- ⚡ TL;DR — Quick Summary
- 20 Cloud Cost Optimization Traps
- Traps 1–4: Migration Strategy Mistakes That Set the Wrong Foundation
- Traps 5–9: Architectural Decisions That Create Structural Waste
- Traps 10–15: Operational Habits That Drain the Budget Silently
- Traps 16–20: Governance and FinOps Failures That Undermine Everything Else
- Cloud Cost Optimization Checklist for Engineering Leaders
- Cloud Cost Optimization Checklist
- Stop Guessing. Start Optimizing.
The 20 traps listed here are drawn from recurring patterns observed across cloud migration, architecture review, and cost optimization engagements led by Gart’s engineers. All provider-specific pricing references were verified against official AWS, Azure, and GCP documentation and FinOps Foundation guidance as of April 2026. This article was last substantially reviewed in April 2026.
Organizations moving infrastructure to the cloud often expect immediate cost savings. The reality is frequently more complicated. Without deliberate cloud cost optimization, cloud bills can grow faster than on-premises costs ever did — driven by dozens of hidden traps that are easy to fall into and surprisingly hard to detect once they compound.
At Gart Solutions, our cloud architects review spending patterns across AWS, Azure, and GCP environments every week. This article distills the 20 most damaging cloud cost optimization traps we encounter — organized into four cost-control layers — along with the signals that reveal them and the fastest fixes available.
Is cloud waste draining your budget right now? Our Infrastructure Audit identifies exactly where spend is leaking — typically within 5 business days. Most clients uncover 20–40% in recoverable cloud costs.
⚡ TL;DR — Quick Summary
- Migration traps (Traps 1–4): Lift-and-shift, wrong architecture, over-engineered enterprise tools, and poor capacity forecasting inflate costs from day one.
- Architecture traps (Traps 5–9): Data egress, vendor lock-in, over-provisioning, ignored discounts, and storage mismanagement create structural waste.
- Operations traps (Traps 10–15): Idle resources, licensing gaps, monitoring blind spots, and poor backup planning drain budgets silently.
- Governance & FinOps traps (Traps 16–20): Missing tagging, no cost policies, weak tooling, hidden fees, and undeveloped FinOps practices are the root cause behind most budget overruns.
- The biggest single lever: adopting a continuous FinOps operating cadence aligned to the FinOps Foundation framework.
20 Cloud Cost Optimization Traps
Use this table to quickly scan every trap and identify where your environment is most exposed before diving into the detailed breakdowns below.
| # | Trap | Why It Hurts | Typical Signal | Fastest Fix |
|---|---|---|---|---|
| 1 | Lift-and-Shift Migration | Pays cloud prices for on-prem design | High instance costs, poor utilization | Refactor high-cost workloads first |
| 2 | Wrong Architecture | Scalability failures → expensive rework | Manual scaling, outages at traffic peaks | Architecture review before migration |
| 3 | Overreliance on Enterprise Editions | Paying for features you don’t use | Enterprise licenses on dev/staging | Audit licenses by environment tier |
| 4 | Uncontrolled Capacity Planning | Over- or under-provisioned resources | Idle capacity OR repeated scaling crises | Demand-based autoscaling + monitoring |
| 5 | Underestimating Data Egress | Egress fees add up faster than compute | Data transfer line items spike monthly | VPC endpoints + region co-location |
| 6 | Ignoring Vendor Lock-in Risk | Switching costs explode over time | All workloads on a single provider | Adopt portable abstractions (K8s, Terraform) |
| 7 | Over-Provisioning Resources | Paying for idle CPU/RAM | Avg CPU utilization <20% | Right-sizing + Compute Optimizer |
| 8 | Skipping Reserved Instances & Savings Plans | On-demand premium for predictable workloads | No commitments in billing dashboard | Analyze 3-month usage → commit on stable workloads |
| 9 | Misjudging Storage Costs | Wrong storage class for access pattern | S3 Standard used for rarely accessed data | Enable S3 Intelligent-Tiering |
| 10 | Neglecting to Decommission Resources | Paying for forgotten resources | Unattached EBS volumes, stopped EC2 | Weekly idle resource audit + automation |
| 11 | Overlooking Software Licensing | BYOL vs license-included confusion | Duplicate license charges | License inventory before migration |
| 12 | No Monitoring or Optimization Loop | Waste compounds undetected | No cost anomaly alerts configured | Enable AWS Cost Anomaly Detection / Azure Budgets |
| 13 | Poor Backup & DR Planning | Over-replicated data or recovery failures | DR spend exceeds 15% of total cloud bill | Tiered backup strategy with lifecycle policies |
| 14 | Not Using Cloud Cost Tools | Invisible spend patterns | No regular Cost Explorer reports | Schedule weekly cost review cadence |
| 15 | Inadequate Skills & Expertise | Wrong decisions compound into structural debt | Manual fixes, repeated incidents | Engage a certified cloud partner |
| 16 | Missing Governance & Tagging | No cost attribution = no accountability | Untagged resources >30% of bill | Enforce tagging policy via IaC |
| 17 | Ignoring Security & Compliance Costs | Breaches cost far more than prevention | No WAF, no encryption at rest | Security baseline as part of onboarding |
| 18 | Missing Hidden Fees | NAT, cross-AZ, IPv4, log retention surprises | Unexplained line items in billing | Detailed billing breakdown monthly |
| 19 | Not Leveraging Provider Discounts | Paying full price unnecessarily | No EDP, PPA, or partner program enrollment | Work with an AWS/Azure/GCP partner for pricing |
| 20 | No FinOps Operating Cadence | Cost decisions made reactively | No monthly cloud cost review meeting | Adopt FinOps Foundation operating model |
Traps 1–4: Migration Strategy Mistakes That Set the Wrong Foundation
Cloud cost problems often originate at the very first decision: how to migrate. Poor migration strategy creates structural inefficiencies that become exponentially harder and more expensive to fix after go-live.
Trap 1 – The “Lift and Shift” Approach
Migrating existing infrastructure to the cloud without architectural changes — commonly called “lift and shift” — is the single most widespread source of cloud cost overruns. Cloud economics reward cloud-native design. When you move an on-premises architecture unchanged, you keep all of its inefficiencies while adding cloud-specific cost layers.
A typical example: an on-premises database server running at 15% utilization, provisioned for peak load. In a data center, that idle capacity has no additional cost. In AWS or Azure, you pay for the full instance 24/7. That same pattern repeated across 50 services can double your effective cloud spend versus what a refactored equivalent would cost.
The right approach is “refactoring” — redesigning or partially rewriting applications to use cloud-native services such as managed databases, serverless compute, and event-driven architectures. Refactoring does require upfront investment, but it consistently delivers 30–60% lower steady-state costs compared to lift-and-shift.
Risk: High compute costs; pays cloud prices for on-prem design decisions
Signal: Low CPU/memory utilization (<25%) on most instances post-migration
Fix: Identify the top 5 cost drivers; prioritize those for refactoring in Sprint 1
Trap 2 – Choosing the Wrong IT Architecture
Architecture decisions made before or during migration determine your cost ceiling for years. A monolithic deployment that requires a large EC2 instance to function at all will always cost more than a microservices-based design that can scale individual components independently. Similarly, choosing synchronous service-to-service calls when asynchronous queuing would work causes unnecessary instance sizing to handle peak concurrency.
Poor architectural choices also create security and scalability gaps that require expensive remediation. We have seen clients spend more fixing architectural decisions in year two than their original migration cost.
What to do: Conduct a formal architecture review before migration. Map how services interact, identify coupling points, and evaluate whether managed cloud services (RDS, SQS, ECS Fargate, Lambda) can replace self-managed components. Seek an independent review — internal teams often have blind spots around the architectures they built.
Risk: Expensive rework; environments that don’t scale without large instance upgrades
Signal: Manual vertical scaling during traffic events; frequent infrastructure incidents
Fix: Infrastructure audit pre-migration with explicit architecture recommendations
Trap 3 – Overreliance on Enterprise Editions
Many organizations default to enterprise tiers of cloud services and SaaS tools without validating whether standard editions cover their actual requirements. Enterprise editions can cost 3–5× more than standard equivalents while delivering features that 80% of teams never activate.
This is especially common in managed database services, monitoring platforms, and identity management. A 50-person engineering team paying for enterprise database licensing at $8,000/month when a standard tier at $1,200/month would meet their SLA requirements is a straightforward optimization many teams overlook.
What to do: Build a license inventory as part of your migration plan. Map every service tier to actual feature usage. Apply enterprise editions only where specific features — such as advanced security controls or SLA guarantees — are genuinely required. Use non-production environments to validate that standard tiers meet your needs before committing.
Risk: 3–5× cost premium for unused enterprise features
Signal: Enterprise licenses deployed uniformly across all environments including dev/staging
Fix: Feature-usage audit per service; downgrade where usage doesn’t justify tier
Trap 4 – Uncontrolled Capacity Planning
Capacity needs differ dramatically by workload type. Some workloads are constant, some linear, some follow exponential growth curves, and some are highly seasonal (e-commerce spikes, payroll runs, end-of-quarter reporting). Without workload-specific capacity models, teams either over-provision to be safe — paying for idle capacity — or under-provision and face service disruptions that result in emergency spending.
A practical example: an e-commerce platform provisioning its peak Black Friday capacity year-round would spend roughly 4× more than a platform using autoscaling with predictive scaling policies and spot instances for burst capacity.
What to do: Model capacity by workload pattern type. Use cloud-native autoscaling with predictive policies (AWS Auto Scaling predictive scaling, Azure VMSS autoscale) for variable workloads. Use Reserved Instances only for the steady-state baseline that you can reliably forecast 12 months out. Review capacity assumptions quarterly.
Risk Persistent over-provisioning or costly emergency scaling events
Signal Flat autoscaling policies; no predictive scaling configured
Fix Workload classification + autoscaling policy tuning + quarterly capacity review
Traps 5–9: Architectural Decisions That Create Structural Waste
Even with a sound migration strategy, specific architectural choices can lock in cost inefficiencies. These traps are particularly dangerous because they are not visible in compute cost reports — they hide in network fees, storage charges, and pricing tiers.
Trap 5 – Underestimating Data Transfer and Egress Costs
Data transfer costs are the most consistently underestimated line item in cloud budgets. AWS charges $0.09 per GB for standard egress from most regions. Azure and GCP follow similar models. For an application that moves 100 TB of data monthly between services, regions, or to end users, that’s $9,000 per month from egress alone — often invisible during initial cost modeling.
Beyond external egress, cross-Availability Zone (cross-AZ) data transfer is a hidden cost that catches many teams by surprise. In AWS, cross-AZ traffic costs $0.01 per GB in each direction. A microservices application making frequent cross-AZ calls can generate thousands of dollars in monthly cross-AZ fees that appear in no single obvious dashboard item.
NAT Gateway charges are another overlooked trap: at $0.045 per GB processed (AWS), a data-heavy workload can generate NAT costs that rival compute. Use VPC Interface Endpoints or Gateway Endpoints for S3, DynamoDB, SQS, and other AWS-native services to eliminate unnecessary NAT Gateway traffic entirely.
Risk $0.09+/GB egress; cross-AZ and NAT fees compound quickly at scale
Signal Data transfer line items represent >15% of total cloud bill
Fix Deploy VPC endpoints; co-locate communicating services in same AZ; use CDN for user-facing egress
Trap 6 – Overlooking Vendor Lock-in Risks
Vendor lock-in is not merely an architectural concern — it is a cost risk. When 100% of your workloads are tightly coupled to a single cloud provider’s proprietary services, your negotiating position on pricing is zero, migration away from bad pricing agreements is prohibitively expensive, and you are exposed to any pricing changes the provider makes.
Using open standards — Kubernetes for container orchestration, Terraform or Pulumi for infrastructure as code, PostgreSQL-compatible databases rather than proprietary variants — preserves optionality without meaningful cost or performance tradeoffs for most workloads. The Cloud Native Computing Foundation (CNCF) maintains an extensive ecosystem of portable tooling that reduces lock-in risk while supporting enterprise-grade requirements.
Risk Zero pricing leverage; multi-year migration cost if you need to switch
Signal All infrastructure uses proprietary managed services with no portable alternatives
Fix Adopt open standards (K8s, Terraform, open-source databases) for new workloads
Trap 7 – Over-Provisioning Resources
Over-provisioning — allocating more compute, memory, or storage than workloads actually need — is one of the most common and most correctable sources of cloud waste. Industry benchmarks consistently show that average CPU utilization across cloud environments sits below 20%. That means 80% of compute capacity is idle on an average day.
AWS Compute Optimizer analyzes actual utilization metrics and generates rightsizing recommendations. In a typical engagement, Gart architects find that 30–50% of EC2 instances are candidates for downsizing by one or more instance sizes, often without any measurable performance impact. The same pattern applies to managed database instances, where default sizing is frequently 2× what the actual workload requires.
For Kubernetes workloads, idle node waste is a particularly common issue. If EKS nodes run at <40% average utilization, Fargate profiles for low-utilization pods can reduce compute costs significantly by charging only for the CPU and memory actually requested by each pod — not the entire node.
Risk Paying for 80% idle capacity on average; compounds across every service
Signal Average CPU <20%; CloudWatch showing consistent low utilization
Fix Run AWS Compute Optimizer or Azure Advisor; right-size top 10 cost drivers first
Trap 9 – Skipping Reserved Instances and Savings Plans
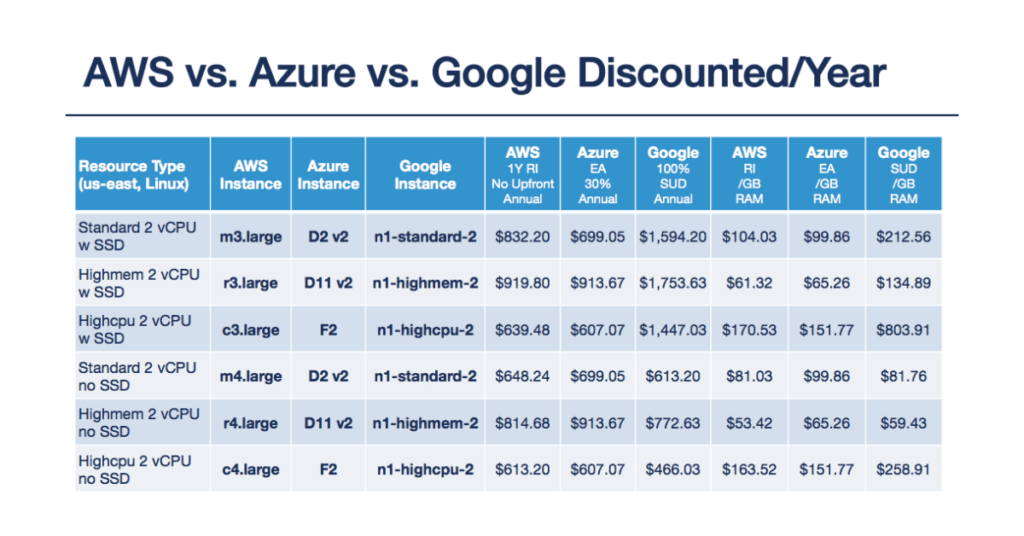
On-demand pricing is the most expensive way to run predictable workloads. AWS Reserved Instances and Compute Savings Plans offer discounts of up to 72% versus on-demand rates for 1- or 3-year commitments — discounts that are documented in AWS’s official pricing documentation. Azure Reserved VM Instances and GCP Committed Use Discounts offer comparable savings.
Despite the size of these savings, many organizations run the majority of their workloads on on-demand pricing, either because they lack the forecasting confidence to commit or because no one has owned the decision. For production workloads with predictable usage — databases, core application servers, monitoring stacks — there is almost never a good reason to use on-demand pricing exclusively.
Practical approach: Analyze your last 90 days of usage. Identify the minimum baseline usage across all instance types — that is your “floor.” Commit Reserved Instances to cover that floor. Use Savings Plans (more flexible, applying across instance families and regions) to cover the next layer of predictable usage. Keep only genuine burst capacity on on-demand or Spot.
Risk Paying 72% more than necessary for stable workloads
Signal No active reservations or savings plans in billing console
Fix 90-day usage analysis → commit on the steady-state baseline; layer Savings Plans on top
Trap 10 – Misjudging Data Storage Costs
Storage costs are deceptively easy to ignore when an organization is small — and surprisingly painful when data volumes grow. Three specific patterns create disproportionate storage costs:
Wrong storage class. Storing rarely-accessed data in S3 Standard at $0.023/GB when S3 Glacier Instant Retrieval costs $0.004/GB is a 6× overspend on archival data. S3 Intelligent-Tiering solves this automatically for access patterns you cannot predict — it moves objects between tiers based on access history and can deliver savings of 40–95% on archival content.
EBS volume type mismatch. Most workloads still use gp2 EBS volumes by default. Migrating to gp3 reduces cost by approximately 20% ($0.10/GB vs $0.08/GB in us-east-1) while delivering better baseline IOPS. A team with 5 TB of EBS saves $100/month with a configuration change that takes minutes.
Observability retention bloat. CloudWatch Log Groups with retention set to “Never Expire” accumulate months or years of logs that no one reviews. Setting a 30- or 90-day retention policy on non-compliance logs is one of the simplest cost reductions available and can represent significant monthly savings for data-heavy applications.
Risk Up to 6× overpayment on archival storage; compounding log retention costs
Signal All S3 data in Standard class; CloudWatch retention set to “Never”
Fix Enable Intelligent-Tiering; migrate EBS to gp3; set log retention policies immediately
Traps 10–15: Operational Habits That Drain the Budget Silently
Operational cloud cost traps are the result of what teams do (and don’t do) day to day. They are often smaller individually than architectural traps, but they compound quickly and are the most common source of the “unexplained” portion of cloud bills.
Trap 10 – Neglecting to Decommission Unused Resources
Cloud environments accumulate ghost resources — stopped EC2 instances, unattached EBS volumes, unused Elastic IPs, orphaned load balancers, forgotten RDS snapshots — faster than most teams realize. Each item carries a small individual cost, but across a mature cloud environment these can represent 10–20% of the total bill.
Starting from February 2024, AWS charges $0.005 per public IPv4 address per hour — approximately $3.65/month per address. An environment with 200 public IPs that have never been audited pays $730/month in IPv4 fees alone, often without anyone noticing. Transitioning to IPv6 where supported eliminates this cost entirely.
Best practice: Schedule a monthly idle-resource audit using AWS Trusted Advisor, Azure Advisor, or a dedicated FinOps tool. Automate shutdown of non-production resources outside business hours. Set lifecycle policies on EBS snapshots, RDS snapshots, and ECR images to automatically prune old versions.
Risk 10–20% of bill in ghost resources; IPv4 fees accumulate invisibly
Signal Unattached EBS volumes; stopped instances still appearing in billing
Fix Automated weekly cleanup script + lifecycle policies on snapshots and images
Trap 11 – Overlooking Software Licensing Costs
Cloud migration can inadvertently increase software licensing costs in two ways: activating license-included instance types when you already hold bring-your-own-license (BYOL) agreements, or losing license portability by moving to managed services that bundle licensing at a premium.
Windows Server and SQL Server licenses are particularly high-value areas. Running SQL Server Enterprise on a license-included RDS instance can cost significantly more than using a BYOL license on an EC2 instance with an optimized configuration. Understanding your existing software agreements before migration — and mapping them to cloud deployment options — can save substantial amounts annually.
Risk Duplicate licensing costs; paying for bundled licenses when BYOL applies
Signal No license inventory reviewed before migration; license-included instances for Windows/SQL Server
Fix Software license audit pre-migration; map existing agreements to BYOL eligibility in cloud
Trap 12 – Failing to Monitor and Optimize Usage Continuously
Cloud cost optimization is not a one-time project — it is a continuous operational practice. Without ongoing monitoring, cost anomalies go undetected, new services are provisioned without review, and seasonal workloads retain peak-period sizing long after demand has subsided.
AWS Cost Anomaly Detection, Azure Cost Management alerts, and GCP Budget Alerts all provide free anomaly detection capabilities that most organizations never configure. Setting budget thresholds with alert notifications takes less than an hour and provides immediate visibility into unexpected spend spikes.
Recommended monitoring stack: cloud-native cost dashboards (Cost Explorer / Azure Cost Management) for historical analysis, budget alerts for real-time anomaly detection, and a weekly team review of the top 10 cost drivers by service.
Risk Waste compounds for months before anyone notices
Signal No cost anomaly alerts configured; no regular cost review meeting
Fix Enable anomaly detection; schedule weekly cost review; assign cost ownership per team
Trap 13 – Inadequate Backup and Disaster Recovery Planning
Backup and disaster recovery strategies that aren’t cost-optimized can inflate cloud bills significantly. Common mistakes include retaining identical backup copies across multiple regions for all data regardless of criticality, keeping backups indefinitely without a lifecycle policy, and running full active-active DR environments for workloads where a simpler warm standby or pilot light approach would meet RTO/RPO requirements.
Cost-effective DR design starts with classifying workloads by criticality tier. Not every application needs a hot standby. Many workloads with RTO requirements of 4+ hours can be recovered efficiently from S3-based backups at a fraction of the cost of a full multi-region active replica. For S3, enabling lifecycle rules that transition backup data to Glacier Deep Archive after 30 days reduces storage cost by up to 95%.
Risk DR costs exceeding 15–20% of total cloud bill for non-critical workloads
Signal Uniform DR strategy applied to all workloads regardless of criticality tier
Fix Workload criticality classification → tiered DR strategy → S3 Glacier lifecycle policies
Trap 14 – Ignoring Cloud Cost Management Tools
Every major cloud provider ships cost management and optimization tools that the majority of organizations either ignore or underuse. AWS Cost Explorer, AWS Compute Optimizer, AWS Trusted Advisor, Azure Advisor, and GCP Recommender collectively surface rightsizing recommendations, reserved capacity suggestions, and idle resource reports — all free of charge.
Third-party FinOps platforms (CloudHealth, Apptio Cloudability, Spot by NetApp) provide cross-provider views and more sophisticated anomaly detection for multi-cloud environments. For organizations spending more than $50K/month on cloud, the ROI on a dedicated FinOps tool typically exceeds 10:1 within the first quarter.
Risk Missing savings recommendations that providers generate automatically
Signal No regular review of Trusted Advisor / Azure Advisor recommendations
Fix Enable all native cost tools; schedule weekly review of top recommendations
Trap 15 – Lack of Appropriate Cloud Skills
Cloud cost optimization requires specific expertise that is not automatically present in teams that migrate from on-premises environments. Teams without cloud-native skills tend to default to familiar patterns — large VMs, manual scaling, on-demand pricing — that systematically cost more than cloud-optimized equivalents.
The skill gap is not just about knowing which services exist. It is about understanding the cost implications of architectural decisions in real time — knowing that choosing a NAT Gateway over a VPC endpoint has a measurable monthly cost, or that a managed database defaults to a larger instance tier than necessary for a given workload.
Gart’s approach:We embed a cloud architect alongside your team during the first 90 days post-migration. That direct knowledge transfer prevents the most expensive mistakes during the period when cloud spend is most volatile.
Risk Repeated costly mistakes; structural technical debt from uninformed decisions
Signal Manual infrastructure changes; frequent cost surprises; no IaC adoption
Fix Engage a certified cloud partner for the migration and 90-day post-migration period
Traps 16–20: Governance and FinOps Failures That Undermine Everything Else
The most technically sophisticated cloud architecture can still generate runaway costs without adequate governance. These final five traps operate at the organizational level — they are about processes, policies, and culture as much as technology.
Trap 16 – Missing Governance, Tagging, and Cost Policies
Without a resource tagging strategy, cloud cost reports show you what you’re spending but not who is spending it, on what, or why. This makes accountability impossible and optimization very difficult. Untagged resources in a mature cloud environment commonly represent 30–50% of the total bill — a figure that makes cost attribution to business units, projects, or environments nearly impossible.
Effective tagging policies include mandatory tags enforced at provisioning time via Service Control Policies (AWS), Azure Policy, or IaC templates. Minimum viable tags: environment (production/staging/dev), team, project, and cost-center. Resources that fail tagging checks should be prevented from provisioning in production.
Governance beyond tagging includes spending approval workflows for new service provisioning, budget alerts per team, and quarterly cost reviews that compare actual vs. planned spend by business unit.
Risk No cost accountability; optimization impossible without attribution
Signal >30% of resources untagged; no per-team budget visibility
Fix Enforce tagging at IaC level; SCPs/Azure Policy for tag compliance; team-level budget dashboards
Trap 17 – Ignoring Security and Compliance Costs
Under-investing in cloud security creates a different kind of cost trap: the cost of a breach or compliance failure vastly exceeds the cost of prevention. The average cost of a cloud data breach reached $4.9M in 2024 (IBM Cost of a Data Breach report). WAF, encryption at rest, secrets management, and compliance automation are not optional overhead — they are cost controls.
Security-related compliance requirements (SOC 2, HIPAA, GDPR, PCI DSS) also have cloud cost implications: they constrain which storage services, regions, and encryption configurations you can use. Understanding these constraints before architecture is finalized prevents expensive rework and compliance-driven re-migration.
For implementation guidance, the Linux Foundation and cloud provider security frameworks provide open standards for cloud security baselines that are both compliance-aligned and cost-efficient.
Risk Breach costs far exceed prevention investment; compliance rework is expensive
Signal No WAF; secrets in environment variables; no encryption at rest configured
Fix Security baseline as part of initial architecture; compliance audit before go-live
Trap 18 – Not Considering Hidden and Miscellaneous Costs
Beyond compute and storage, cloud bills contain dozens of smaller line items that collectively represent a significant portion of total spend. The most commonly overlooked hidden costs we see in client audits:
- Public IPv4 addressing: $0.005/hour per IP in AWS = $3.65/month per address. 100 addresses = $365/month that many teams have never noticed.
- Cross-AZ traffic: $0.01/GB in each direction. Microservices with chatty inter-service communication across AZs can generate thousands per month.
- NAT Gateway processing: $0.045/GB processed through NAT. Services that use NAT to reach AWS APIs instead of VPC endpoints pay this fee unnecessarily.
- CloudWatch log ingestion: $0.50 per GB ingested. Verbose application logging without sampling can generate large CloudWatch bills.
- Managed service idle time: RDS instances, ElastiCache clusters, and OpenSearch domains running 24/7 for development workloads that operate 8 hours/day.
Risk Cumulative hidden fees representing 10–25% of total bill
Signal Unexplained or unlabeled line items in billing breakdown
Fix Monthly detailed billing review; enable Cost Allocation Tags; use VPC endpoints to eliminate NAT fees
Trap 19 – Failing to Leverage Cloud Provider Discounts
Beyond Reserved Instances and Savings Plans, cloud providers offer several discount programs that most organizations never explore. AWS Enterprise Discount Program (EDP), Azure Enterprise Agreement (EA) pricing, and GCP Committed Use Discounts can deliver negotiated rates of 10–30% on overall spend for organizations with committed annual volumes.
Working with an AWS, Azure, or GCP partner can also unlock reseller discount arrangements and technical credit programs. Partners in the AWS Partner Network (APN) and Microsoft Partner Network can often pass on pricing that is not directly available to end customers. Gart’s AWS partner status allows us to structure engagements that include pricing advantages for qualifying clients — an arrangement that can save 5–15% of annual cloud spend independently of any architectural optimization.
Provider credit programs (AWS Activate for startups, Google for Startups, Microsoft for Startups) are also frequently overlooked by companies that don’t realize they qualify. Many Series A and Series B companies are still eligible for substantial credits.
Risk Paying full list price when negotiated rates of 10–30% are available
Signal No EDP, EA, or partner program enrollment; no credits applied
Fix Engage a cloud partner to assess discount program eligibility and negotiate pricing
Trap 20 – No FinOps Operating Cadence
The final and most systemic trap is the absence of an organized FinOps practice. FinOps — Financial Operations — is the cloud financial management discipline that brings financial accountability to variable cloud spend, enabling engineering, finance, and product teams to make informed trade-offs between speed, cost, and quality. The FinOps Foundation defines the framework that leading cloud-native organizations use to govern cloud economics.
Without a FinOps operating cadence, cloud cost optimization is reactive: teams respond to bill shock rather than preventing it. With FinOps, cost optimization becomes embedded in engineering workflows — part of sprint planning, architecture review, and release processes.
Core FinOps practices to adopt immediately:
- Weekly cloud cost review meeting with engineering leads and finance representative
- Cost forecasts updated monthly by service and team
- Budget alerts set at 80% and 100% of monthly targets
- Anomaly detection enabled on all accounts
- Quarterly optimization sprints with dedicated engineering time for cost improvements
Risk All other 19 traps compound without FinOps to catch them
Signal No regular cost review; cost surprises discovered at invoice receipt
Fix Adopt FinOps Foundation operating model; assign cloud cost owner per account.
Cloud Cost Optimization Checklist for Engineering Leaders
Use this checklist to rapidly assess where your cloud environment stands across the four cost-control layers. Items you cannot check today represent your highest-priority optimization opportunities.
Cloud Cost Optimization Checklist
Migration & Architecture
Compute & Capacity
Operations & Monitoring
Governance & FinOps
Stop Guessing. Start Optimizing.
Gart’s cloud architects have helped 50+ organizations recover 20–40% of their cloud spend — without sacrificing performance or reliability.
🔍 Cloud Cost Audit
We analyze your full cloud bill and deliver a prioritized savings roadmap within 5 business days.
🏗️ Architecture Review
Identify structural inefficiencies like over-provisioning and redesign for efficiency without disruption.
📊 FinOps Implementation
Operating cadence, tagging governance, and cost dashboards to keep cloud spend under control.
☁️ Ongoing Optimization
Monthly or quarterly retainers that keep your spend aligned with business goals as workloads evolve.









