evaluate cost is to compare it to:
- Ongoing cloud waste from over-provisioning and unused resources
- Downtime risk from untested DR and weak observability
- Compliance penalties and deal friction when evidence is missing
- Breach exposure from weak IAM and incomplete monitoring
This is where audits become high-ROI. Savings from right-sizing, improved reliability, reduced incident frequency, and faster compliance readiness often outweigh the audit cost — and you gain a more scalable foundation.
Why organizations choose Gart Solutions
An infrastructure audit is only as valuable as the expertise behind it. Gart Solutions combines DevOps engineering, cloud architecture, compliance engineering, and security best practices into one structured methodology, supported by real engagements focused on scalability, ISO readiness, and operational optimization .
If your organization is questioning whether its infrastructure can support upcoming business challenges, an audit is often the most strategic first step. Explore the full scope here
Conclusion
An IT Infrastructure Audit is not a technical luxury. It is a practical way to turn uncertainty into control.
It helps you prove whether your architecture can scale, whether access controls are truly safe, whether monitoring can detect incidents early, whether backups and disaster recovery will work under stress, and whether cloud spend matches real demand. It connects compliance expectations to actual configurations, which matters when frameworks like ISO 27001, GDPR, and HIPAA are part of your business reality .
If your infrastructure must support growth, audits are the moment you stop guessing and start managing with evidence. If you want a structured, execution-friendly audit that produces a clear roadmap, explore Gart Solutions’ IT Audit Services.
Contact Us and let’s start your audit!