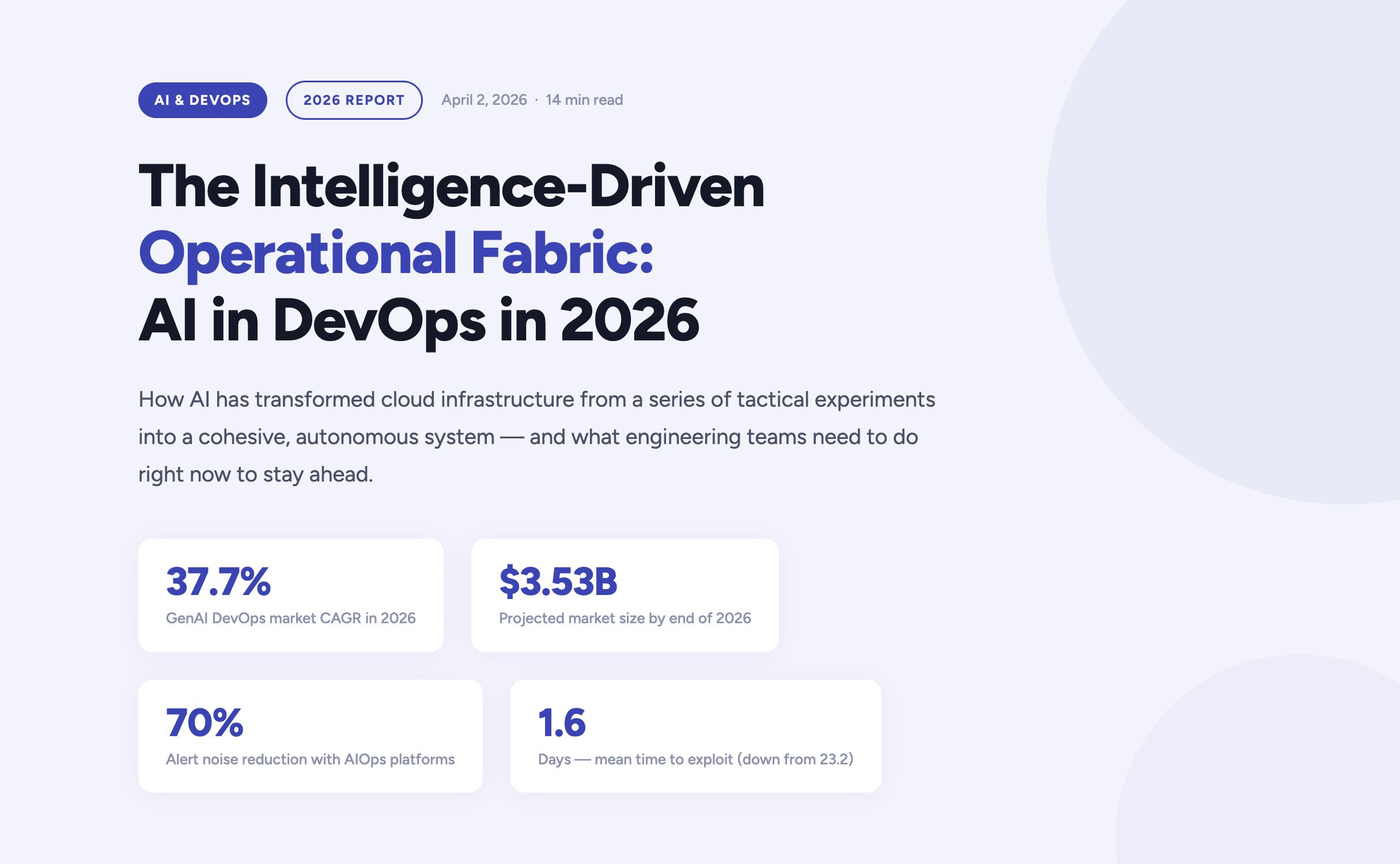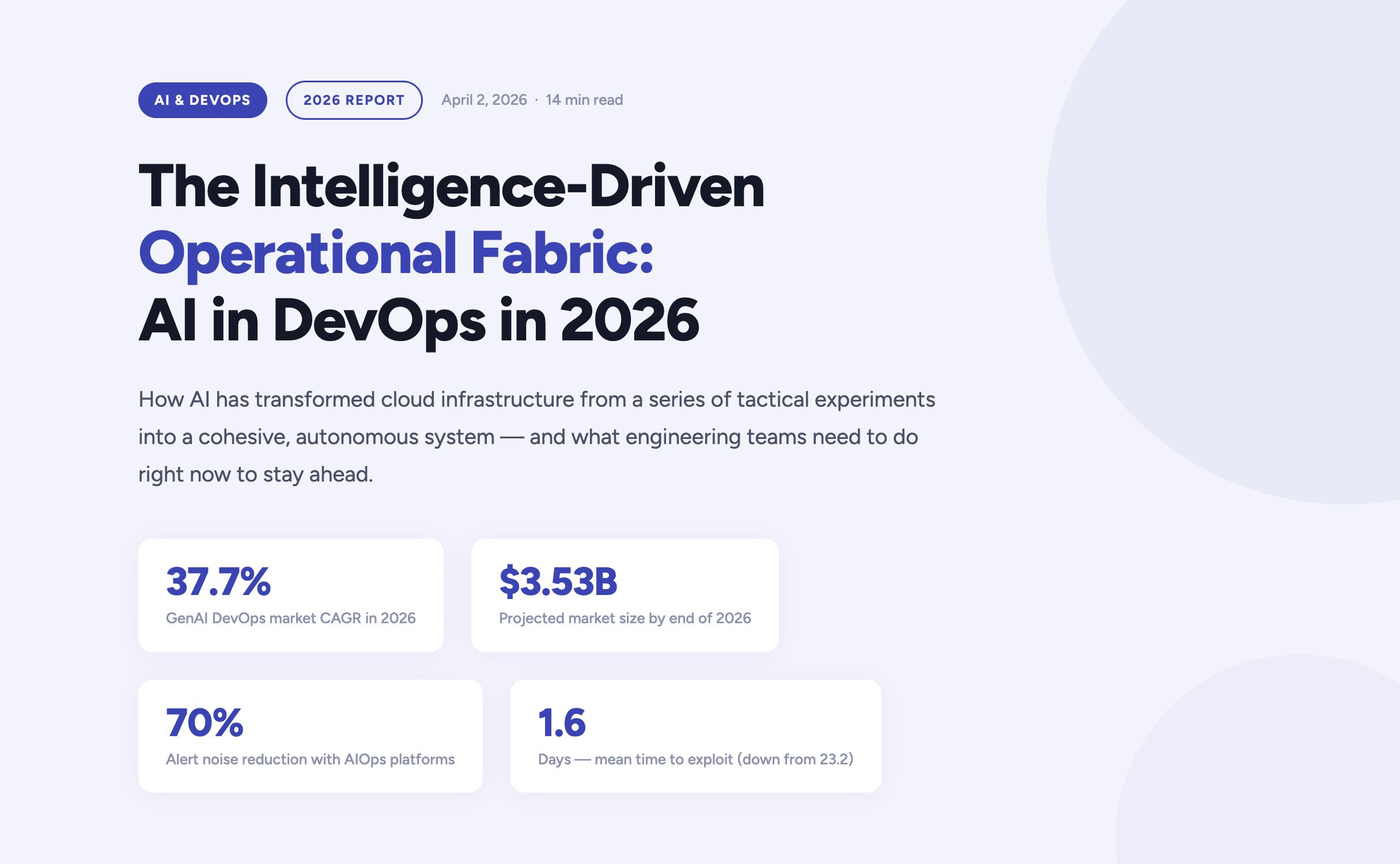
The year 2026 marks a definitive turning point in how enterprises build, deploy, and operate software. Artificial Intelligence has moved far beyond the experimental phase inside DevOps pipelines — it now forms the connective tissue of the entire software delivery lifecycle. According to current market analysis, the generative AI segment of the DevOps market is growing at a compound annual rate of 37.7%, expected to reach $3.53 billion by the end of this year alone.
For engineering teams, platform engineers, and CTOs navigating this shift, the questions are no longer "should we adopt AI?" but rather "how do we govern it?", "where does it amplify our strengths?", and critically — "where does it expose our weaknesses?". This article answers those questions, grounded in the realities of operating cloud infrastructure in 2026.
https://youtu.be/4FNyMRmHdTM?si=F2yOv89QU9gQ7Hif
The AI velocity paradox — why more code isn't always better
One of the most striking findings in the 2026 DevOps landscape is what researchers have begun calling the AI Velocity Paradox. AI-assisted coding tools have dramatically accelerated the code creation phase of the Software Development Life Cycle. However, the downstream delivery systems responsible for testing, securing, and deploying that code have often failed to keep pace — creating a structural mismatch between production and operations capacity.
The data tells a clear story. Teams that use AI coding tools daily are three times more likely to deploy frequently — but they also report significantly higher rates of quality failures, security incidents, and engineer burnout.
The AI DevOps maturity gap — occasional vs. daily AI tool users
The AI DevOps Maturity Gap — 2026 Analysis
Performance Indicator
Occasional AI Usage
Daily AI Usage
Daily deployment frequency
15% of teams
45% of teams
Frequent deployment issues
Minimal
69% of teams
Mean Time to Recovery (MTTR)
6.3 hours
7.6 hours
Quality / security problems
Baseline
51% quality / 53% security
Engineers working overtime
66%
96%
The root cause is structural: a "six-lane highway" of AI-accelerated code generation is funneling into a "two-lane bridge" of operational capacity. Engineers spend an average of 36% of their time on repetitive manual tasks — chasing tickets, rerunning failed jobs, manually validating AI-generated code — while developer burnout now affects 47% of the engineering workforce.
The implication is clear: AI does not automatically improve DevOps outcomes. Applied to brittle pipelines or fragmented telemetry, it accelerates instability. Applied to robust, standardized foundations, it becomes a force multiplier. The organizations that succeed in 2026 are those that modernize their entire delivery system — not just the IDE.
Tech should do more than work — it should do good, and it should scale purposefully."
Fedir Kompaniiets, CEO, Gart Solutions
Intent-to-Infrastructure — the evolution of IaC
Infrastructure as Code has been a DevOps cornerstone for years, but the model is undergoing a fundamental transformation in 2026. The industry is moving away from hand-crafted Terraform scripts and declarative state management toward what practitioners call Intent-to-Infrastructure — AI-powered platforms that interpret high-level business requirements and autonomously provision compliant, cost-optimized environments.
The evolution of Infrastructure as Code
The Evolution of Infrastructure as Code
Generation
Primary Mechanism
Governance Model
Outcome Focus
IaC 1.0 — Legacy
Manual scripting (Terraform, Ansible)
Periodic manual audits
Resource provisioning
IaC 2.0 — Standard
Declarative state management
Automated policy checks
Environment consistency
Intent-Driven (2026)
AI translation of requirements
Continuous autonomous reconciliation
Business-aligned outcomes
In the intent-driven model, a developer can express a requirement in plain language — for example, "provision a production-ready Kubernetes cluster with SOC 2-compliant networking for our EU-West workload" — and the platform autonomously generates, validates, and manages the resources. Compliance is no longer a retrospective audit exercise; it is embedded at the moment of generation.
This approach directly addresses one of the most persistent gaps in enterprise cloud governance: the Confidence Gap. While 77% of organizations report confidence in their AI-generated infrastructure, only 39% maintain the fully automated audit trails needed to actually verify those outputs. Intent-driven platforms close this gap by creating immutable, traceable records of every provisioning decision.
Key IaC Capabilities in 2026
Natural language provisioning — Describe infrastructure requirements in plain English, receiving validated, compliant Terraform or Pulumi code.
Golden path enforcement — Pre-approved patterns ensure every environment is secure by default, reducing misconfiguration risk.
Continuous autonomous reconciliation — AI continuously monitors for drift and self-corrects without human intervention.
Policy-as-code integration — OPA, Sentinel, and custom guardrails are embedded into generation pipelines, not added as an afterthought.
Cost-aware provisioning — FinOps constraints are applied at generation time, preventing over-provisioning before it happens.
AIOps and the new era of observability
As cloud-native architectures scale in complexity, the challenge facing modern platform engineers is no longer the collection of telemetry data — it is the meaningful interpretation of it. According to Gartner, over 60% of production incidents in 2026 are caused by poor interpretation of existing data, not a lack of visibility. Teams are drowning in signals while missing the meaning.
This has driven the rapid maturation of AIOps — Artificial Intelligence for IT Operations — which shifts the operational model from reactive incident firefighting to predictive, self-healing systems. Modern AIOps platforms in 2026 are built on three core capabilities:
Predictive incident management
AI models trained on historical delivery patterns, change velocity data, and error logs can now surface probabilistic risk assessments hours before a service outage occurs. Rather than reacting to pages at 3am, platform teams receive prioritized warnings during business hours with recommended remediation paths.
Autonomous remediation
For well-understood failure patterns — pod OOMKill events, connection pool exhaustion, SSL certificate expiry — AI agents can execute validated runbooks autonomously, patching or scaling systems within seconds of detection. Human intervention is reserved for novel or high-impact scenarios.
Intelligent alert prioritization
By correlating weak signals across application, infrastructure, and network layers, modern AIOps platforms reduce alert noise by up to 70%. Engineers no longer triage a wall of Slack notifications — they engage with a curated, context-rich incident queue.
60%+
Incidents from misinterpretation
70%
Less alert noise via AIOps
36%
Engineer time lost to manual tasks
eBPF
Deep visibility sans code changes
DevSecOps 2.0 — when autonomous security becomes non-negotiable
The security landscape of 2026 is unforgiving. The mean time to exploit a known vulnerability has collapsed from 23.2 days in 2025 to just 1.6 days — faster than any human-speed security process can respond. This has driven a fundamental rearchitecting of DevSecOps, from a set of "shift left" practices to a fully autonomous, self-healing security model.
Traditional vs. AI-Enhanced DevSecOps
Security Metric
Traditional DevSecOps
AI-Enhanced DevSecOps (2026)
Vulnerability identification
Periodic scanning of dependencies
Real-time scanning of code, containers, and runtimes
Threat response
Manual triage and incident response
Automated isolation of compromised resources
Compliance evidence
Manual spreadsheet collection
Automated, immutable audit trails
Risk assessment
Static CVSS vulnerability scoring
Contextual scoring based on reachability and blast radius
For regulated industries — healthcare, financial services, legal — compliance is no longer a quarterly exercise. In 2026, the most resilient organizations implement Compliance-by-Design infrastructure, where HIPAA, HITECH, SOC 2, and PCI-DSS controls are embedded directly into DevOps pipelines. Every commit, every deployment, every configuration change produces a verifiable, immutable compliance artifact — not as overhead, but as a natural byproduct of the engineering workflow.
The shift is cultural as well as technical: compliance is now understood as a growth enabler, not a hindrance. Organizations that can demonstrate real-time security posture attract enterprise customers, pass procurement audits, and move faster through regulated markets.
FinOps and the economics of intelligent infrastructure
Cloud spending has become a top-five P&L line item for most mid-to-large enterprises in 2026. Uncontrolled SaaS sprawl, over-provisioned Kubernetes clusters, and idle development environments have made AI-driven FinOps not just a cost-optimization strategy, but a boardroom-level priority.
The latest generation of FinOps tooling applies AI in two directions: reactive optimization (identifying and eliminating waste in existing infrastructure) and proactive cost governance (embedding unit cost constraints into provisioning workflows before resources are ever created). The results are significant — in some cases, organizations achieve savings of up to 80% on AWS compute budgets through spot instance migration, rightsizing, and automated idle resource termination.
Increasingly, FinOps and sustainability are being treated as two sides of the same coin. By eliminating idle compute and over-provisioned infrastructure, organizations simultaneously reduce cloud spend and digital carbon footprint — what practitioners are calling Green FinOps. At Gart Solutions, 70% of client workloads are optimized to run on green cloud platforms as part of a carbon-neutral-by-default infrastructure strategy.
"Applied to brittle pipelines or fragmented telemetry, AI accelerates instability. Applied to robust, standardized foundations, it becomes the force multiplier that allows organizations to scale resilience at the speed of code."
Roman Burdiuzha, CTO, Gart Solutions
Human-on-the-Loop governance — the new control model
As AI agents take over increasing portions of the operational layer, one of the defining debates of 2026 is where to draw the line on autonomy. The industry consensus has moved away from both extremes — fully manual "Human-in-the-Loop" (HITL) processes that create bottlenecks, and fully autonomous systems that introduce unacceptable risk — toward a middle path: Human-on-the-Loop (HOTL) governance.
In the HOTL model, AI agents operate autonomously within predefined guardrails. Humans shift from being operators to being overseers — setting policies, reviewing exceptions, and vetoing high-stakes decisions. The architecture is built on four pillars:
Step and cost thresholds — Hard limits on the number of actions an agent can execute per session, or the total tokens consumed, prevent infinite loops and runaway infrastructure costs.
The Veto Protocol — For high-risk decisions (budget reallocations, production changes above a defined blast radius), the agent surfaces a structured "Decision Summary" for asynchronous human review before proceeding.
Identity and access control — Agents are granted short-lived, task-scoped credentials. They never hold standing access to production environments; every session is authenticated, logged, and time-bounded.
Immutable audit trails — Every agent action generates a cryptographically signed record, ensuring full traceability for compliance and post-incident review.
This governance model is not a limitation on AI capability — it is what makes AI capability trustworthy enough to deploy at scale in regulated, high-stakes environments.
Industry-specific transformations
Manufacturing — the intelligent shop floor
Manufacturing organizations face a persistent challenge: deeply siloed data environments where Management Execution Systems (MES), ERP platforms, IoT sensor networks, and POS systems rarely communicate in real time. In 2026, cloud-native, AI-powered integration layers are dissolving these silos — enabling predictive maintenance, real-time production analytics, and supply chain transparency from raw material to finished product.
For one manufacturing client, a custom Green FinOps strategy eliminated over-provisioned infrastructure while a blockchain-based supply chain integration created end-to-end product traceability. The combined impact: measurable cost savings, improved regulatory compliance, and a more resilient operational model.
Healthcare — securing the patient data journey
In healthcare, the stakes of a misconfigured infrastructure are clinical as well as financial. DevOps practices in this sector are purpose-built around securing electronic health records, ensuring FDA and HIPAA compliance, and protecting medical device software against zero-day vulnerabilities. AI-driven monitoring continuously scans for "blind spots" that could lead to clinical data loss — not just at deployment time, but across the full runtime lifecycle.
SaaS and fintech — scaling without headcount sprawl
SaaS companies and fintech startups are increasingly turning to DevOps-as-a-Service to manage global availability and rapid iteration cycles without proportional growth in engineering headcount. By embedding automated security tasks, infrastructure-as-code provisioning, and AI-driven observability into every deployment, these teams can scale their products while maintaining the operational quality standards that enterprise customers demand.
Build your intelligent operational fabric
Partner with Gart Solutions for resilient, AI-powered cloud infrastructure.
Talk to an engineer →
Your 2026 AI DevOps roadmap
Organizations that are successfully navigating the AI transition in 2026 share a common pattern. They did not bolt AI onto existing processes — they built the foundations first, then amplified them. The roadmap has four distinct stages:
Data readiness audit
Ensure that observability data — logs, metrics, traces, events — is clean, normalized, and accessible across organizational silos. AI models are only as good as the telemetry they consume. Fragmented, noisy data produces fragmented, unreliable AI recommendations.
High-ROI use case selection
Start with workflows where AI delivers measurable, auditable value — automated testing, incident triage, IaC generation, cost anomaly detection. Build confidence and governance muscle before expanding to higher-risk autonomous operations.
Governance architecture
Establish the guardrails — HOTL oversight protocols, agent identity controls, immutable audit trails, cost thresholds — before deploying autonomous agents into production environments. Governance is not friction; it is what makes speed sustainable.
AI fluency across the engineering organization
Develop the skills required to oversee, interact with, and continuously improve intelligent agents. The competitive advantage in 2027 will belong to teams that can govern AI effectively — not just deploy it.
The 2026 AI-native DevOps toolchain
The toolchain of 2026 is defined by intelligence at every stage of the delivery pipeline. Unlike earlier generations of tooling that added AI as an afterthought, these platforms are AI-native — built from the ground up to learn, adapt, and act autonomously.
The AI DevOps Tooling Landscape (2026)
Tool
Domain
Key AI Capability
Snyk
Security
Real-time AI scanning for dependencies, containers, and IaC
Spacelift
Infrastructure
Multi-tool IaC management with AI policy enforcement
Harness
CI/CD
Intelligent software delivery with autonomous deployment verification
Datadog
Monitoring
AI-augmented full-stack visibility, anomaly detection, log correlation
PagerDuty
Incident Management
ML-based event correlation and intelligent noise reduction
StackGen
Platform Eng.
AI-powered intent-to-infrastructure generation
K8sGPT
Kubernetes
Natural language explanation and diagnosis of cluster errors
Sysdig Sage
DevSecOps
AI analyst for runtime security threat detection and CNAPP
Cast AI
FinOps
Autonomous Kubernetes cost optimization and rightsizing
Conclusion — from manual doers to intelligent orchestrators
The convergence of AI and DevOps in 2026 has redefined what is possible in software delivery. The organizations that thrive are not those that deploy the most AI tools — they are those that build the most resilient foundations and then amplify those foundations intelligently. Cloud infrastructure is no longer a hosting environment. It is an intelligent fabric that predicts, learns, and self-heals.
The transition is as cultural as it is technical. Engineering teams are moving from being manual operators to being intelligent orchestrators — governing not through a queue of tickets, but through the strategic definition of intent and the rigorous enforcement of outcomes. For those willing to make this shift, the competitive advantage is significant, durable, and compounding.
As Gart Solutions has built its entire practice around: tech should do more than work — it should do good, and it should scale purposefully.
Build your intelligent operational fabric with us
A boutique DevOps and cloud infrastructure partner for engineering teams that want to scale reliably, securely, and sustainably — without the overhead of a hyperscaler.
DevOps as a Service
Full-lifecycle CI/CD design, automation, and platform engineering for teams that need reliable, battle-tested delivery pipelines at startup speed.
Cloud migration & adoption
Strategic migration from on-premise or legacy cloud environments to modern, cost-optimized, and green cloud architectures on AWS, GCP, or Azure.
DevSecOps automation
Compliance-by-design infrastructure for regulated industries — embedding HIPAA, SOC 2, and PCI-DSS controls directly into your delivery pipeline.
AIOps & observability
End-to-end observability strategy — from eBPF telemetry and distributed tracing to AI-powered alerting, anomaly detection, and autonomous runbook execution.
FinOps & cloud cost optimization
Cloud cost audits, spot instance migration, idle resource termination, and Kubernetes rightsizing — achieving savings of up to 80% on cloud budgets.
Managed infrastructure
24/7 proactive management of your cloud infrastructure, with SLA-backed uptime guarantees, automated scaling, and continuous compliance monitoring.

Why the DevOps vs DevSecOps debate still matters?
Software engineering has entered an era where speed without security is no longer merely inefficient—it is existentially risky. As organizations accelerate release cycles using automation, cloud platforms, and AI-assisted development, the traditional boundaries between building, running, and securing software have collapsed.
DevOps solved one historical problem: the friction between development and operations.DevSecOps emerged to solve the next one: security debt created by speed itself.
In 2026, the distinction between DevOps and DevSecOps is not academic. It determines whether organizations can safely scale AI-generated code, survive automated attacks, meet regulatory obligations, and maintain trust in systems that now evolve faster than humans can manually inspect.
This article explores DevOps and DevSecOps not as competing models, but as successive architectural responses to systemic failures in software delivery—culminating in a security-embedded operating model designed for autonomous, AI-augmented systems.
The Historical Failure of Sequential Development
Waterfall and the Cost of Late Discovery
For decades, software was built using the Waterfall model, a linear sequence of requirements, design, implementation, testing, and deployment. While administratively neat, it assumed that:
requirements would remain stable,
risks could be fully anticipated upfront,
and defects discovered late were acceptable.
In reality, Waterfall created compounding risk. Defects found during testing or production were exponentially more expensive to fix, and security flaws often surfaced only after systems were already exposed.
More critically, Waterfall institutionalized organizational silos:
Developers optimized for feature delivery.
Operations optimized for uptime and stability.
Security was external, reactive, and often adversarial.
This misalignment made rapid adaptation nearly impossible.
DevOps: Optimizing for Flow and Stability
The Birth of DevOps
DevOps emerged in the late 2000s as a response to these failures. Sparked by Patrick Debois and popularized through early success stories like Flickr’s “10+ deploys per day,” DevOps reframed software delivery as a continuous, collaborative system rather than a sequence of handoffs.
The goal was not just faster releases, but predictable, repeatable, low-risk change.
The CAMS Model: DevOps as a System, Not a Toolchain
DevOps is best understood through the CAMS framework:
Culture: Shared ownership across development, operations, and management
Automation: CI/CD pipelines, infrastructure provisioning, and repeatable processes
Measurement: Metrics-driven feedback loops (later formalized as DORA metrics)
Sharing: Transparent communication of failures, learnings, and outcomes
By 2025, DevOps had become the industry default, with adoption nearing 85%.
But success created a new problem.
The Security Debt of High-Velocity Delivery
When Speed Outpaces Control
DevOps dramatically reduced deployment friction—but security practices largely remained unchanged:
Threat modeling happened late or not at all.
Vulnerability scanning was a gate, not a guide.
Security teams reviewed releases after code was written.
This created what many organizations experienced as security debt:
vulnerabilities accumulated silently,
open-source dependencies expanded attack surfaces,
cloud misconfigurations became the leading cause of breaches.
In regulated industries—finance, healthcare, government—this model simply did not scale.
DevSecOps: Security as a First-Class System Property
The Core Difference: Timing and Ownership
The fundamental difference between DevOps and DevSecOps is not tooling—it is when and by whom security is handled.
DimensionDevOpsDevSecOpsPrimary GoalSpeed and reliabilitySpeed with verifiable securitySecurity RoleExternal or late-stageBuilt-in, shared responsibilityRisk FocusDowntime and failuresVulnerabilities, compliance, exposureAutomationBuild & deploySecurity, compliance, governance as code
DevSecOps does not slow DevOps down.It restructures it so security moves at the same velocity as code.
“Shift Left”: The Operating Mechanism of DevSecOps
Why Early Security Changes Everything
The strategic engine of DevSecOps is Shift Left—moving security controls as close as possible to the point where code is written.
In practice, this means:
security feedback inside the IDE,
pre-commit scans for secrets and vulnerable dependencies,
automated threat modeling during design,
policy enforcement before infrastructure is provisioned.
Fixing a vulnerability during coding can be up to 90% cheaper than fixing it in production. Mature DevSecOps teams consistently demonstrate:
faster remediation,
lower incident rates,
higher deployment frequency.
Security becomes an accelerator, not a brake.
The DevSecOps Toolchain: Defense in Depth, Automated
In a mature DevSecOps environment, security is not delivered through a single tool or control point. It emerges from a layered, automated system designed to surface risk as early as possible and respond to it continuously as software moves from idea to production. This approach—often described as defense in depth—ensures that no single failure, missed scan, or human oversight can expose the entire system.
Application security testing forms the foundation of this layered model. Static analysis tools examine source code and build artifacts before they ever run, identifying insecure patterns, missing input validation, and unsafe logic at the moment developers are still actively working on the code. Dynamic testing complements this by evaluating applications while they are running, revealing vulnerabilities that only appear in real execution contexts, such as authentication flaws, injection paths, or broken access controls. Together, these techniques close the gap between theoretical weakness and real-world exploitability.
Application Security Testing (AST)
SAST: Finds insecure code patterns before execution
DAST: Tests running applications for real-world exploitability
SCA: Secures open-source and third-party dependencies
IAST: Correlates runtime behavior with source code
RASP: Protects applications in production
As modern software increasingly depends on open-source and third-party components, software composition analysis has become just as critical as scanning proprietary code. Dependency trees now represent a significant portion of the attack surface, and vulnerabilities introduced indirectly can be just as damaging as those written in-house. By automatically evaluating dependencies against known vulnerability databases during builds and tests, DevSecOps pipelines protect the software supply chain without requiring developers to manually audit every library they use.
More advanced teams introduce interactive and runtime protection mechanisms to reduce noise and increase precision. By observing how code behaves during functional testing, interactive testing technologies can directly map untrusted inputs to vulnerable execution paths, dramatically reducing false positives. Runtime protection extends this visibility into production environments, where applications can actively block exploit attempts in real time, providing a last line of defense against zero-day attacks or previously unknown attack vectors.
Beyond application code, the DevSecOps toolchain expands into infrastructure and operational security. Secrets management systems prevent credentials, API keys, and tokens from being hardcoded or leaked into version control. Infrastructure-as-code scanners evaluate cloud templates and configuration files before deployment, catching misconfigurations such as overly permissive access policies or unencrypted storage—issues that remain one of the leading causes of cloud breaches.
Beyond Applications
Secrets management prevents credential leaks
IaC scanning detects cloud misconfigurations early
Diff-aware scanning preserves pipeline speed
The goal is not maximal scanning—it is precise, contextual, automated control.
What differentiates high-performing DevSecOps pipelines from slower, tool-heavy implementations is selectivity. Rather than scanning everything all the time, modern systems are diff-aware, focusing security analysis only on what has changed. This preserves fast feedback loops and prevents security tooling from becoming a bottleneck. Developers receive relevant, contextual feedback tied directly to their changes, which makes security actionable instead of disruptive.
Taken together, this automated, layered toolchain transforms security from a single gate at the end of delivery into a continuous capability embedded throughout the lifecycle. Each layer compensates for the limitations of the others, creating a resilient system where speed and protection reinforce each other rather than compete. In practice, this is where DevSecOps delivers its greatest value—not by adding more tools, but by orchestrating them into a coherent, automated defense that moves at the same pace as modern software development.
Infrastructure and Policy as Code: Governance Without Friction
As infrastructure moved to the cloud, manual configuration became a liability.
DevSecOps extends automation to governance itself:
Infrastructure as Code (IaC) ensures consistency and auditability
Policy as Code (PaC) enforces rules automatically using engines like Open Policy Agent (OPA)
Examples:
Preventing unencrypted storage before deployment
Blocking insecure Kubernetes manifests at admission time
Generating audit evidence automatically for SOC 2, HIPAA, or GDPR
This creates guardrails, not gates—allowing teams to move fast safely.
Culture: From Security Gatekeepers to Shared Ownership
Tools alone do not create DevSecOps. DevSecOps succeeds or fails less on tooling than on culture. In traditional organizations, security teams often operated as external reviewers, stepping in late to approve or reject releases. This positioning made security a perceived obstacle to delivery and reinforced adversarial dynamics between teams focused on speed and those focused on risk reduction.
DevSecOps replaces this model with shared ownership. Security is no longer something “handed off” to specialists but a responsibility distributed across development, operations, and security professionals. Developers are empowered to make secure decisions as they write code, operations teams enforce resilient environments, and security teams act as enablers who design guardrails rather than gates.
The cultural shift is from security as enforcement to security as collaboration:
Developers own security outcomes
Security teams enable, not block
Operations enforce reliability and containment
In practice, this shift requires meeting engineers where they work. Security feedback must appear in the same tools developers already use—IDEs, pull requests, and issue trackers—rather than in separate reports or audits. As trust grows, security specialists increasingly collaborate directly with product teams, helping shape design decisions early instead of policing them later.
Successful organizations scale this through:
Security champions inside engineering teams
Pairing and embedding security engineers
Threat modeling workshops and gamification
Integrating security into existing workflows
Maturity is measured not by zero vulnerabilities, but by how fast teams learn and respond.
Measuring DevSecOps: Speed and Risk Signals
Traditional DevOps metrics, like deployment frequency, lead time, and change failure rate, remain important indicators of agility. But they don’t capture the full picture in a security-first environment.
DevSecOps expands the lens to include risk signals that reflect how effectively teams prevent, detect, and remediate vulnerabilities. Key measures include how quickly newly discovered flaws are addressed, how long critical issues linger in the system, and how many high-severity vulnerabilities reach production. By combining velocity with these security indicators, organizations can evaluate whether their fast-moving pipelines also maintain a strong risk posture.
DevSecOps extends classic DORA metrics with security indicators:
Vulnerability discovery rate
Mean time to remediate (MTTR)
Mean vulnerability age
Critical issues reaching production
Data from 2025 shows that mature DevSecOps organizations resolve vulnerabilities over ten times faster than less mature peers, while simultaneously increasing deployment frequency by up to 150 percent. This demonstrates a crucial point: when automated correctly, speed and security reinforce each other rather than compete, turning DevSecOps into a true accelerator for both innovation and resilience.
AI Changes Everything — and Exposes Everything
By 2025, 90% of developers used AI daily.The DORA report confirms a hard truth:
AI does not fix broken systems — it amplifies them.
High-maturity teams get faster and safer.Low-maturity teams accumulate debt at machine speed.
The key lesson is clear: AI is a force multiplier. In capable environments, it drives innovation safely. In fragile environments, it magnifies vulnerabilities and exposes weaknesses faster than human teams can respond. The challenge for 2026 and beyond is not whether AI will be used—it’s whether organizations have the culture, tooling, and guardrails in place to ensure that speed doesn’t come at the cost of security. In other words, AI changes everything, but without DevSecOps, it also exposes everything.
Vibe Coding, Agentic AI, and the New Security Gap
As we move into 2026, a new paradigm is reshaping software development: vibe coding. Developers now act as “conductors,” giving natural language prompts to AI systems that generate entire modules or applications. This accelerates prototyping at unprecedented speeds but introduces a hidden cost: security debt baked into AI-generated code.
By 2026:
Up to 42% of code is AI-generated
Nearly 25% of that code contains security flaws
Developers increasingly do not fully trust what they ship
New risks emerge:
hallucinated authentication bypasses,
phantom dependencies,
silent removal of security controls,
AI-driven polymorphic attacks.
Compounding the challenge, adversaries are also leveraging agentic AI to launch adaptive attacks, creating a dynamic, real-time contest between offensive and defensive systems. In this environment, DevSecOps is no longer optional—it is the framework that allows organizations to integrate security into AI-assisted development, detect flawed code before it reaches production, and maintain trust even as machines take a more active role in creating software.
Security is no longer human-versus-human.It is machine-versus-machine.
DevSecOps in the Agentic Era
In the era of agentic AI, DevSecOps evolves from a pipeline strategy into a continuous, autonomous capability. Security can no longer be a manual checkpoint or a final review—AI-driven development moves too fast, and attackers are already leveraging machine intelligence to probe vulnerabilities in real time.
The future DevSecOps model includes:
autonomous vulnerability detection,
AI-generated remediation PRs,
automated validation pipelines,
strict human-in-the-loop controls for high-impact logic.
Frameworks like NIST SSDF, OWASP SAMM, SLSA provide structure, but success depends on platform engineering that embeds security invisibly into developer experience.
Conclusion: DevSecOps Is Not Optional Anymore
DevOps made software fast.DevSecOps makes it trustworthy at speed.
In an era of:
AI-generated code,
autonomous attackers,
continuous compliance,
and expanding attack surfaces,
security can no longer be a phase, a team, or a checklist.
DevSecOps is the operating system for modern software delivery.
Organizations that adopt it as a cultural, architectural, and automated system will not just ship faster—they will survive the next decade of software evolution.

In recent times, there has been a growing urgency regarding the security concerns of the developed software. Integrating secure development practices into the current processes has become imperative.
This is where DevSecOps comes into play—a powerful methodology that seamlessly integrates security practices into the software development process. In this article, we will explore the world of DevSecOps tools and how they play a pivotal role in enhancing software security, enabling organizations to stay one step ahead of potential threats.
[lwptoc]
Understanding DevSecOps Tools
DevSecOps tools are software applications and utilities designed to integrate security practices into the DevOps (Development and Operations) workflow. These tools aim to automate security checks, improve code quality, and ensure that security measures are an integral part of the software development process.
Some popular DevSecOps tools include:
Continuous Integration (CI) tools for security testing
Continuous Integration (CI) tools play a vital role in automating security testing throughout the development pipeline. They enable developers to regularly test code changes for vulnerabilities and weaknesses, ensuring that security is integrated into every stage of development.
Continuous Deployment (CD) tools for secure deployment
Continuous Deployment (CD) tools facilitate the secure and automated release of software into production environments. By leveraging CD tools, organizations can ensure that security measures are applied consistently during the deployment process.
? Read more: Exploring the Best CI/CD Tools for Streamlined Software Delivery
Security Information and Event Management (SIEM) tools for monitoring and incident response
SIEM tools help organizations monitor and analyze security events across their infrastructure. By providing real-time insights and automated incident response capabilities, SIEM tools empower teams to swiftly detect and respond to potential security breaches.
Here is a list of SIEM (Security Information and Event Management) tools: Splunk, IBM QRadar, ArcSight (now part of Micro Focus), LogRhythm, Sumo Logic, AlienVault (now part of AT&T Cybersecurity), SolarWinds Security Event Manager, Graylog, McAfee Enterprise Security Manager (ESM), Rapid7 InsightIDR.
Static Application Security Testing (SAST) tools for code analysis
SAST tools analyze the source code of applications to identify security flaws, vulnerabilities, and compliance issues. Integrating SAST into the development workflow allows developers to proactively address security concerns during the coding phase.
Some examples of Static Application Security Testing (SAST) tools: Fortify Static Code Analyzer, Checkmarx, Veracode Static Analysis, SonarQube, WhiteSource Bolt, Synopsys Coverity, Kiuwan, WebInspect, AppScan Source, Codacy
Key Features of SAST Solutions:
Code Analysis: SAST solutions perform in-depth code analysis to identify security issues, such as SQL injection, cross-site scripting (XSS), and buffer overflows.
Early Detection: By integrating SAST into the development workflow, security issues can be identified and addressed during the coding phase, reducing the cost and effort required to fix vulnerabilities later in the development cycle.
Continuous Scanning: SAST solutions can be configured for continuous scanning, allowing developers to receive real-time feedback on security issues as code changes are made.
Integration with CI/CD Pipelines: SAST tools seamlessly integrate with Continuous Integration/Continuous Deployment (CI/CD) pipelines, ensuring security testing is an integral part of the software development process.
Compliance Checks: SAST solutions can help organizations adhere to industry-specific and regulatory security standards by identifying code that may violate compliance requirements.
False Positive Reduction: Modern SAST solutions employ advanced algorithms and heuristics to reduce false positives, providing developers with more accurate and actionable results.
Language Support: SAST solutions support a wide range of programming languages, enabling organizations to secure diverse application portfolios.
Remediation Guidance: SAST tools often provide guidance on how to remediate identified vulnerabilities, helping developers address security issues effectively.
Dynamic Application Security Testing (DAST) tools for web application scanning
DAST tools perform dynamic scans of web applications in real-time, simulating attacks to identify potential vulnerabilities. By testing applications from the outside, DAST tools offer a comprehensive view of security risks.
Here is a list of Dynamic Application Security Testing (DAST) tools: OWASP ZAP (Zed Attack Proxy), Burp Suite, Acunetix, Netsparker, WebInspect, Qualys Web Application Scanning (WAS), AppScan Standard, Trustwave App Scanner (formerly Cenzic Hailstorm), Rapid7 AppSpider, Tenable.io Web Application Scanning.
Key Features of DAST Solutions:
Web Application Scanning: DAST tools focus on web applications and assess their security from an external perspective by sending crafted requests and analyzing responses.
Real-World Simulation: DAST solutions mimic actual attack scenarios, including SQL injection, cross-site scripting (XSS), and other common security threats, to identify vulnerabilities.
Comprehensive Coverage: DAST solutions analyze the entire application, including dynamic content generated by the server, to detect security issues across different pages and functionalities.
Automation and Scalability: DAST tools can be automated to perform regular and extensive scans, making them suitable for large-scale web applications and continuous testing.
Out-of-Band Testing: DAST solutions can identify vulnerabilities not discoverable through traditional scanning, such as those found in non-standard HTTP methods or custom headers.
Reduced False Positives: Modern DAST tools employ advanced techniques to minimize false positives, providing developers with accurate and reliable security findings.
Integration with CI/CD Pipelines: DAST solutions can be seamlessly integrated into CI/CD pipelines, allowing security testing to be an integral part of the software development process.
Compliance Support: DAST tools help organizations meet industry standards and regulatory requirements by detecting security weaknesses that may lead to compliance violations.
Continuous Monitoring: Some DAST solutions offer continuous monitoring capabilities, enabling developers to receive real-time feedback on security issues as the application changes.
Interactive Application Security Testing (IAST) tools for real-time code analysis
IAST tools provide real-time security analysis by observing application execution. By combining dynamic and static analysis, IAST tools offer deeper insights into application security while minimizing false positives.
Here is a list of IAST (Interactive Application Security Testing) tools: Contrast Security, Hdiv Security, RIPS Technologies, Seeker by Synopsys, Waratek AppSecurity for Java, Quotium Seeker, ShiftLeft, WhiteHat Security Sentinel IAST, AppSecTest by Pradeo, IriusRisk IAST.
Key Features of IAST Solutions:
Real-Time Analysis: IAST tools continuously monitor applications in real-time as they execute, capturing data on code behavior and interactions with the system to detect security flaws.
Code-Level Visibility: IAST solutions provide detailed information about vulnerabilities, including the exact line of code responsible for the issue, helping developers pinpoint and fix problems with greater accuracy.
Low False Positives: IAST reduces false positives by directly observing application behavior, resulting in more precise identification of true security vulnerabilities.
Minimal Performance Impact: IAST operates with low overhead, ensuring that security testing does not significantly impact the application's performance during runtime.
Comprehensive Security Coverage: By analyzing code execution paths, IAST solutions identify a wide range of vulnerabilities, including those arising from data flow, configuration, and authentication.
Seamless Integration: IAST tools easily integrate into existing development and testing environments, supporting various programming languages and frameworks.
Continuous Security Monitoring: IAST solutions enable continuous monitoring of applications, offering ongoing security assessment throughout the development lifecycle.
DevSecOps Collaboration: IAST fosters collaboration between development, security, and operations teams by providing real-time insights accessible to all stakeholders.
Remediation Guidance: IAST solutions not only identify vulnerabilities but also offer actionable remediation guidance, streamlining the process of fixing security issues.
Compliance Support: IAST assists organizations in meeting regulatory requirements by providing accurate and detailed security assessments.
Runtime Application Self-Protection (RASP) tools for runtime security
RASP tools operate within the application runtime environment, actively monitoring for malicious behavior and automatically blocking potential threats. These tools provide an additional layer of protection to complement other security measures.
Here is a list of RASP (Runtime Application Self-Protection) tools: Sqreen, Contrast Security, Waratek AppSecurity for Java, StackRox, Veeam PN (Powered Network), Guardicore, Aqua Security, Datadog Security Monitoring, Wallarm, Arxan Application Protection.
Key Features of RASP Solutions:
Real-Time Protection: RASP tools actively monitor application behavior during runtime, detecting and blocking security threats as they occur in real-time.
Immediate Response: By residing within the application, RASP can take immediate action against threats without relying on external systems, ensuring faster response times.
Application-Centric Approach: RASP solutions focus on protecting the application itself, making them independent of external security configurations.
Automatic Policy Enforcement: RASP automatically enforces security policies based on the application's behavior, mitigating vulnerabilities and enforcing compliance.
Precise Attack Detection: RASP can identify and differentiate between legitimate application behavior and malicious activities, reducing false positives.
Low Performance Overhead: RASP operates with minimal impact on application performance, ensuring efficient security without compromising user experience.
Runtime Visibility: RASP solutions provide real-time insights into application security events, helping developers and security teams understand attack patterns and trends.
Adaptive Defense: RASP can dynamically adjust its protection strategies based on the evolving threat landscape, adapting to new attack vectors and tactics.
Application-Aware Security: RASP understands the unique context of the application, allowing it to tailor security responses to specific application vulnerabilities.
Continuous Protection: RASP continuously monitors the application, offering ongoing security coverage that extends throughout the application's lifecycle.
DevSecOps Integration: RASP seamlessly integrates into DevSecOps workflows, empowering developers with real-time security feedback and enabling collaboration between teams.
Compliance Support: RASP helps organizations meet regulatory requirements by providing active protection against security threats and potential data breaches.
DevSecOps Tools Table
CategoryDevSecOps ToolCI/CDJenkins, GitLab CI, Travis CI, CircleCISASTSonarQube, Veracode, Checkmarx, FortifyDASTOWASP Zap, Burp Suite, Acunetix, NetsparkerIASTContrast Security, RASPberryRASPSqreen, AppTrana, GuardicoreSIEMSplunk, IBM QRadar, ArcSight, LogRhythmContainer SecurityAqua Security, Sysdig, TwistlockSecurity OrchestrationDemisto, Phantom, ResilientAPI SecurityPostman, Swagger InspectorChaos EngineeringGremlin, Chaos Monkey, PumbaPolicy-as-a-CodeOpen Policy Agent (OPA), Rego, KyvernoThis table provides a selection of DevSecOps tools across different categories.
Empower your team with DevOps excellence! Streamline workflows, boost productivity, and fortify security. Let's shape the future of your software development together – inquire about our DevOps Consulting Services.