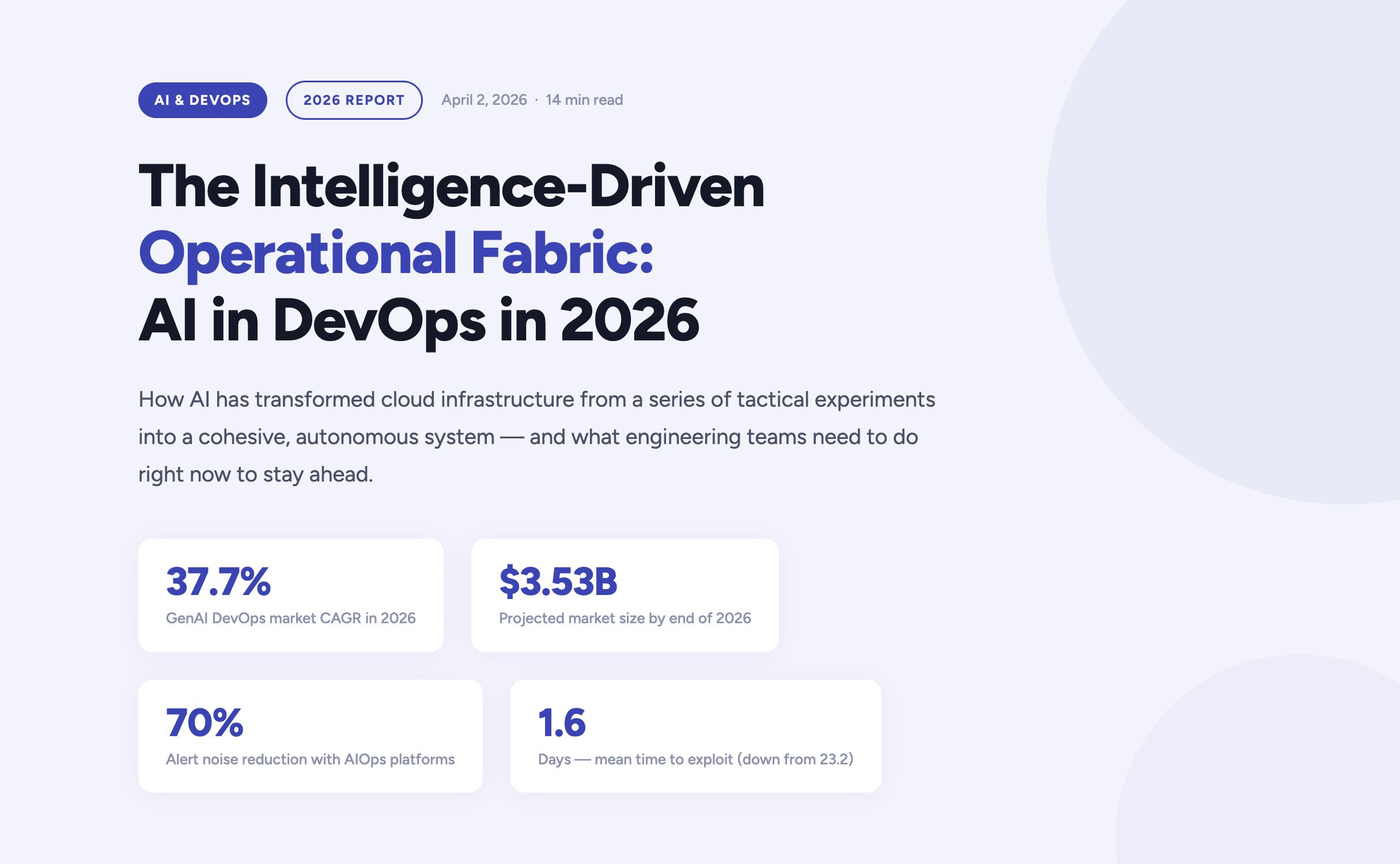
The year 2026 marks a definitive turning point in how enterprises build, deploy, and operate software. Artificial Intelligence has moved far beyond the experimental phase inside DevOps pipelines — it now forms the connective tissue of the entire software delivery lifecycle. According to current market analysis, the generative AI segment of the DevOps market is growing at a compound annual rate of 37.7%, expected to reach $3.53 billion by the end of this year alone.
For engineering teams, platform engineers, and CTOs navigating this shift, the questions are no longer "should we adopt AI?" but rather "how do we govern it?", "where does it amplify our strengths?", and critically — "where does it expose our weaknesses?". This article answers those questions, grounded in the realities of operating cloud infrastructure in 2026.
https://youtu.be/4FNyMRmHdTM?si=F2yOv89QU9gQ7Hif
The AI velocity paradox — why more code isn't always better
One of the most striking findings in the 2026 DevOps landscape is what researchers have begun calling the AI Velocity Paradox. AI-assisted coding tools have dramatically accelerated the code creation phase of the Software Development Life Cycle. However, the downstream delivery systems responsible for testing, securing, and deploying that code have often failed to keep pace — creating a structural mismatch between production and operations capacity.
The data tells a clear story. Teams that use AI coding tools daily are three times more likely to deploy frequently — but they also report significantly higher rates of quality failures, security incidents, and engineer burnout.
The AI DevOps maturity gap — occasional vs. daily AI tool users
The AI DevOps Maturity Gap — 2026 Analysis
Performance Indicator
Occasional AI Usage
Daily AI Usage
Daily deployment frequency
15% of teams
45% of teams
Frequent deployment issues
Minimal
69% of teams
Mean Time to Recovery (MTTR)
6.3 hours
7.6 hours
Quality / security problems
Baseline
51% quality / 53% security
Engineers working overtime
66%
96%
The root cause is structural: a "six-lane highway" of AI-accelerated code generation is funneling into a "two-lane bridge" of operational capacity. Engineers spend an average of 36% of their time on repetitive manual tasks — chasing tickets, rerunning failed jobs, manually validating AI-generated code — while developer burnout now affects 47% of the engineering workforce.
The implication is clear: AI does not automatically improve DevOps outcomes. Applied to brittle pipelines or fragmented telemetry, it accelerates instability. Applied to robust, standardized foundations, it becomes a force multiplier. The organizations that succeed in 2026 are those that modernize their entire delivery system — not just the IDE.
Tech should do more than work — it should do good, and it should scale purposefully."
Fedir Kompaniiets, CEO, Gart Solutions
Intent-to-Infrastructure — the evolution of IaC
Infrastructure as Code has been a DevOps cornerstone for years, but the model is undergoing a fundamental transformation in 2026. The industry is moving away from hand-crafted Terraform scripts and declarative state management toward what practitioners call Intent-to-Infrastructure — AI-powered platforms that interpret high-level business requirements and autonomously provision compliant, cost-optimized environments.
The evolution of Infrastructure as Code
The Evolution of Infrastructure as Code
Generation
Primary Mechanism
Governance Model
Outcome Focus
IaC 1.0 — Legacy
Manual scripting (Terraform, Ansible)
Periodic manual audits
Resource provisioning
IaC 2.0 — Standard
Declarative state management
Automated policy checks
Environment consistency
Intent-Driven (2026)
AI translation of requirements
Continuous autonomous reconciliation
Business-aligned outcomes
In the intent-driven model, a developer can express a requirement in plain language — for example, "provision a production-ready Kubernetes cluster with SOC 2-compliant networking for our EU-West workload" — and the platform autonomously generates, validates, and manages the resources. Compliance is no longer a retrospective audit exercise; it is embedded at the moment of generation.
This approach directly addresses one of the most persistent gaps in enterprise cloud governance: the Confidence Gap. While 77% of organizations report confidence in their AI-generated infrastructure, only 39% maintain the fully automated audit trails needed to actually verify those outputs. Intent-driven platforms close this gap by creating immutable, traceable records of every provisioning decision.
Key IaC Capabilities in 2026
Natural language provisioning — Describe infrastructure requirements in plain English, receiving validated, compliant Terraform or Pulumi code.
Golden path enforcement — Pre-approved patterns ensure every environment is secure by default, reducing misconfiguration risk.
Continuous autonomous reconciliation — AI continuously monitors for drift and self-corrects without human intervention.
Policy-as-code integration — OPA, Sentinel, and custom guardrails are embedded into generation pipelines, not added as an afterthought.
Cost-aware provisioning — FinOps constraints are applied at generation time, preventing over-provisioning before it happens.
AIOps and the new era of observability
As cloud-native architectures scale in complexity, the challenge facing modern platform engineers is no longer the collection of telemetry data — it is the meaningful interpretation of it. According to Gartner, over 60% of production incidents in 2026 are caused by poor interpretation of existing data, not a lack of visibility. Teams are drowning in signals while missing the meaning.
This has driven the rapid maturation of AIOps — Artificial Intelligence for IT Operations — which shifts the operational model from reactive incident firefighting to predictive, self-healing systems. Modern AIOps platforms in 2026 are built on three core capabilities:
Predictive incident management
AI models trained on historical delivery patterns, change velocity data, and error logs can now surface probabilistic risk assessments hours before a service outage occurs. Rather than reacting to pages at 3am, platform teams receive prioritized warnings during business hours with recommended remediation paths.
Autonomous remediation
For well-understood failure patterns — pod OOMKill events, connection pool exhaustion, SSL certificate expiry — AI agents can execute validated runbooks autonomously, patching or scaling systems within seconds of detection. Human intervention is reserved for novel or high-impact scenarios.
Intelligent alert prioritization
By correlating weak signals across application, infrastructure, and network layers, modern AIOps platforms reduce alert noise by up to 70%. Engineers no longer triage a wall of Slack notifications — they engage with a curated, context-rich incident queue.
60%+
Incidents from misinterpretation
70%
Less alert noise via AIOps
36%
Engineer time lost to manual tasks
eBPF
Deep visibility sans code changes
DevSecOps 2.0 — when autonomous security becomes non-negotiable
The security landscape of 2026 is unforgiving. The mean time to exploit a known vulnerability has collapsed from 23.2 days in 2025 to just 1.6 days — faster than any human-speed security process can respond. This has driven a fundamental rearchitecting of DevSecOps, from a set of "shift left" practices to a fully autonomous, self-healing security model.
Traditional vs. AI-Enhanced DevSecOps
Security Metric
Traditional DevSecOps
AI-Enhanced DevSecOps (2026)
Vulnerability identification
Periodic scanning of dependencies
Real-time scanning of code, containers, and runtimes
Threat response
Manual triage and incident response
Automated isolation of compromised resources
Compliance evidence
Manual spreadsheet collection
Automated, immutable audit trails
Risk assessment
Static CVSS vulnerability scoring
Contextual scoring based on reachability and blast radius
For regulated industries — healthcare, financial services, legal — compliance is no longer a quarterly exercise. In 2026, the most resilient organizations implement Compliance-by-Design infrastructure, where HIPAA, HITECH, SOC 2, and PCI-DSS controls are embedded directly into DevOps pipelines. Every commit, every deployment, every configuration change produces a verifiable, immutable compliance artifact — not as overhead, but as a natural byproduct of the engineering workflow.
The shift is cultural as well as technical: compliance is now understood as a growth enabler, not a hindrance. Organizations that can demonstrate real-time security posture attract enterprise customers, pass procurement audits, and move faster through regulated markets.
FinOps and the economics of intelligent infrastructure
Cloud spending has become a top-five P&L line item for most mid-to-large enterprises in 2026. Uncontrolled SaaS sprawl, over-provisioned Kubernetes clusters, and idle development environments have made AI-driven FinOps not just a cost-optimization strategy, but a boardroom-level priority.
The latest generation of FinOps tooling applies AI in two directions: reactive optimization (identifying and eliminating waste in existing infrastructure) and proactive cost governance (embedding unit cost constraints into provisioning workflows before resources are ever created). The results are significant — in some cases, organizations achieve savings of up to 80% on AWS compute budgets through spot instance migration, rightsizing, and automated idle resource termination.
Increasingly, FinOps and sustainability are being treated as two sides of the same coin. By eliminating idle compute and over-provisioned infrastructure, organizations simultaneously reduce cloud spend and digital carbon footprint — what practitioners are calling Green FinOps. At Gart Solutions, 70% of client workloads are optimized to run on green cloud platforms as part of a carbon-neutral-by-default infrastructure strategy.
"Applied to brittle pipelines or fragmented telemetry, AI accelerates instability. Applied to robust, standardized foundations, it becomes the force multiplier that allows organizations to scale resilience at the speed of code."
Roman Burdiuzha, CTO, Gart Solutions
Human-on-the-Loop governance — the new control model
As AI agents take over increasing portions of the operational layer, one of the defining debates of 2026 is where to draw the line on autonomy. The industry consensus has moved away from both extremes — fully manual "Human-in-the-Loop" (HITL) processes that create bottlenecks, and fully autonomous systems that introduce unacceptable risk — toward a middle path: Human-on-the-Loop (HOTL) governance.
In the HOTL model, AI agents operate autonomously within predefined guardrails. Humans shift from being operators to being overseers — setting policies, reviewing exceptions, and vetoing high-stakes decisions. The architecture is built on four pillars:
Step and cost thresholds — Hard limits on the number of actions an agent can execute per session, or the total tokens consumed, prevent infinite loops and runaway infrastructure costs.
The Veto Protocol — For high-risk decisions (budget reallocations, production changes above a defined blast radius), the agent surfaces a structured "Decision Summary" for asynchronous human review before proceeding.
Identity and access control — Agents are granted short-lived, task-scoped credentials. They never hold standing access to production environments; every session is authenticated, logged, and time-bounded.
Immutable audit trails — Every agent action generates a cryptographically signed record, ensuring full traceability for compliance and post-incident review.
This governance model is not a limitation on AI capability — it is what makes AI capability trustworthy enough to deploy at scale in regulated, high-stakes environments.
Industry-specific transformations
Manufacturing — the intelligent shop floor
Manufacturing organizations face a persistent challenge: deeply siloed data environments where Management Execution Systems (MES), ERP platforms, IoT sensor networks, and POS systems rarely communicate in real time. In 2026, cloud-native, AI-powered integration layers are dissolving these silos — enabling predictive maintenance, real-time production analytics, and supply chain transparency from raw material to finished product.
For one manufacturing client, a custom Green FinOps strategy eliminated over-provisioned infrastructure while a blockchain-based supply chain integration created end-to-end product traceability. The combined impact: measurable cost savings, improved regulatory compliance, and a more resilient operational model.
Healthcare — securing the patient data journey
In healthcare, the stakes of a misconfigured infrastructure are clinical as well as financial. DevOps practices in this sector are purpose-built around securing electronic health records, ensuring FDA and HIPAA compliance, and protecting medical device software against zero-day vulnerabilities. AI-driven monitoring continuously scans for "blind spots" that could lead to clinical data loss — not just at deployment time, but across the full runtime lifecycle.
SaaS and fintech — scaling without headcount sprawl
SaaS companies and fintech startups are increasingly turning to DevOps-as-a-Service to manage global availability and rapid iteration cycles without proportional growth in engineering headcount. By embedding automated security tasks, infrastructure-as-code provisioning, and AI-driven observability into every deployment, these teams can scale their products while maintaining the operational quality standards that enterprise customers demand.
Build your intelligent operational fabric
Partner with Gart Solutions for resilient, AI-powered cloud infrastructure.
Talk to an engineer →
Your 2026 AI DevOps roadmap
Organizations that are successfully navigating the AI transition in 2026 share a common pattern. They did not bolt AI onto existing processes — they built the foundations first, then amplified them. The roadmap has four distinct stages:
Data readiness audit
Ensure that observability data — logs, metrics, traces, events — is clean, normalized, and accessible across organizational silos. AI models are only as good as the telemetry they consume. Fragmented, noisy data produces fragmented, unreliable AI recommendations.
High-ROI use case selection
Start with workflows where AI delivers measurable, auditable value — automated testing, incident triage, IaC generation, cost anomaly detection. Build confidence and governance muscle before expanding to higher-risk autonomous operations.
Governance architecture
Establish the guardrails — HOTL oversight protocols, agent identity controls, immutable audit trails, cost thresholds — before deploying autonomous agents into production environments. Governance is not friction; it is what makes speed sustainable.
AI fluency across the engineering organization
Develop the skills required to oversee, interact with, and continuously improve intelligent agents. The competitive advantage in 2027 will belong to teams that can govern AI effectively — not just deploy it.
The 2026 AI-native DevOps toolchain
The toolchain of 2026 is defined by intelligence at every stage of the delivery pipeline. Unlike earlier generations of tooling that added AI as an afterthought, these platforms are AI-native — built from the ground up to learn, adapt, and act autonomously.
The AI DevOps Tooling Landscape (2026)
Tool
Domain
Key AI Capability
Snyk
Security
Real-time AI scanning for dependencies, containers, and IaC
Spacelift
Infrastructure
Multi-tool IaC management with AI policy enforcement
Harness
CI/CD
Intelligent software delivery with autonomous deployment verification
Datadog
Monitoring
AI-augmented full-stack visibility, anomaly detection, log correlation
PagerDuty
Incident Management
ML-based event correlation and intelligent noise reduction
StackGen
Platform Eng.
AI-powered intent-to-infrastructure generation
K8sGPT
Kubernetes
Natural language explanation and diagnosis of cluster errors
Sysdig Sage
DevSecOps
AI analyst for runtime security threat detection and CNAPP
Cast AI
FinOps
Autonomous Kubernetes cost optimization and rightsizing
Conclusion — from manual doers to intelligent orchestrators
The convergence of AI and DevOps in 2026 has redefined what is possible in software delivery. The organizations that thrive are not those that deploy the most AI tools — they are those that build the most resilient foundations and then amplify those foundations intelligently. Cloud infrastructure is no longer a hosting environment. It is an intelligent fabric that predicts, learns, and self-heals.
The transition is as cultural as it is technical. Engineering teams are moving from being manual operators to being intelligent orchestrators — governing not through a queue of tickets, but through the strategic definition of intent and the rigorous enforcement of outcomes. For those willing to make this shift, the competitive advantage is significant, durable, and compounding.
As Gart Solutions has built its entire practice around: tech should do more than work — it should do good, and it should scale purposefully.
Build your intelligent operational fabric with us
A boutique DevOps and cloud infrastructure partner for engineering teams that want to scale reliably, securely, and sustainably — without the overhead of a hyperscaler.
DevOps as a Service
Full-lifecycle CI/CD design, automation, and platform engineering for teams that need reliable, battle-tested delivery pipelines at startup speed.
Cloud migration & adoption
Strategic migration from on-premise or legacy cloud environments to modern, cost-optimized, and green cloud architectures on AWS, GCP, or Azure.
DevSecOps automation
Compliance-by-design infrastructure for regulated industries — embedding HIPAA, SOC 2, and PCI-DSS controls directly into your delivery pipeline.
AIOps & observability
End-to-end observability strategy — from eBPF telemetry and distributed tracing to AI-powered alerting, anomaly detection, and autonomous runbook execution.
FinOps & cloud cost optimization
Cloud cost audits, spot instance migration, idle resource termination, and Kubernetes rightsizing — achieving savings of up to 80% on cloud budgets.
Managed infrastructure
24/7 proactive management of your cloud infrastructure, with SLA-backed uptime guarantees, automated scaling, and continuous compliance monitoring.
SOC (Service Organization Control) audits are a way to show that your internal processes are up to standard—whether it's managing financial data or protecting sensitive information like customer privacy.
SOC 2 compliance is a set of guidelines that helps companies manage and protect customer data. It's especially important for businesses that offer services to other companies, like those in IT and cloud services.
If your business handles sensitive information, SOC 2 compliance audit is crucial. Preparing for a SOC 2 audit means following clear steps to make sure your data protection measures are working effectively.
In today’s digital age, being SOC 2 compliant shows your customers that you prioritize data security, building trust and confidence in your business.
What is SOC 2?
SOC 2 (System and Organization Controls 2) is a set of compliance standards developed by the American Institute of Certified Public Accountants (AICPA). It is aimed at service organizations that store customer data in the cloud.The audit assesses a company’s systems and processes based on five trust service criteria: security, availability, processing integrity, confidentiality, and privacy.
Unlike other frameworks that are rigid, SOC 2 is flexible and allows companies to select which trust service criteria they need to focus on, depending on their operational needs.
Trust Services Criteria
SOC 2 focuses on five key trust services criteria:
Security: Ensuring that systems are protected against unauthorized access (both physical and digital).
Availability: Making sure systems are available for operation and use as expected.
Confidentiality: Protecting sensitive information from unauthorized access.
Processing Integrity: Ensuring that data processing systems operate correctly, delivering accurate results.
Privacy: Protecting personal information collected and ensuring it is used appropriately.
Out of these five criteria, security is the only mandatory one. However, most organizations also focus on availability and confidentiality, as they are critical for maintaining customer trust.
Pre-Audit Preparations
Defining the Audit Scope
The first step in preparing for a SOC 2 audit is clearly defining the scope. This scope outlines the specific systems and processes that will be evaluated. It is essential to ensure that the defined information system – infrastructure, software, people, data, and processes – still meets the current business needs. If there have been changes, adjustments to the scope may be necessary.
Control Customization
SOC 2 allows organizations to customize controls based on their operational environment. For example, if your organization has shifted from a waterfall to an agile development process, the controls should reflect this change. Ensuring that controls align with how the business operates helps auditors understand your environment better, leading to a smoother audit process.
Team Readiness
Preparing the internal team for the audit is crucial. Assigning clear roles, setting agendas, and conducting control spot-checks beforehand can save time and ensure that everyone knows what is expected during the audit. Key personnel must understand their roles in explaining controls, providing evidence, and participating in system walkthroughs.
Ask how Gart Solutions can help you with SOC 2 compliance.
Contact us today.
SOC 2 Audit Process
The SOC 2 audit is not a one-size-fits-all. Organizations can choose which of the trust service criteria they want to be audited on. This flexibility allows businesses to tailor their audit based on specific operational needs. For example, an e-commerce platform might focus on security and availability, while a healthcare provider might prioritize security and confidentiality.
The audit process itself involves several steps:
Documentation: It is essential to document all processes and policies. Auditors will review this documentation to verify that security measures are in place and that they are being followed. For example, if a company states that it conducts annual access reviews for AWS, it must provide evidence that these reviews actually took place.
Audit Execution: Auditors will examine the company’s controls to ensure compliance. This can involve reviewing data logs, verifying access permissions, and conducting interviews with key personnel.
Audit Types:
Type 1 Audit: A snapshot of the organization’s compliance at a specific point in time.
Type 2 Audit: Reviews the operational effectiveness of controls over a period, typically 12 months.
*The key difference between Type I and Type II audits is time. A Type I audit checks if the controls you have in place are working at a single point in time. A Type II audit goes further by testing whether those controls actually worked over a longer period, usually at least six months. Both SOC 1 and SOC 2 audits can come in either Type I or Type II formats, which is why it can get confusing.
Critical Controls for SOC 2 Compliance
SOC 2 compliance requires several key controls across the organization. Some of the most important include:
Access Controls: Implementing principles like "least privilege," where only necessary personnel have access to sensitive data. Multi-factor authentication is also required for accessing sensitive systems like cloud services.
Encryption: Both encryption at rest (data stored) and encryption in transit (data moving between systems) are crucial. Encryption protects sensitive information from unauthorized access.
Change Management: In software companies, it’s important to maintain strict version control and require independent approval of changes. This ensures that code changes are securely managed and that no unauthorized changes affect the system.
Post-Audit Steps
Reviewing the System DescriptionAfter the audit fieldwork is completed, the next step is reviewing the system description. This section of the SOC 2 report details the organization’s systems and processes. It must be reviewed annually to ensure that it reflects any changes in the company’s operations. The system description can be lengthy, often around 30 pages, so early preparation is necessary.
Maintaining Compliance for Future AuditsOnce the initial audit is done, it is important to establish an ongoing compliance program. This includes regular control checks, ensuring that controls continue to operate as expected. For example, if a control requires quarterly user access reviews, these must be conducted regularly. Assigning responsibility for each control ensures accountability and reduces the risk of future non-compliance.
Audit Closure and Next StepsOnce the audit is complete, it is essential to schedule a closeout meeting with the auditor to discuss improvements and plan for future audits. This meeting should also cover how to use the SOC 2 report for business purposes, such as sharing it with stakeholders or using it as a marketing tool to demonstrate compliance. Additionally, preparing for the next year’s audit by scheduling key dates and responsibilities is recommended.
SOC 2 Audit Checklist
SOC-2-Audit-ChecklistDownload
Human Factors in SOC 2 Compliance
While SOC 2 compliance focuses heavily on technical controls, human factors also play a critical role. Processes like employee onboarding and offboarding must be managed consistently to ensure that no unauthorized individuals gain access to systems. For instance, an overlooked background check due to an HR error could compromise compliance.
Automation tools, such as Secureframe, are invaluable in mitigating risks associated with human error. By automating reminders for critical processes (like access reviews or background checks), companies can reduce the chance of non-compliance due to manual oversights.
SOC 1 vs. SOC 2
SOC 1 audits, also known as SSAE16 audits, look at how well your company controls financial reporting. SOC 2 audits focus on other important aspects like security, system availability, data processing accuracy, confidentiality, and privacy. Think of it like comparing apples to oranges—they’re both fruit but serve different needs.
Key differences between SOC 2 and ISO 27001
Table
AspectSOC 2ISO 27001DefinitionSet of audit reports based on Trust Service Criteria (TSC)Standard for an Information Security Management System (ISMS)Geographical ApplicabilityPrimarily used in the United StatesInternationally recognizedIndustry ApplicabilityService organizations across various industriesOrganizations of any size or industryComplianceAttested by a Certified Public Accountant (CPA)Certified by an accredited ISO certification bodyFocusProves security level of systems against static principles and criteriaDefines, implements, operates, controls, and improves overall securityReport TypesType 1 and Type 2 reportsCertification audit and surveillance auditsPurposeValidates internal controls related to information systemsEstablishes and maintains an ISMS
Conclusion
SOC 2 compliance is essential for organizations that handle sensitive data, particularly in the B2B sector. Achieving SOC 2 certification not only demonstrates that a company takes security seriously but also enables it to expand its business by selling to larger, security-conscious clients. SOC 2 is more than just a compliance program; it is a powerful tool for fostering customer trust and enhancing business opportunities.
How can Gart Solutions help with SOC 2 compliance?
Gart Solutions offers:
Gap assessments and remediation
Secure cloud infrastructure setup
Automated evidence collection
Policy documentation support
Post-audit compliance maintenanceOur team helps you streamline the entire SOC 2 journey and stay ready for future audits.
Imagine this: You’re busy running your clinic, pharmacy, or health tech firm when suddenly an email arrives – you’re getting audited for HIPAA compliance. Panic sets in. What if your policies aren’t updated? What if employee training is outdated? What if a single misstep costs you millions in fines?
This isn’t an imaginary worst-case scenario. HIPAA audits are real, random, and rigorous. With penalties ranging from $50,000 per incident to $1.5 million per year, failing an audit can financially and reputationally cripple your business.
But here’s the good news: You can prepare in advance. This guide will break down everything you need to know in simple, practical steps to ensure you’re not just compliant on paper but audit-ready anytime.
We’ll cover:
What HIPAA really is (without jargon)
Who needs to comply (it’s not just hospitals)
What gets audited
The three main HIPAA rules
Step-by-step HIPAA audit preparation checklist
How to avoid common pitfalls
How experts like Gart Solutions can help you stay secure and compliant
Ready to protect your business and your patients’ trust? Let’s dive in.
What is PHI (Protected Health Information)?
HIPAA's main goal is to keep patients' medical records and personal health details safe from being shared without permission. It sets nationwide rules to make sure that health information stays private, accurate, and accessible only to the right people. These rules apply to health plans, doctors, hospitals, and any businesses that handle patient information.
Protected Health Information (PHI) is any health-related data that can be traced back to a specific person. This includes things like medical records, names, social security numbers, and even fingerprints or other biometric data. HIPAA requires that all health information connected to personal details is considered PHI and must be kept secure.
The U.S. Department of Health and Human Services (HHS) has defined 18 unique identifiers that classify health information as PHI, including but not limited to:
Names
Dates (except years)
Social security numbers
Medical record numbers
Email addresses
Device identifiers
Biometric data (fingerprints, face scans)
Who Must Comply with HIPAA?
HIPAA compliance is mandatory for entities that handle PHI, including:
Healthcare providers: Hospitals, clinics, nursing homes, pharmacies.
Health plans: Health insurance companies, Medicare, Medicaid.
Health clearinghouses: Organizations that process health data like billing services and data management firms.
Business associates: Third-party vendors, including billing companies, consultants, and cloud service providers, who handle PHI on behalf of covered entities.
HIPAA compliance extends beyond healthcare providers to include business associates—third-party entities that perform services involving the use or disclosure of Protected Health Information (PHI) on behalf of covered entities like hospitals or clinics. Examples of business associates include:
Billing companies
Cloud service providers
Consultants
Transcription services
Data storage firms
Business associates are required to ensure the same level of protection for PHI as the primary covered entities, such as hospitals and insurance companies. This means they must adhere to HIPAA’s Privacy, Security, and Breach Notification rules. If a breach occurs or there’s non-compliance, business associates face the same penalties, ranging from $50,000 fines per incident to $1.5 million annually.
Key takeaway:If you store, process, access, or transmit PHI in any capacity, HIPAA applies to you. No exceptions.
The Three Main Rules of HIPAA
HIPAA compliance is governed by three primary rules:
Privacy Rule
This rule controls how personal health information (PHI) can be used and shared. It focuses on keeping patient information safe from unauthorized access while still allowing healthcare providers to share it when needed for treatment or running their services. It limits who can see a patient’s health information and under what conditions it can be shared, giving patients control over their personal health details.
Security Rule
This rule is about protecting electronic health information (ePHI). It requires security measures like encryption, access controls, and monitoring logs to keep data safe from breaches. Whether the data is being stored or sent, this rule ensures it is protected. It also requires healthcare organizations to have administrative, physical, and technical safeguards in place to keep electronic health data secure.
Breach Notification Rule
If there’s a breach involving unsecured health information, this rule requires healthcare providers to notify the affected individuals and, in some cases, the government and media. The individuals must be informed within 60 days if their health information was accessed without permission. If the breach is large, the Department of Health and Human Services (HHS) and the media may also need to be notified.
Penalties for Non-Compliance
Failing to comply with HIPAA can lead to severe consequences. Financial penalties range from $50,000 per incident to $1.5 million per violation category per year. Persistent violations or multiple breaches can result in multi-million-dollar fines, and in some cases, criminal charges.
Even if an organization is found to be compliant today, they may face fines for any previous deficiencies. These penalties can be financially debilitating, highlighting the importance of maintaining a thorough and consistent compliance plan.
What Is a HIPAA Audit?
A HIPAA audit is a formal assessment conducted by the Department of Health and Human Services (HHS) Office for Civil Rights (OCR) to verify that healthcare providers, health plans, and their business associates comply with HIPAA’s privacy and security requirements.
Why do HIPAA audits happen?
Random selection for proactive audits
Complaints filed by patients or staff
Data breach incidents reported to OCR
These audits are not just paperwork reviews. They evaluate your actual practices, training programs, and technical safeguards. In recent years, OCR contracted firms like FCI Federal to conduct these audits, expanding audit frequency and depth.
Types of HIPAA audits:
Desk audits – You submit requested documentation electronically within a strict timeframe (usually 10-14 days).
On-site audits – Auditors visit your physical office to observe operations, interview staff, and inspect security practices.
If deficiencies are found, you may be required to submit a Corrective Action Plan (CAP) and could face monetary penalties depending on severity.
Key takeaway:A HIPAA audit tests your real-world compliance, not just your written policies.
What Gets Audited During a HIPAA Audit?
Auditors review both current and historical compliance efforts, meaning that even if you updated policies last week, outdated practices from last year can still lead to penalties.
Areas commonly audited:
Privacy policies and procedures: Are they up to date and aligned with HIPAA standards?
Security risk assessment reports: Have you identified and addressed vulnerabilities in your systems?
Employee training records: Has your staff been trained regularly on HIPAA requirements?
Business Associate Agreements (BAAs): Are they signed, current, and compliant with HIPAA rules?
Breach notification procedures: Do you have a documented and tested plan in place?
Technical safeguards: Encryption, access controls, audit logs, and authentication systems.
Physical safeguards: Locked storage, secure facility access, workstation security policies.
Incident response plans: Are you prepared to handle and report breaches effectively?
What is the auditor looking for?
They want proof that:
You understand HIPAA requirements
You have implemented policies, procedures, and safeguards
Your team is trained and compliant
You maintain documentation to demonstrate compliance
Failure to provide these quickly can trigger deeper investigations or fines.
Implementation and Best Practices
HIPAA compliance requires organizations to adopt several best practices, including:
Employee Training: All employees handling PHI must be thoroughly trained on HIPAA policies and procedures.
Risk Management: Organizations should regularly assess risks to PHI and take necessary steps to mitigate them.
Access Control: Only authorized personnel should have access to PHI, ensuring that medical information is protected from unauthorized access.
HIPAA compliance checklist
HIPAA-Compliance-ChecklistDownload
Common Mistakes to Avoid During HIPAA Audits
Even organizations with good intentions fail audits due to avoidable errors. Here are critical mistakes to avoid:
Incomplete risk assessments – Simply checking boxes without thorough evaluation.
Outdated policies – Using templates created years ago without updates.
No employee training records – Failing to document who attended HIPAA training and when.
Unencrypted data – Storing PHI in cloud or local systems without proper encryption.
Weak password policies – Allowing default passwords or sharing logins.
Missing BAAs – Working with vendors handling PHI without signed Business Associate Agreements.
Ignoring small breaches – Failing to document or notify minor unauthorized disclosures.
No audit logs – Lack of monitoring for who accesses PHI and when.
Avoid these pitfalls by conducting internal audits regularly, keeping policies current, and working with compliance experts who can identify gaps before OCR finds them.
How Gart Solutions Can Help with HIPAA Audits
Preparing for a HIPAA audit isn’t just about checking off compliance boxes – it’s about implementing security and privacy best practices that protect your patients and your business long-term. This is where Gart Solutions comes in.
Here’s how Gart Solutions can support your HIPAA compliance:
Cloud Infrastructure DesignDesign and deploy cloud environments compliant with HIPAA standards, ensuring scalable and secure PHI storage.Cloud Infrastructure DesignDesign and deploy cloud environments compliant with HIPAA standards, ensuring scalable and secure PHI storage.
Data Encryption ImplementationEncrypt sensitive data in transit and at rest to prevent unauthorized access.
Automated Compliance MonitoringUse DevOps practices to continuously scan for misconfigurations and vulnerabilities, resolving them in real time.
Audit Trail CreationDeploy logging and monitoring tools to track system activity and demonstrate compliance during audits.
Incident Response AutomationDevelop automated procedures to minimize breach impact and ensure fast compliance with HIPAA breach notification rules.
Risk Assessment and ManagementConduct thorough risk assessments, implement remediation plans, and monitor for ongoing compliance.
Backup and Disaster RecoverySet up secure backup systems and disaster recovery plans to ensure data is always recoverable.
Business Associate Agreements (BAA) ManagementHelp draft and maintain compliant BAAs with cloud vendors and business associates.
By partnering with Gart Solutions, you not only prepare for HIPAA audits but also build a resilient and secure IT environment that earns your patients’ trust and protects your business.
Gart Solutions can design and implement cloud infrastructure that adheres to HIPAA security and privacy standards. This includes ensuring that the architecture is secure, scalable, and meets the technical safeguards required for protected health information (PHI) handling.
One of the core requirements for HIPAA compliance is ensuring that sensitive data, such as PHI, is encrypted both in transit and at rest. Gart Solutions can implement encryption protocols on cloud services, ensuring that all data is protected from unauthorized access.
Using DevOps practices, Gart Solutions can automate the monitoring of cloud environments for HIPAA compliance. By setting up automated scans and alert systems, they can ensure that any misconfigurations or potential breaches are identified and resolved in real-time.
HIPAA requires that organizations maintain a record of access and activity for all systems handling PHI. Gart Solutions can deploy logging and monitoring tools to ensure a robust audit trail. This makes it easier to demonstrate compliance during an audit.
In case of a security incident, a fast and effective response is critical. Gart Solutions can automate incident response procedures, minimizing response time and ensuring that any HIPAA violations are addressed immediately.
Gart Solutions can conduct regular risk assessments, helping organizations identify vulnerabilities in their cloud infrastructure. They can then implement remediation plans and continuously monitor the environment to reduce the risk of non-compliance.
HIPAA requires that organizations have plans for backup and disaster recovery in place. Gart Solutions can set up automated, secure backups and disaster recovery solutions, ensuring that data is always recoverable and protected from loss.
For any cloud services provided to healthcare organizations, a BAA is required to establish responsibilities for HIPAA compliance. Gart Solutions can help navigate the process of drafting and maintaining BAAs with cloud vendors, ensuring proper legal protection and compliance.
These services ensure that organizations meet HIPAA requirements while maintaining efficient, secure cloud operations.
Conclusion
HIPAA serves as a cornerstone of healthcare privacy and security regulations, ensuring that individuals' health data is protected. Healthcare providers, insurance companies, and associated businesses must understand and adhere to HIPAA's rules to avoid heavy penalties and safeguard patient trust.