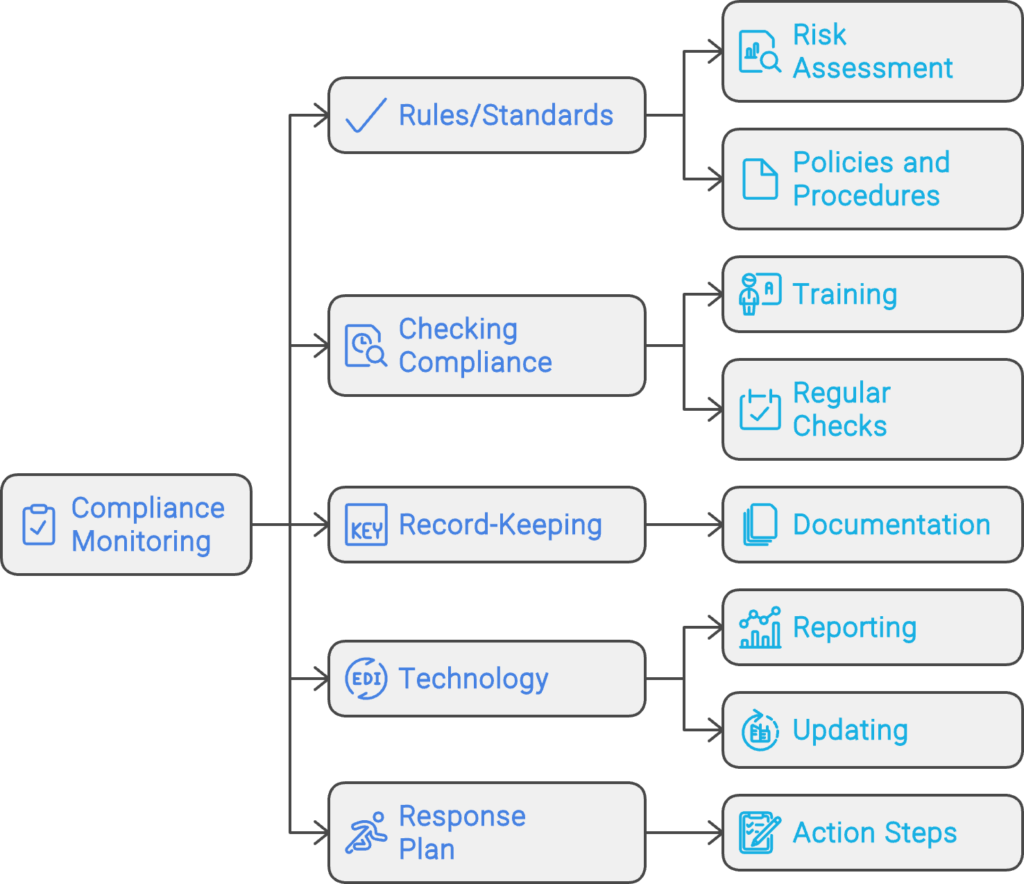
- What is Compliance Monitoring?
- Why Compliance Monitoring Matters in 2026
- Compliance Monitoring vs Compliance Audit vs Compliance Management
- The 7-Step Compliance Monitoring Process
- Key Controls & Evidence to Monitor
- Continuous Compliance Monitoring for Cloud Environments
- Industry-Specific Compliance Monitoring Frameworks
- What We Usually Find During Compliance Monitoring Reviews
- Compliance Monitoring Tools & Automation
- Compliance Monitoring Best Practices
- Compliance Monitoring Checklist for Cloud Teams
- How Gart Helps You Build a Continuous Compliance Monitoring Program
Compliance Monitoring is the ongoing process of verifying that an organization’s systems, processes, and people continuously adhere to regulatory requirements, internal policies, and industry standards — not just at audit time, but every day. For cloud-native and regulated businesses in 2026, it is the difference between a clean audit and a costly breach.
What is Compliance Monitoring?
Compliance monitoring is the systematic, continuous practice of evaluating whether an organization’s operations, systems, and people conform to the laws, regulations, and internal standards that govern them. Unlike a one-time audit, compliance monitoring runs as an always-on feedback loop — collecting evidence, flagging exceptions, and enabling rapid remediation before regulators ever knock on the door.
The practice is critical across heavily regulated industries:
- Healthcare — HIPAA, HITECH, 21 CFR Part 11
- Finance & Banking — PCI DSS, SOX, Basel III, MiFID II
- Cloud & SaaS — SOC 2, ISO 27001, CSA CCM
- EU-regulated entities — GDPR, NIS2, DORA
- Energy & Utilities — NERC CIP, ISO 50001
- Pharmaceuticals — GxP, FDA 21 CFR

💡 In short: Compliance monitoring is your organization’s immune system. Audits are the annual check-up. Monitoring is what keeps you healthy between check-ups.
Why Compliance Monitoring Matters in 2026
Regulatory landscapes have never moved faster. GDPR fines reached record highs in 2024–2025, NIS2 entered enforcement mode across the EU, and DORA (Digital Operational Resilience Act) took effect for financial entities. Meanwhile, cloud adoption has created entirely new attack surfaces that traditional point-in-time audits simply cannot cover.
| Risk Without Monitoring | Typical Business Impact | Probability (unmonitored) |
|---|---|---|
| Undetected misconfigured S3 bucket / cloud storage | Data breach, regulatory fine, brand damage | High |
| Stale privileged access not reviewed | Insider threat, audit failure, SOX violation | Very High |
| Missing audit log retention | Inability to prove compliance, automatic audit failure | High |
| Backup not tested | Unrecoverable data loss, SLA breach, recovery failure | Medium |
| Unpatched critical CVE beyond SLA | Exploitable vulnerability, CVSS breach, PCI non-compliance | High |
Strong compliance monitoring builds trust with enterprise clients and partners, significantly reduces audit preparation time, and enables a proactive risk posture instead of a reactive, fire-fighting one.
Compliance Monitoring vs Compliance Audit vs Compliance Management
These three terms are often used interchangeably but they describe distinct activities that work together. Understanding the difference helps organizations allocate resources correctly.
| Dimension | Compliance Monitoring | Compliance Audit | Compliance Management |
|---|---|---|---|
| Frequency | Continuous / near-real-time | Periodic (annual, quarterly) | Ongoing governance |
| Purpose | Detect & alert on deviations | Formal independent assessment | Policies, training, culture |
| Output | Alerts, dashboards, exception logs | Audit report, findings, attestation | Policies, procedures, risk register |
| Who leads | Engineering / Security / DevOps | Internal audit / Third-party auditor | Compliance Officer / GRC team |
| Analogy | Blood pressure cuff worn daily | Annual physical with doctor | Healthy lifestyle program |
✅ Monitoring answers
- Is MFA enforced right now?
- Are all logs being retained?
- Did anything change in IAM this week?
- Are backups completing successfully?
- Is encryption enabled on all storage?
📋 Auditing answers
- Were controls effective over the period?
- Did evidence satisfy the framework?
- What is the organization’s control maturity?
- What formal findings require remediation?
- Is the organization SOC 2 / ISO 27001 ready?
The 7-Step Compliance Monitoring Process
Effective compliance monitoring is not a single tool or dashboard — it’s a disciplined cycle. Here is the process Gart uses when setting up or maturing a client’s compliance monitoring program:
1. Define Scope & Applicable Frameworks
Identify which regulations, standards, and internal policies apply. Map your systems, data flows, and third-party integrations to determine the monitoring perimeter. Ambiguous scope is the most common reason monitoring programs fail.
2. Inventory Systems & Controls
Catalogue all assets (cloud, on-prem, SaaS, CI/CD pipelines) and map each one to a control objective. Assign control owners. Without ownership, no one acts when an exception fires.
3. Define Evidence Collection Rules
For each control, specify what constitutes “evidence of compliance” — a log entry, a configuration state, a test result, a screenshot, or a signed document. Define collection frequency (real-time, daily, monthly) and acceptable format for auditors.
4. Instrument & Automate Collection
Deploy monitoring agents, SIEM rules, cloud policy engines (AWS Config, Azure Policy, GCP Security Command Center), and IaC scanning tools. Automate evidence collection wherever possible — manual evidence gathering at audit time is a costly, error-prone anti-pattern.
5. Monitor Exceptions & Triage Alerts
Create alert thresholds for control deviations. Not every alert is a breach — build a triage process that separates noise from genuine risk. Route high-priority exceptions to security/engineering immediately; lower-priority items to a weekly review queue.
6. Prioritize Risks & Remediate
Score exceptions by likelihood and impact. Maintain a risk register that tracks open findings, owners, and target remediation dates. Escalate unresolved critical findings to leadership with a clear business-impact framing.
7. Re-test, Report & Continuously Improve
After remediation, re-test the control to confirm it is effective. Produce compliance health reports for leadership and auditors. Run a quarterly retrospective to tune alert thresholds and update monitoring scope as regulations and infrastructure evolve.
Key Controls & Evidence to Monitor
Across hundreds of compliance engagements, the controls below consistently appear on auditor checklists. These are the areas where automated compliance monitoring delivers the highest return:
| Control Area | What to Monitor | Evidence Auditors Want | Relevant Frameworks |
|---|---|---|---|
| Identity & Access (IAM) | Privileged role assignments, inactive accounts, MFA status, service account permissions | Access review logs, MFA adoption rate, least-privilege config exports | SOC 2, ISO 27001, HIPAA |
| Audit Logging | Log completeness, retention period, tamper-evidence, SIEM ingestion health | Log retention policy, SIEM dashboard, CloudTrail / Audit Log exports | PCI DSS, SOX, NIS2, GDPR |
| Encryption | Data-at-rest encryption on storage, TLS version on endpoints, key rotation schedules | Encryption config exports, key management audit logs, TLS scan reports | PCI DSS, HIPAA, GDPR, ISO 27001 |
| Patch Management | CVE scan results, SLA adherence per severity, open critical/high vulnerabilities | Scan reports, patch cadence logs, SLA compliance metrics | SOC 2, PCI DSS, ISO 27001 |
| Backup & Recovery | Backup job success rate, RPO/RTO test results, offsite replication status | Backup logs, recovery test records, DR test reports | SOC 2, ISO 22301, DORA, NIS2 |
| Vendor / Third-Party Access | Active vendor sessions, access scope, contract/NDA currency, SOC 2 report dates | Vendor access logs, contract register, third-party risk assessments | ISO 27001, SOC 2, GDPR, NIS2 |
| Network & Perimeter | Firewall rule changes, open ports, egress filtering, WAF alert volumes | Firewall config snapshots, IDS/IPS logs, pen test reports | PCI DSS, SOC 2, NIS2 |
| Incident Response | Mean time to detect (MTTD), mean time to respond (MTTR), breach notification timelines | Incident logs, CSIRT reports, post-mortems | GDPR (72h), NIS2, HIPAA, DORA |
Continuous Compliance Monitoring for Cloud Environments
Cloud infrastructure changes constantly — teams spin up resources, update IAM policies, and deploy code multiple times per day. This makes continuous compliance monitoring not a nice-to-have but a fundamental requirement. Manual checks against cloud state are obsolete before the ink dries.
AWS Compliance Monitoring — Key Automated Checks
- AWS Config Rules — detect non-compliant resources in real time (e.g., unencrypted EBS volumes, public S3 buckets, missing CloudTrail)
- AWS Security Hub — aggregates findings from GuardDuty, Inspector, Macie into a single compliance posture score
- CloudTrail + Athena — query audit logs for unauthorized IAM changes, API calls outside approved regions
- IAM Access Analyzer — surfaces external access to resources and unused roles/permissions
Azure Compliance Monitoring — Key Automated Checks
- Azure Policy & Defender for Cloud — enforce and score compliance against CIS, NIST SP 800-53, ISO 27001 benchmarks
- Microsoft Purview — data classification, governance, and audit trail across Azure and M365
- Azure Monitor + Sentinel — SIEM-class alerting on suspicious activity with compliance-relevant playbooks
- Privileged Identity Management (PIM) — just-in-time access with mandatory justification and approval workflows
GCP Compliance Monitoring — Key Automated Checks
- Security Command Center — organization-wide misconfiguration detection and compliance benchmarking
- VPC Service Controls — perimeter security policies that prevent data exfiltration
- Cloud Audit Logs — immutable, per-service activity and data access logs
- Policy Intelligence — recommends IAM role right-sizing based on actual usage data
For authoritative cloud security benchmarks, the CIS Benchmarks provide configuration baselines for AWS, Azure, GCP, Kubernetes, and 100+ other platforms — an industry-standard starting point for any cloud compliance monitoring program.
See Gart’s Cloud Computing & Security servicesIndustry-Specific Compliance Monitoring Frameworks
Compliance monitoring requirements differ significantly by industry and geography. Below are the frameworks Gart’s clients most commonly monitor against, along with the controls that require continuous (not just periodic) monitoring.
| Framework | Industry / Region | Key Continuous Monitoring Requirements | Resources |
|---|---|---|---|
| ISO 27001 | Global / All industries | Access control review, log management, vulnerability scanning, supplier review | ISO.org |
| SOC 2 Type II | SaaS / Technology | Continuous availability, logical access, change management, incident response | AICPA |
| HIPAA | Healthcare (US) | ePHI access logs, encryption at rest/transit, workforce activity audits | HHS.gov |
| PCI DSS v4.0 | Payment / E-commerce | Real-time network monitoring, file integrity monitoring, quarterly vulnerability scans | PCI SSC |
| NIS2 | EU / Critical sectors | Incident detection within 24h, risk assessments, supply chain security checks | ENISA |
| GDPR | EU / Global processing EU data | Data subject request tracking, breach detection (<72h notification), processor audits | GDPR.eu |
How to prepare for a HIPAA Audit – Gart’s PCI DSS Audit guide
What We Usually Find During Compliance Monitoring Reviews
After reviewing postures across dozens of regulated environments, these are the patterns we encounter repeatedly — regardless of organization size.
Incomplete or stale access reviews
Former employees and service accounts with active permissions weeks after departure. IAM hygiene is rarely automated, and reviews are often rubber-stamped.
Missing backup test evidence
Backups appear healthy, but nobody has tested a restore in 6–18 months. Auditors want dated restore test logs with RPO/RTO outcomes, not just success metrics.
Fragmented or incomplete audit logs
Gaps in the log chain (like disabled S3 data-event logging) make it impossible to reconstruct an incident or prove that one didn’t happen.
Alert fatigue masking real issues
Thousands of low-fidelity alerts lead teams to mute notifications or build exceptions, inadvertently disabling detection for real threats.
Policy-to-implementation gaps
Written policies say “encryption required,” but reality reveals unencrypted legacy buckets. Continuous monitoring is the only way to detect this drift.
Automation is first patched, last monitored
CI/CD pipelines move faster than human reviewers. IaC repositories often lack policy-as-code scanning, leaving non-compliant resources active for months.
Compliance Monitoring Tools & Automation
The right tooling depends on your stack, frameworks, and team maturity. Most organizations use a layered approach rather than a single platform:
| Category | Representative Tools | Best For |
|---|---|---|
| Cloud Security Posture Management (CSPM) | AWS Security Hub, Wiz, Prisma Cloud, Orca Security, Defender for Cloud | Cloud misconfiguration detection, continuous benchmarking |
| SIEM / Log Management | Splunk, Elastic SIEM, Microsoft Sentinel, Datadog Security | Log correlation, anomaly detection, audit evidence |
| GRC Platforms | Vanta, Drata, Secureframe, ServiceNow GRC, OneTrust | Evidence collection automation, audit-ready reporting |
| Policy-as-Code / IaC Scanning | Open Policy Agent (OPA), Checkov, Terrascan, tfsec, Conftest | Prevent non-compliant infrastructure from being deployed |
| Vulnerability Management | Tenable Nessus, Qualys, AWS Inspector, Trivy (containers) | CVE detection, patch SLA monitoring, container scanning |
| Identity Governance | SailPoint, CyberArk, Azure PIM, AWS IAM Access Analyzer | Access reviews, least-privilege enforcement, PAM |
⚠️ Tool sprawl is a compliance risk: More tools mean more integrations to maintain, more alert queues to manage, and more places where evidence can fall through the cracks. Start with native cloud tools and expand deliberately. The Linux Foundation and CNCF maintain open-source compliance tooling for cloud-native environments worth evaluating before adding commercial licenses.
Compliance Monitoring Best Practices
1. Shift compliance left into the development pipeline
The cheapest time to catch a compliance violation is before the resource is deployed. Integrate policy-as-code scanning (OPA, Checkov) into your CI/CD pipeline so that non-compliant Terraform or Helm charts never reach production. Treat compliance failures as build-breaking errors, not post-deploy recommendations.
2. Automate evidence collection — not just detection
Detection without evidence collection is useless at audit time. Configure your monitoring tools to export and archive compliance evidence (configuration snapshots, access review logs, scan reports) automatically to an immutable store. Auditors need evidence from a defined period — not a screenshot taken the morning of the audit.
3. Assign control owners, not just tool owners
Every control needs a named human owner who is accountable for exceptions. When an alert fires that MFA is disabled on a privileged account, “the security team” is not a sufficient owner — a specific person must be on call to investigate and remediate within the SLA.
4. Tune alerts ruthlessly to eliminate fatigue
Compliance monitoring programs that generate thousands of daily alerts quickly become ignored. Start with a small set of high-fidelity, high-impact alerts. Expand incrementally after each is tuned to near-zero false positive rates. A team that responds to 20 real alerts per day is more secure than one drowning in 2,000 noisy ones.
5. Monitor your monitoring
Monitoring pipelines break silently. Log shippers stop, API rate limits are hit, SIEM ingestion queues fill up. Build meta-monitoring to detect when evidence collection or alerting pipelines have gaps — and treat those gaps as compliance findings in their own right.
6. Conduct a quarterly compliance posture review
Beyond continuous automated monitoring, schedule a quarterly human review of the compliance posture. Review open exceptions, re-assess risk scores, retire obsolete controls, and update monitoring scope to cover new systems and regulatory changes.
Compliance Monitoring Checklist for Cloud Teams
A starting point for cloud-first compliance. Each item requires a named owner, a monitoring cadence, and a defined evidence artifact.
How Gart Helps You Build a Continuous Compliance Monitoring Program
We work with CTOs, CISOs, and engineering leaders to design, implement, and run compliance monitoring programs that hold up under real auditor scrutiny — not just on paper.
Scope & Framework Mapping
We identify applicable frameworks (ISO 27001, SOC 2, HIPAA, PCI DSS, NIS2, GDPR) and map your cloud infrastructure to each control objective.
Monitoring Setup & Automation
We deploy CSPM tools, SIEM rules, and policy-as-code pipelines — so evidence is collected automatically, not manually on audit day.
Gap Analysis & Risk Register
We deliver a clear view of your current compliance posture, prioritized by risk, with a remediation roadmap and accountable owners.
Ongoing Reviews & Readiness
Monthly exception reviews and pre-audit evidence packages — so you’re never scrambling the week before an official audit.
Audit-Ready Deliverables
Exception logs, risk matrices, and control evidence archives. Everything formatted for the specific framework you’re being audited against.